Get the free Penetration testing for Basic Infrastructure Application form
Show details
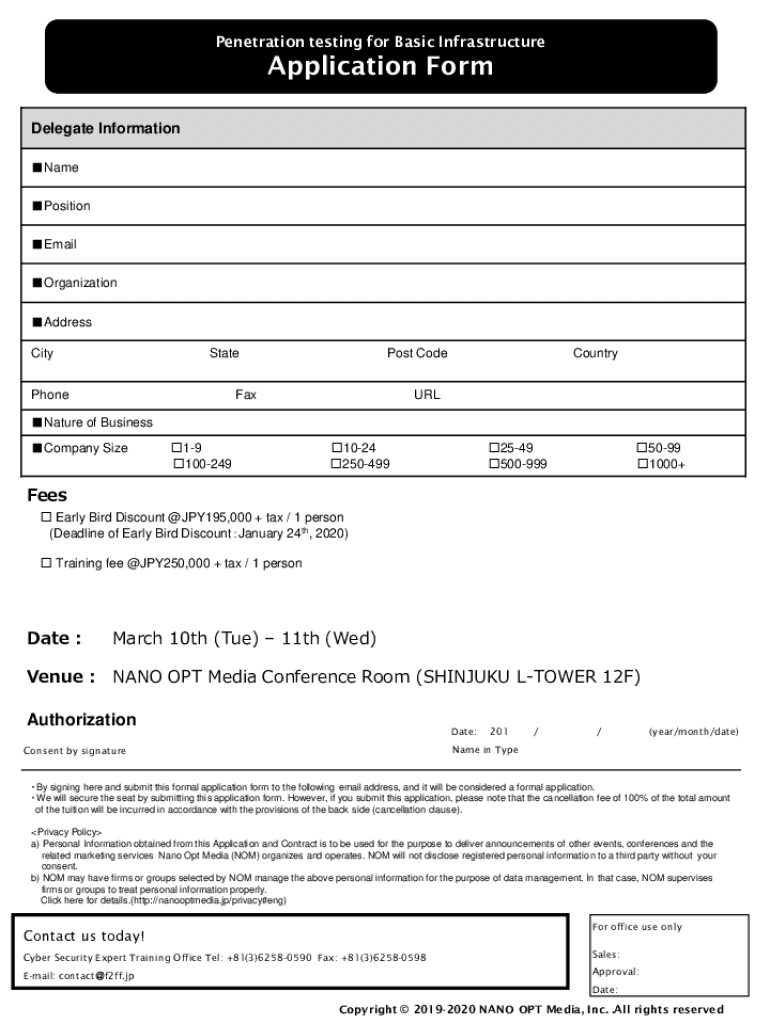
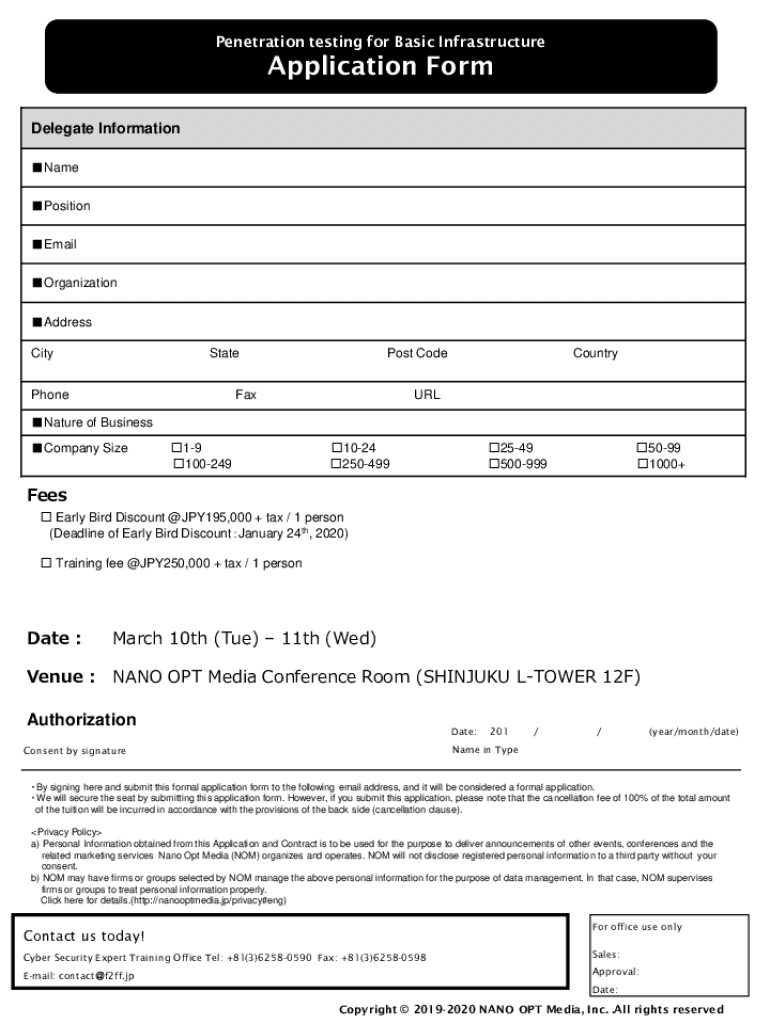
Penetration testing for Basic InfrastructureApplication Form Delegate Information Name Position Email Organization Address CityStatePhonePost CodeFaxCountryURLNature of Business Company Size19 1002491024
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign penetration testing for basic
Edit your penetration testing for basic form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your penetration testing for basic form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit penetration testing for basic online
Follow the steps below to use a professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit penetration testing for basic. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
It's easier to work with documents with pdfFiller than you can have ever thought. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out penetration testing for basic
How to fill out penetration testing for basic
01
To fill out penetration testing for basic, follow these steps:
02
Identify the scope and objectives of the penetration testing. Determine the systems, networks, or applications that need to be tested and define the goals of the testing.
03
Assemble a team of experienced penetration testers who have the necessary skills and knowledge to conduct the testing effectively.
04
Obtain permission from the organization or individuals who own the systems or networks to be tested. This is essential to ensure that the testing is legal and authorized.
05
Conduct a thorough reconnaissance to gather information about the target systems or networks. This may involve passive information gathering techniques like Internet searches or active techniques like network scanning.
06
Perform vulnerability scanning to identify potential weaknesses or vulnerabilities in the target systems or networks. Use automated tools or manual techniques to identify security flaws.
07
Exploit the identified vulnerabilities to gain unauthorized access or privileges. This step should be carried out with caution and only after obtaining proper authorization to avoid any legal issues.
08
Document and report the findings and recommendations. Prepare a detailed report that highlights the vulnerabilities found, their impact, and suggested remediation actions.
09
Share the findings and recommendations with the relevant stakeholders or decision-makers. Discuss the implications of the vulnerabilities and recommend mitigation strategies.
10
Follow up on the remediation actions to ensure that the identified vulnerabilities are addressed and fixed. Conduct retesting if necessary to verify the effectiveness of the remedial measures taken.
11
Continuously monitor and reassess the security posture of the tested systems or networks to stay proactive against emerging threats.
12
Note: It is highly recommended to engage with a professional penetration testing service provider or consult with experienced penetration testers for accurate and reliable results.
Who needs penetration testing for basic?
01
Penetration testing for basic is useful for various individuals or organizations, including:
02
- Small businesses or startups that want to assess the security of their IT infrastructure within a limited budget.
03
- Organizations that have recently implemented new systems, networks, or applications and want to ensure their security before they go live.
04
- IT administrators or security professionals who want to identify potential vulnerabilities in their existing systems or networks to prevent security breaches.
05
- Web application developers who want to test the security of their applications and uncover vulnerabilities or weaknesses that could be exploited by attackers.
06
- Individuals or organizations in regulated industries, such as finance or healthcare, that need to comply with industry-specific security standards and regulations.
07
- Companies that handle sensitive customer data and want to protect it from unauthorized access or data breaches.
08
Ultimately, anyone who wants to proactively assess and enhance the security of their digital assets can benefit from penetration testing for basic.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send penetration testing for basic for eSignature?
Once your penetration testing for basic is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How do I complete penetration testing for basic online?
pdfFiller has made it easy to fill out and sign penetration testing for basic. You can use the solution to change and move PDF content, add fields that can be filled in, and sign the document electronically. Start a free trial of pdfFiller, the best tool for editing and filling in documents.
How do I edit penetration testing for basic on an iOS device?
Yes, you can. With the pdfFiller mobile app, you can instantly edit, share, and sign penetration testing for basic on your iOS device. Get it at the Apple Store and install it in seconds. The application is free, but you will have to create an account to purchase a subscription or activate a free trial.
What is penetration testing for basic?
Penetration testing for basic is a method of evaluating the security of a computer system or network by simulating an attack from malicious outsiders.
Who is required to file penetration testing for basic?
Any organization that wants to assess and improve its security measures is required to conduct penetration testing for basic.
How to fill out penetration testing for basic?
Penetration testing for basic can be filled out by hiring a cybersecurity company to conduct the test and provide a detailed report on vulnerabilities and recommendations for improvement.
What is the purpose of penetration testing for basic?
The purpose of penetration testing for basic is to identify potential security weaknesses in a system or network before they can be exploited by cyber attackers.
What information must be reported on penetration testing for basic?
The report from penetration testing for basic must include details on the vulnerabilities found, their severity, and recommended mitigation strategies.
Fill out your penetration testing for basic online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Penetration Testing For Basic is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.



















