Get the free CYBER POLICY RECOMMENDATIONS FOR THE NEW ADMINISTRATION
Show details
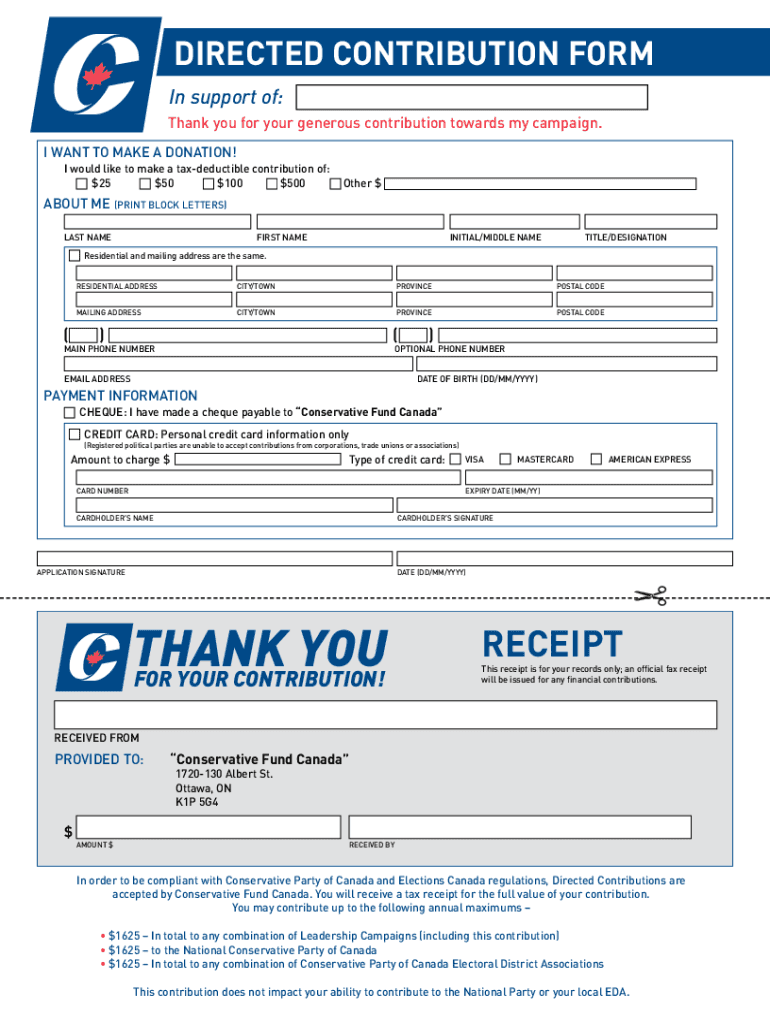
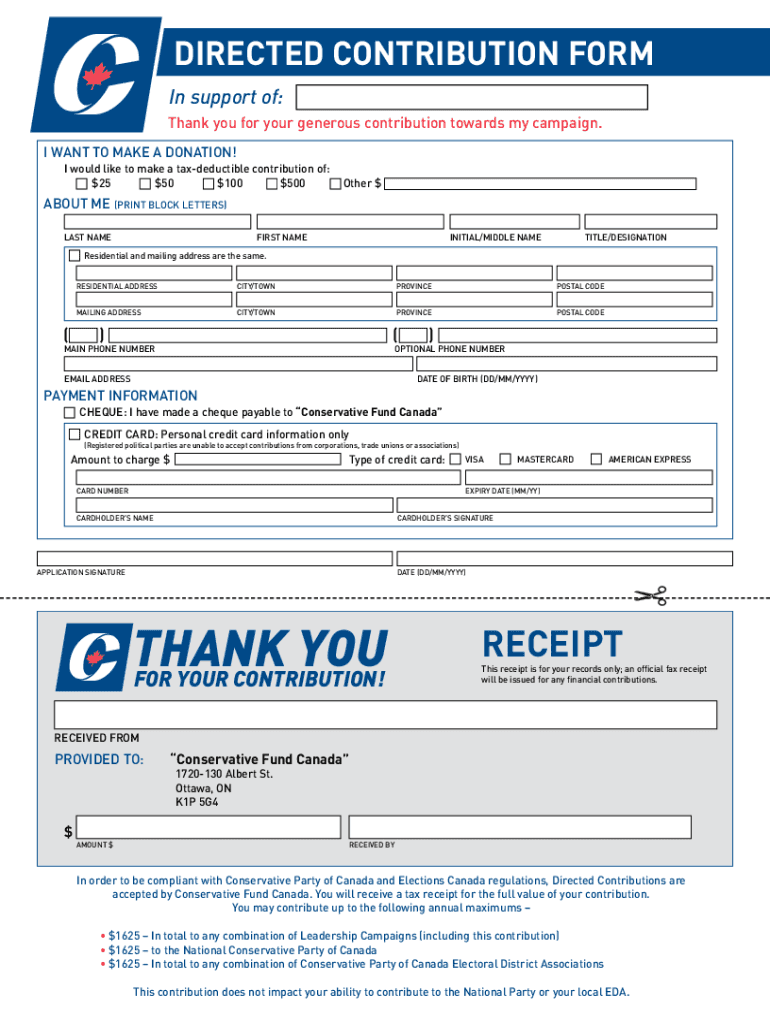
DIRECTED CONTRIBUTION FORM
In support of:
Thank you for your generous contribution towards my campaign.
I WANT TO MAKE A DONATION!
I would like to make a tax-deductible contribution of:
$$$$2550100500Other
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber policy recommendations for
Edit your cyber policy recommendations for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your cyber policy recommendations for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cyber policy recommendations for online
To use the professional PDF editor, follow these steps below:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit cyber policy recommendations for. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber policy recommendations for
How to fill out cyber policy recommendations for
01
Start by identifying the key stakeholders and decision-makers who will be involved in the cyber policy recommendations process.
02
Conduct a thorough assessment of the organization's current cybersecurity posture, including identifying any existing policies or frameworks that may already be in place.
03
Research best practices and industry standards for cyber policy recommendations to ensure that the proposed recommendations align with recognized guidelines.
04
Analyze the organization's specific needs and risks to develop tailored cyber policy recommendations that address vulnerabilities and potential threats.
05
Clearly articulate the objectives and goals of the cyber policy recommendations, keeping in mind the organization's mission and strategic priorities.
06
Develop a comprehensive action plan that outlines the implementation steps and timeline for the cyber policy recommendations.
07
Engage with stakeholders and decision-makers throughout the process to gather feedback, address concerns, and ensure buy-in and support for the proposed recommendations.
08
Finalize the cyber policy recommendations document, including any necessary supporting documentation or resources.
09
Communicate the cyber policy recommendations to relevant parties within the organization, providing clear guidance on the expectations and responsibilities for implementation.
10
Regularly review and update the cyber policy recommendations to adapt to evolving threats, technologies, and organizational needs.
Who needs cyber policy recommendations for?
01
Businesses of all sizes and industries can benefit from cyber policy recommendations to safeguard their digital assets, data, and customer information.
02
Government agencies and public institutions have a critical need for cyber policy recommendations to protect sensitive information and national security interests.
03
Non-profit organizations that handle donor information and personal data can gain valuable insights from cyber policy recommendations to ensure data privacy and compliance.
04
Educational institutions, including schools and universities, can benefit from cyber policy recommendations to secure student records, research data, and intellectual property.
05
Healthcare organizations need cyber policy recommendations to protect patient data and ensure compliance with healthcare regulations.
06
Financial institutions, such as banks and insurance companies, require robust cyber policy recommendations to prevent fraud, protect customer funds, and maintain trust in the financial system.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit cyber policy recommendations for online?
The editing procedure is simple with pdfFiller. Open your cyber policy recommendations for in the editor. You may also add photos, draw arrows and lines, insert sticky notes and text boxes, and more.
Can I edit cyber policy recommendations for on an iOS device?
You can. Using the pdfFiller iOS app, you can edit, distribute, and sign cyber policy recommendations for. Install it in seconds at the Apple Store. The app is free, but you must register to buy a subscription or start a free trial.
How do I fill out cyber policy recommendations for on an Android device?
Complete cyber policy recommendations for and other documents on your Android device with the pdfFiller app. The software allows you to modify information, eSign, annotate, and share files. You may view your papers from anywhere with an internet connection.
What is cyber policy recommendations for?
Cyber policy recommendations are for providing guidelines and best practices for organizations to prevent and respond to cyber threats.
Who is required to file cyber policy recommendations for?
Organizations in both the public and private sectors are required to file cyber policy recommendations.
How to fill out cyber policy recommendations for?
Cyber policy recommendations can be filled out by assessing current cybersecurity measures, identifying gaps, and implementing necessary changes.
What is the purpose of cyber policy recommendations for?
The purpose of cyber policy recommendations is to enhance cybersecurity posture, protect sensitive data, and mitigate cyber risks.
What information must be reported on cyber policy recommendations for?
Information such as current cybersecurity protocols, incident response procedures, and risk assessment findings must be reported on cyber policy recommendations.
Fill out your cyber policy recommendations for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Policy Recommendations For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















