Get the free Key Policy and Request FormsUniversity of Tennessee at ...
Show details
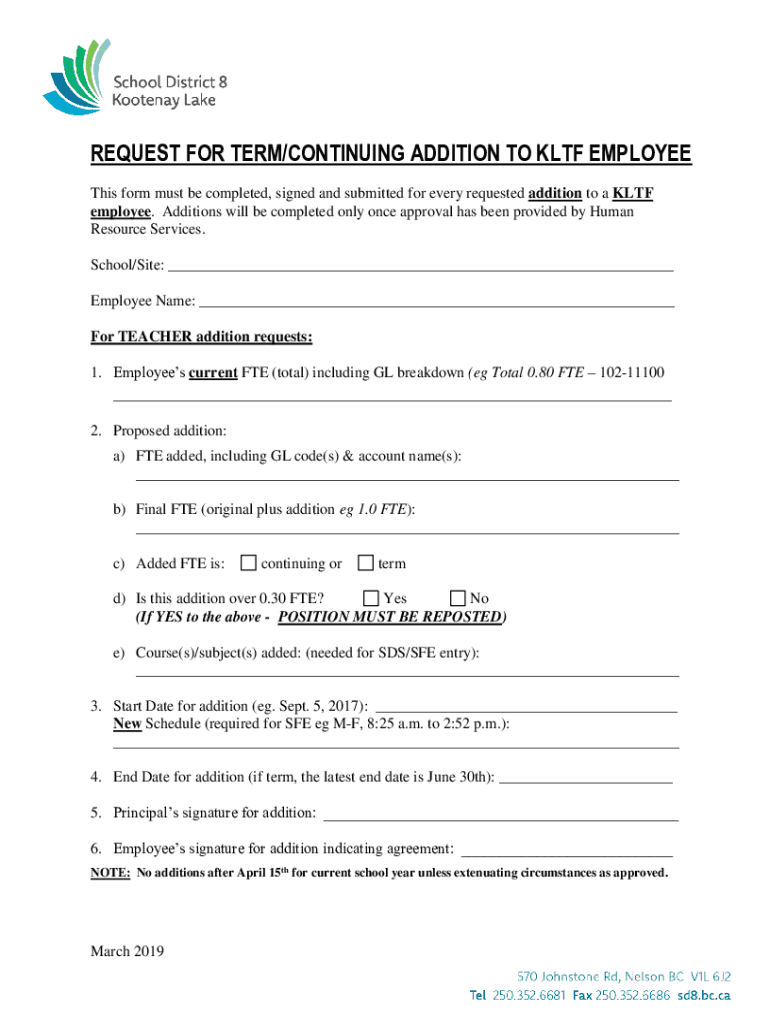
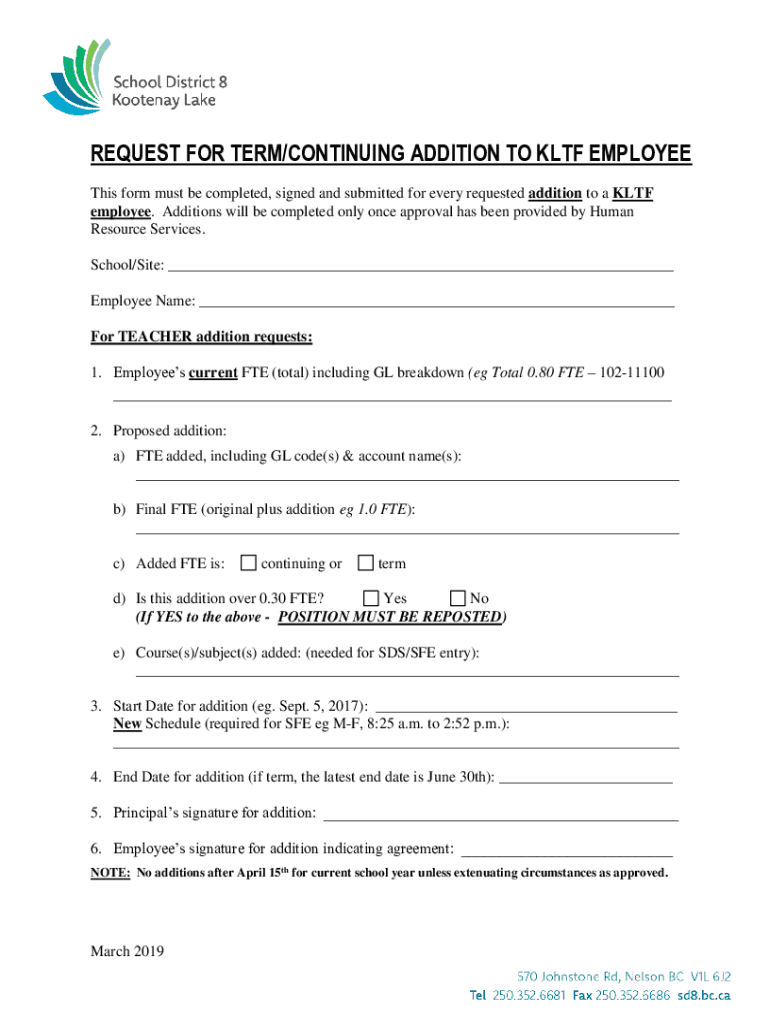
REQUEST FOR TERM/CONTINUING ADDITION TO LTF EMPLOYEE This form must be completed, signed and submitted for every requested addition to an LTF employee. Additions will be completed only once approval
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign key policy and request

Edit your key policy and request form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your key policy and request form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit key policy and request online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit key policy and request. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out key policy and request

How to fill out key policy and request
01
To fill out a key policy and request, follow these steps:
02
Start by downloading the key policy and request form from the official website or obtaining a copy from the appropriate authority.
03
Fill in your personal information accurately, including your full name, address, contact details, and any other required information.
04
Provide details about the specific key(s) you are requesting, such as the purpose of the key(s), the location where they will be used, and any relevant identification numbers.
05
Indicate the duration for which you need the key(s) and any conditions or restrictions associated with their use.
06
Sign and date the form, ensuring that all the provided information is correct and complete.
07
Attach any supporting documents or additional information that may be requested, such as identification proof or authorization letters.
08
Submit the filled-out form and any required documentation to the designated authority or department responsible for key issuance and policy implementation.
09
Follow up with the authorities if necessary to track the status of your request and obtain the approved key policy, if applicable.
Who needs key policy and request?
01
Key policy and request forms are typically required by individuals or entities who need authorized access to restricted areas, facilities, or resources.
02
Some examples of who may need a key policy and request include:
03
- Employees or staff members who require access to secure areas within an organization, such as server rooms or executive offices.
04
- Contractors or service providers who need temporary access to specific premises or equipment.
05
- Students or researchers who require keys to laboratories or research facilities.
06
- Building or property managers responsible for granting access to tenants or authorized personnel.
07
- Government agencies or law enforcement organizations managing key distribution for law enforcement or emergency purposes.
08
It is important to consult the specific policies and guidelines of the organization or authority you are dealing with to determine if a key policy and request form is required.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send key policy and request to be eSigned by others?
Once your key policy and request is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How do I edit key policy and request in Chrome?
Get and add pdfFiller Google Chrome Extension to your browser to edit, fill out and eSign your key policy and request, which you can open in the editor directly from a Google search page in just one click. Execute your fillable documents from any internet-connected device without leaving Chrome.
How do I complete key policy and request on an Android device?
On Android, use the pdfFiller mobile app to finish your key policy and request. Adding, editing, deleting text, signing, annotating, and more are all available with the app. All you need is a smartphone and internet.
What is key policy and request?
A key policy and request is a formal document submitted to inform relevant authorities about specific policies regarding the use and management of keys, usually in a financial or legal context.
Who is required to file key policy and request?
Individuals and entities that manage or administer keys, particularly in sectors like finance and real estate, are typically required to file a key policy and request.
How to fill out key policy and request?
To fill out the key policy and request, one must provide detailed information regarding the key management policies, including the purpose, procedures, and involved parties.
What is the purpose of key policy and request?
The purpose of the key policy and request is to ensure compliance with regulatory requirements and provide transparent information about key management practices.
What information must be reported on key policy and request?
Key information that must be reported includes the entity's name, address, the type of keys managed, policy descriptions, and procedures for key access and security.
Fill out your key policy and request online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Key Policy And Request is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.