Get the Android Binder Use-After-Free Exploit - Vulners Database
Show details
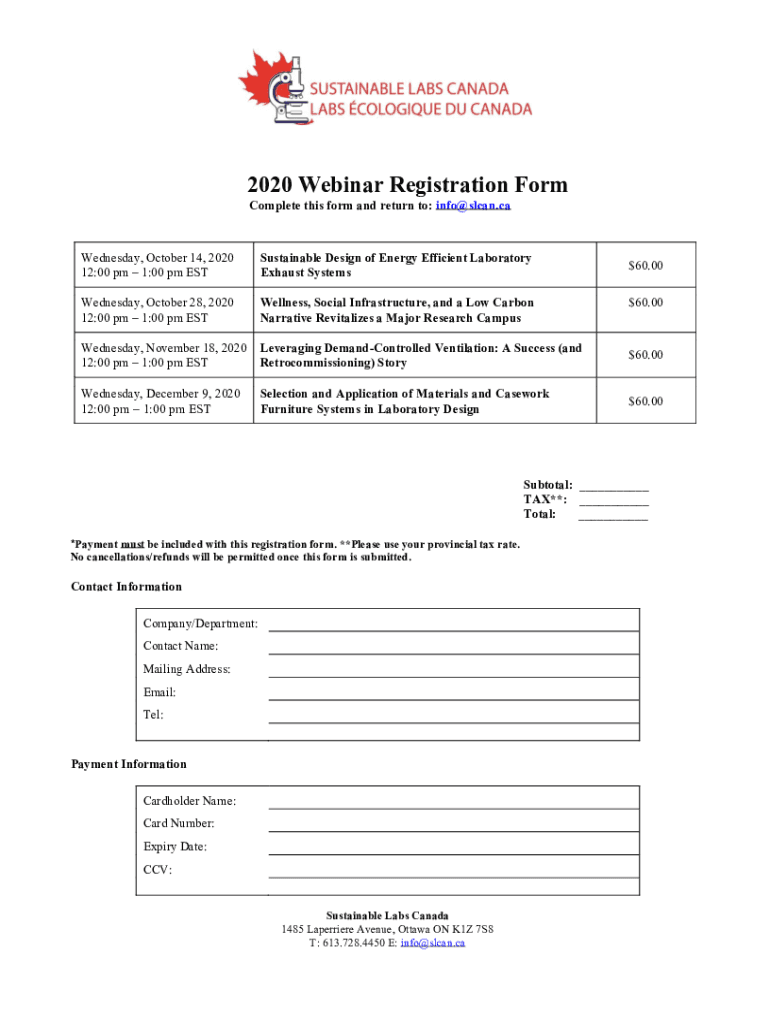
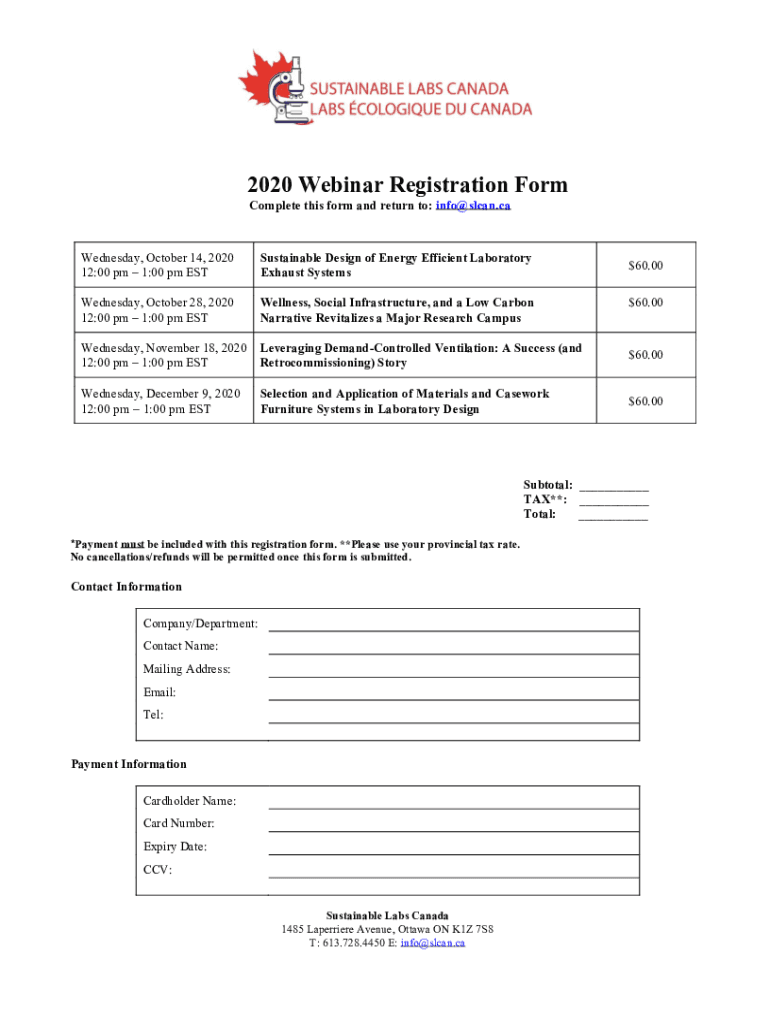
2020 Webinar Registration Form Complete this form and return to: info scan.ca Wednesday, October 14, 2020 12:00 pm 1:00 pm Sustainable Design of Energy Efficient Laboratory Exhaust Systems Wednesday,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign android binder use-after- exploit

Edit your android binder use-after- exploit form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your android binder use-after- exploit form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit android binder use-after- exploit online
Use the instructions below to start using our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit android binder use-after- exploit. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out android binder use-after- exploit

How to fill out android binder use-after- exploit
01
To fill out the Android Binder use-after-exploit, follow these steps:
02
Start by identifying a vulnerable Android device or emulator that is running a vulnerable version of the Android operating system. Vulnerable versions include Android 2.2 to Android 4.3.
03
Acquire the necessary tools and software required for the exploit, such as Android Debug Bridge (ADB) and a custom binder driver.
04
Set up the environment by enabling USB debugging on the target device and connecting it to your computer.
05
Use ADB to gain root access on the target device and remount the system partition as writable.
06
Push the custom binder driver to the target device and load it into the kernel.
07
Craft a malicious payload that takes advantage of the use-after-exploit vulnerability, utilizing the custom binder driver to gain unauthorized access or execute arbitrary code.
08
Trigger the exploit by sending the crafted payload to the vulnerable component of the system, such as a target process or service.
09
Once the exploit is successfully triggered, you should have control over the targeted Android device and can proceed with further actions, such as escalating privileges or exfiltrating sensitive data.
10
It is important to note that performing this exploit on devices without proper authorization is illegal and unethical. Only use it for research or ethical hacking purposes, and always ensure you have the necessary permissions and legal rights.
Who needs android binder use-after- exploit?
01
The Android Binder use-after-exploit is primarily used by security researchers, ethical hackers, or individuals interested in studying or testing the vulnerabilities in the Android operating system.
02
By exploiting the use-after-exploit vulnerability, researchers can identify weaknesses in the Android Binder subsystem and assist in developing patches and security measures to mitigate potential risks.
03
Additionally, organizations involved in cybersecurity or mobile device security may also utilize the exploit to enhance their understanding of Android vulnerabilities and improve their protection mechanisms.
04
It is important to emphasize that the use of this exploit for malicious purposes or unauthorized activities is strictly prohibited and illegal.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my android binder use-after- exploit directly from Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your android binder use-after- exploit and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
How do I edit android binder use-after- exploit in Chrome?
android binder use-after- exploit can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
How do I fill out the android binder use-after- exploit form on my smartphone?
On your mobile device, use the pdfFiller mobile app to complete and sign android binder use-after- exploit. Visit our website (https://edit-pdf-ios-android.pdffiller.com/) to discover more about our mobile applications, the features you'll have access to, and how to get started.
What is android binder use-after- exploit?
The android binder use-after- exploit is a vulnerability that allows an attacker to gain unauthorized access to the Android operating system by exploiting a memory corruption issue in the binder driver.
Who is required to file android binder use-after- exploit?
Any individual or organization that discovers or is affected by the android binder use-after- exploit is required to report it to the relevant security authorities.
How to fill out android binder use-after- exploit?
To report the android binder use-after- exploit, detailed information about the exploit, its impact, and any potential mitigations must be provided to the appropriate security team or agency.
What is the purpose of android binder use-after- exploit?
The purpose of reporting android binder use-after- exploit is to help security researchers and developers patch the vulnerability and prevent further exploitation by malicious actors.
What information must be reported on android binder use-after- exploit?
The information that must be reported on the android binder use-after- exploit includes details about the exploit, its impact, any known affected systems or devices, and potential mitigations or fixes.
Fill out your android binder use-after- exploit online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Android Binder Use-After- Exploit is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















