Get the free Methods for De-identification of PHIHHS.govWhat is Considered PHI Under HIPAA?Exampl...
Show details
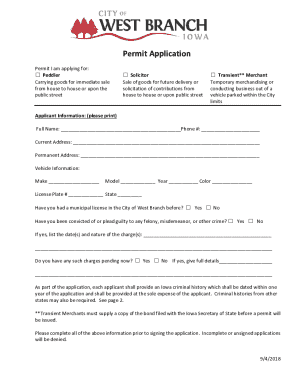
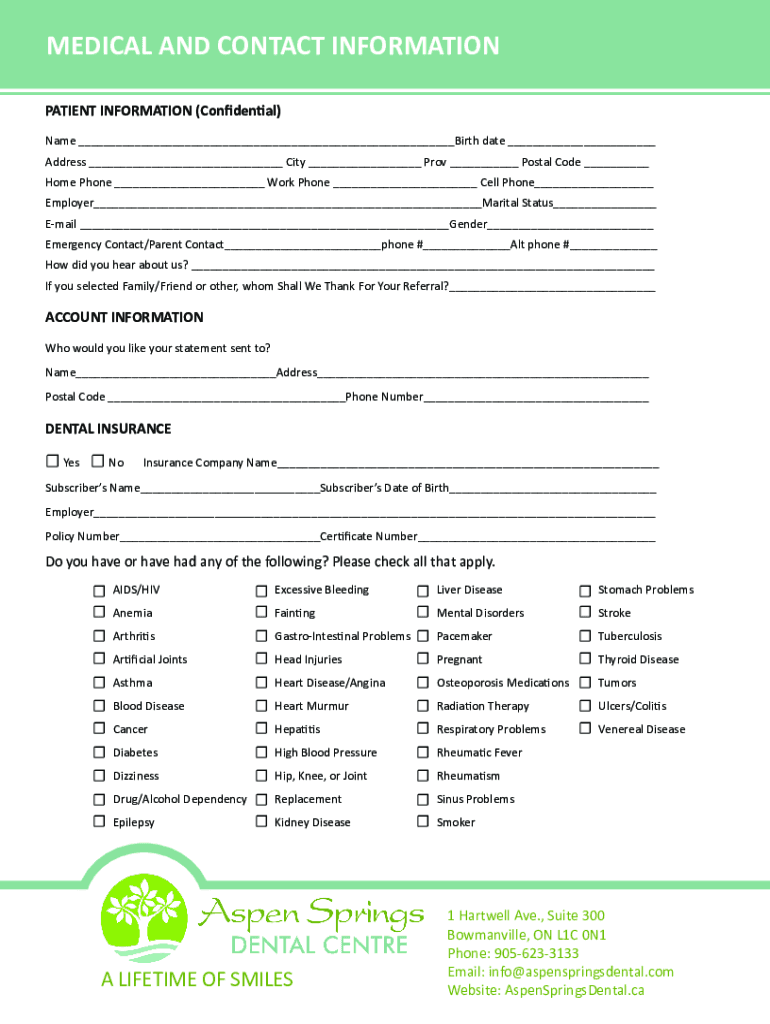
MEDICAL AND CONTACT INFORMATION PATIENT INFORMATION (Confidential) Name Birth date Address City Prov Postal Code Home Phone Work Phone Cell Phone Employer Marital Status Email Gender Emergency Contact/Parent
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign methods for de-identification of

Edit your methods for de-identification of form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your methods for de-identification of form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing methods for de-identification of online
Follow the guidelines below to benefit from a competent PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit methods for de-identification of. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out methods for de-identification of

How to fill out methods for de-identification of
01
To fill out methods for de-identification, follow these steps:
02
Identify the sensitive information: Determine the data elements that need to be de-identified, such as names, addresses, social security numbers, etc.
03
Choose an appropriate de-identification method: Select a method that best suits your needs, such as encryption, masking, tokenization, or generalization.
04
Define the de-identification process: Specify the steps involved in applying the chosen method, including any algorithms or techniques to be used.
05
Implement the de-identification method: Write the code or configure the software application to perform the de-identification process as defined.
06
Test the effectiveness: Validate the de-identification method by running thorough tests and ensuring that the sensitive information is properly masked or anonymized.
07
Document the method: Document the details of the de-identification method, including its purpose, implementation, and any associated risks or limitations.
08
Review and improve: Regularly review and enhance the de-identification methods based on feedback, changing regulations, or evolving best practices.
09
By following these steps, you can effectively fill out methods for de-identification.
Who needs methods for de-identification of?
01
The following entities or organizations may require methods for de-identification:
02
- Healthcare providers: To protect patient privacy and comply with regulations like HIPAA.
03
- Government agencies: When handling sensitive data like social security numbers, financial information, or personal records.
04
- Research institutions: To anonymize data for studies while maintaining data integrity.
05
- Legal firms: When dealing with confidential client information that needs to be shared securely.
06
By using methods for de-identification, these entities can ensure the privacy and security of sensitive information.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for the methods for de-identification of in Chrome?
As a PDF editor and form builder, pdfFiller has a lot of features. It also has a powerful e-signature tool that you can add to your Chrome browser. With our extension, you can type, draw, or take a picture of your signature with your webcam to make your legally-binding eSignature. Choose how you want to sign your methods for de-identification of and you'll be done in minutes.
How can I edit methods for de-identification of on a smartphone?
You can do so easily with pdfFiller’s applications for iOS and Android devices, which can be found at the Apple Store and Google Play Store, respectively. Alternatively, you can get the app on our web page: https://edit-pdf-ios-android.pdffiller.com/. Install the application, log in, and start editing methods for de-identification of right away.
How do I edit methods for de-identification of on an Android device?
The pdfFiller app for Android allows you to edit PDF files like methods for de-identification of. Mobile document editing, signing, and sending. Install the app to ease document management anywhere.
What is methods for de-identification of?
Methods for de-identification of are techniques used to remove or mask personally identifiable information from data in order to protect privacy.
Who is required to file methods for de-identification of?
Organizations and entities that handle sensitive or personal data are required to file methods for de-identification of.
How to fill out methods for de-identification of?
Methods for de-identification of can be filled out by detailing the specific techniques and processes used to safeguard data privacy.
What is the purpose of methods for de-identification of?
The purpose of methods for de-identification of is to ensure that personal information is protected and anonymized in compliance with data privacy regulations.
What information must be reported on methods for de-identification of?
Information such as the types of data being de-identified, the methods used, and any measures taken to secure the data must be reported on methods for de-identification of.
Fill out your methods for de-identification of online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Methods For De-Identification Of is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.