Get the free Implementing ENISAs cyber security plan in the European ...
Show details
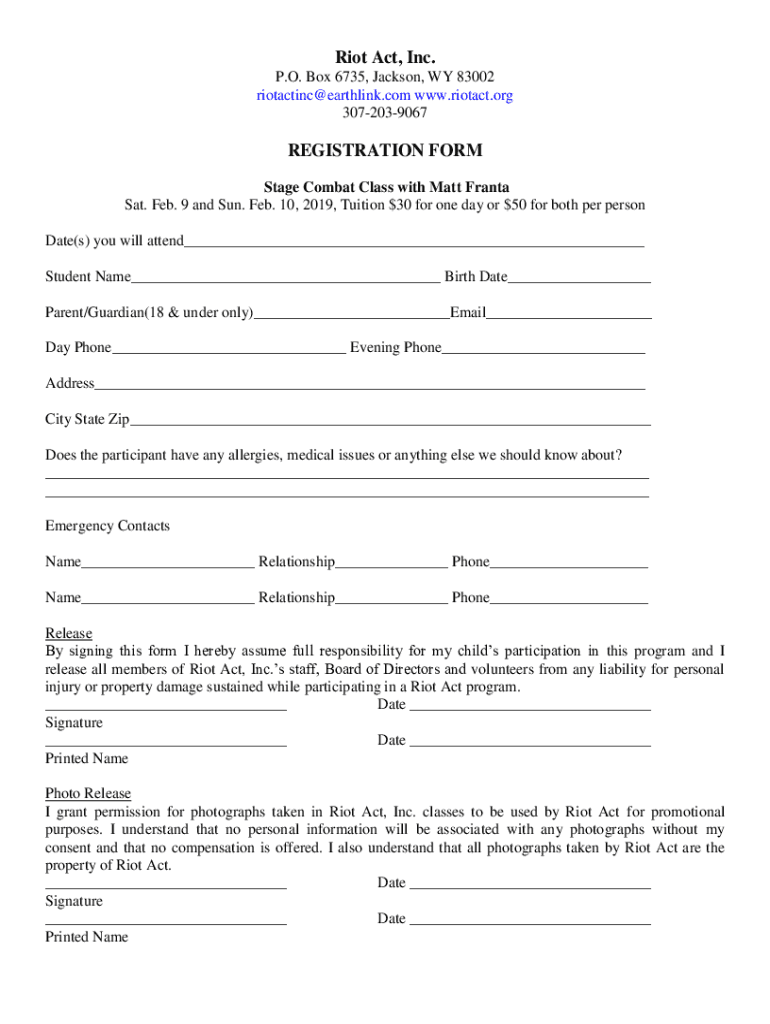
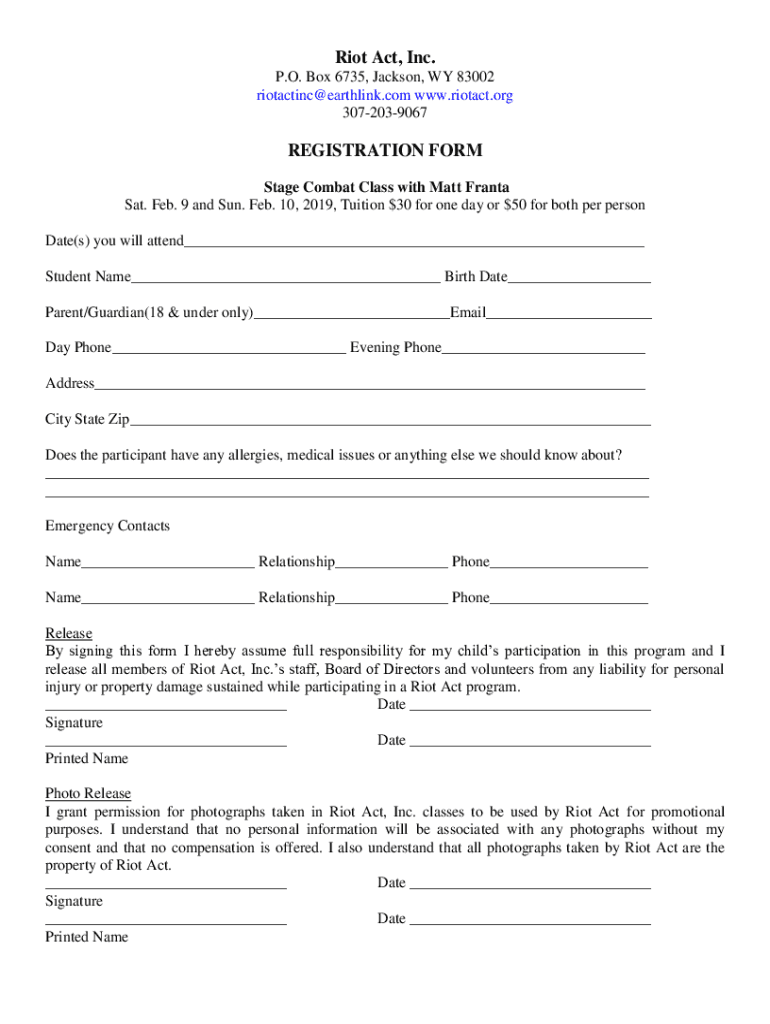
Riot Act, Inc. P.O. Box 6735, Jackson, WY 83002 rotating earthlink.com www.riotact.org 3072039067REGISTRATION FORM Stage Combat Class with Matt Fran ta Sat. Feb. 9 and Sun. Feb. 10, 2019, Tuition
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign implementing enisas cyber security

Edit your implementing enisas cyber security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your implementing enisas cyber security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing implementing enisas cyber security online
In order to make advantage of the professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit implementing enisas cyber security. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out implementing enisas cyber security

How to fill out implementing enisas cyber security
01
To fill out implementing enisas cyber security, follow these steps:
02
Start by understanding the information security requirements provided by ENISA (European Union Agency for Cybersecurity).
03
Analyze your organization's current cyber security practices and identify gaps or areas that need improvement.
04
Develop a cyber security implementation plan based on the ENISA guidelines and your organization's specific needs.
05
Implement technical and organizational measures to protect your information assets, including securing networks, implementing secure software development practices, and establishing access controls.
06
Continuously monitor and assess the effectiveness of your cyber security controls and make necessary adjustments.
07
Regularly review and update your cyber security policies and practices to stay current with evolving threats and technologies.
08
Educate and train your employees on cyber security best practices to promote a culture of security awareness.
09
Consider engaging a third-party security auditor to assess and validate the effectiveness of your cyber security implementation.
10
Document and maintain records of your cyber security activities to demonstrate compliance and support ongoing improvement.
11
Stay informed about the latest cyber security trends, guidelines, and regulations to ensure your implementation remains up to date.
Who needs implementing enisas cyber security?
01
Any organization, both public and private, that handles sensitive or critical information and wants to protect it from cyber threats, needs to implement ENISA's cyber security guidelines.
02
This includes government agencies, financial institutions, healthcare organizations, retail and e-commerce businesses, energy and utility companies, and any other entity that relies on information technology for its operations.
03
Implementing ENISA's cyber security guidelines can help organizations prevent data breaches, protect customer information, ensure regulatory compliance, and maintain business continuity in the face of cyber attacks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send implementing enisas cyber security for eSignature?
Once your implementing enisas cyber security is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How do I edit implementing enisas cyber security online?
pdfFiller not only lets you change the content of your files, but you can also change the number and order of pages. Upload your implementing enisas cyber security to the editor and make any changes in a few clicks. The editor lets you black out, type, and erase text in PDFs. You can also add images, sticky notes, and text boxes, as well as many other things.
Can I create an electronic signature for signing my implementing enisas cyber security in Gmail?
Use pdfFiller's Gmail add-on to upload, type, or draw a signature. Your implementing enisas cyber security and other papers may be signed using pdfFiller. Register for a free account to preserve signed papers and signatures.
What is implementing enisas cyber security?
Implementing ENISA's cyber security refers to adopting and applying the guidelines and frameworks established by the European Union Agency for Cybersecurity (ENISA) to enhance an organization's cyber resilience and security posture.
Who is required to file implementing enisas cyber security?
Entities operating within the EU's critical infrastructure sectors, digital service providers, and organizations subject to the EU's General Data Protection Regulation (GDPR) may be required to file implementing ENISA's cyber security measures.
How to fill out implementing enisas cyber security?
Filling out the implementing ENISA's cyber security requires organizations to assess their current security measures, identify gaps based on ENISA's recommendations, and document their compliance efforts and strategies in an official report.
What is the purpose of implementing enisas cyber security?
The purpose is to ensure a higher level of security across the EU, mitigate risks related to cyber threats, enhance cooperation among member states, and protect critical infrastructure and services.
What information must be reported on implementing enisas cyber security?
Organizations must report on their current security measures, risk assessments, incident response protocols, and any gaps identified with reference to ENISA’s recommendations.
Fill out your implementing enisas cyber security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Implementing Enisas Cyber Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.