Get the free Network Security Audits / Vulnerability Assessments by ...
Show details
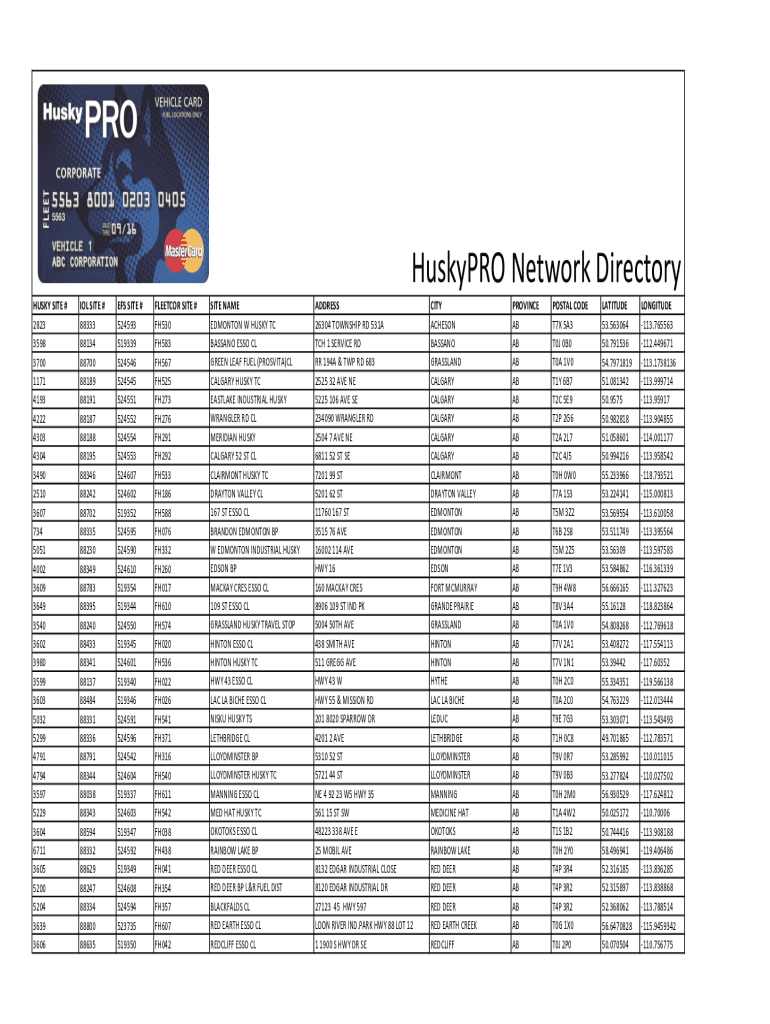
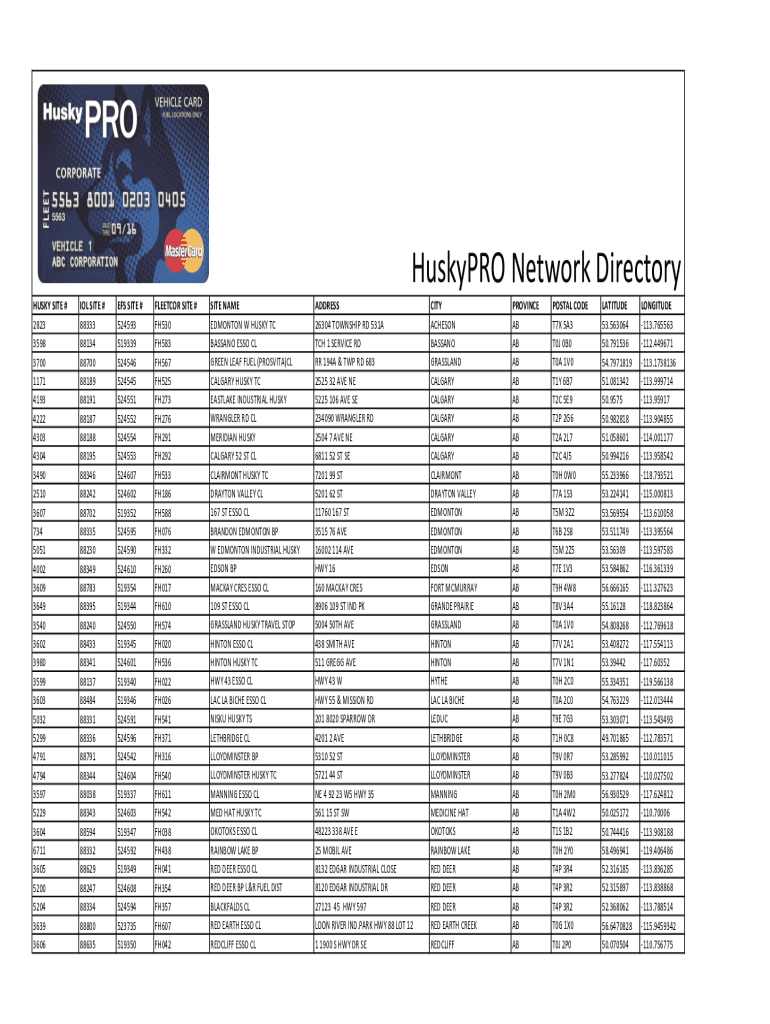
Husky PRO Network Directory HUSKY SITE # 2823 3598 3700 1171 4193 4222 4303 4304 3490 2510 3607 734 5051 4002 3609 3649 3540 3602 3980 3599 3603 5032 5299 4791 4794 3597 5229 3604 6711 3605 5200 5204
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign network security audits vulnerability

Edit your network security audits vulnerability form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your network security audits vulnerability form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit network security audits vulnerability online
Follow the guidelines below to benefit from a competent PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit network security audits vulnerability. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out network security audits vulnerability

How to fill out network security audits vulnerability
01
To fill out a network security audits vulnerability, follow these steps:
02
Start by identifying the scope of the audit and the assets that need to be evaluated for vulnerabilities.
03
Conduct a vulnerability assessment using automated tools or manual techniques to identify potential vulnerabilities in the network.
04
Document the identified vulnerabilities with detailed descriptions, including the affected systems, services, and potential impacts.
05
Assess the severity and likelihood of exploitation for each vulnerability to prioritize remediation efforts.
06
Develop a remediation plan that outlines the necessary steps to mitigate or eliminate the identified vulnerabilities.
07
Implement the remediation plan by applying patches, configuration changes, or other countermeasures as appropriate.
08
Conduct regular re-assessments or periodic audits to ensure the effectiveness of the implemented security measures.
09
Continuously monitor the network for new vulnerabilities and adapt the security measures accordingly.
10
Document the entire process, including the findings, actions taken, and any recommendations for further improvements.
Who needs network security audits vulnerability?
01
Network security audits vulnerability is needed by organizations and individuals who want to ensure the security of their network infrastructure.
02
This includes:
03
- Enterprises and businesses that rely on networks for their operations.
04
- IT departments responsible for managing and securing the network infrastructure.
05
- Security professionals and consultants offering network security assessment services.
06
- Government agencies or organizations handling sensitive data or critical infrastructure.
07
- Any individual or organization concerned about the potential risks and vulnerabilities in their network.
08
By conducting network security audits vulnerability, these entities can identify and address weaknesses in their network security posture, strengthen defenses, and protect against cyber threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get network security audits vulnerability?
The premium pdfFiller subscription gives you access to over 25M fillable templates that you can download, fill out, print, and sign. The library has state-specific network security audits vulnerability and other forms. Find the template you need and change it using powerful tools.
Can I create an electronic signature for signing my network security audits vulnerability in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your network security audits vulnerability directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
How can I fill out network security audits vulnerability on an iOS device?
Install the pdfFiller iOS app. Log in or create an account to access the solution's editing features. Open your network security audits vulnerability by uploading it from your device or online storage. After filling in all relevant fields and eSigning if required, you may save or distribute the document.
What is network security audits vulnerability?
Network security audits vulnerability is the process of assessing the vulnerabilities in a network to identify potential security risks.
Who is required to file network security audits vulnerability?
Organizations and companies that handle sensitive data or operate critical infrastructure are required to file network security audits vulnerability.
How to fill out network security audits vulnerability?
Network security audits vulnerability can be filled out by conducting a thorough assessment of network infrastructure and documenting any vulnerabilities found.
What is the purpose of network security audits vulnerability?
The purpose of network security audits vulnerability is to proactively identify and address security vulnerabilities in a network to prevent potential cyber attacks or data breaches.
What information must be reported on network security audits vulnerability?
Information such as network configuration, security protocols, active devices, vulnerabilities found, and remediation efforts must be reported on network security audits vulnerability.
Fill out your network security audits vulnerability online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Network Security Audits Vulnerability is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.



















