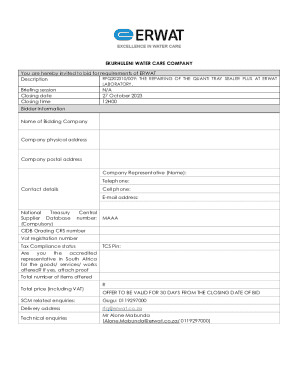
Get the free Anti Cyber Forensics - The Art of Counter-Cyber Forensics ...
Show details
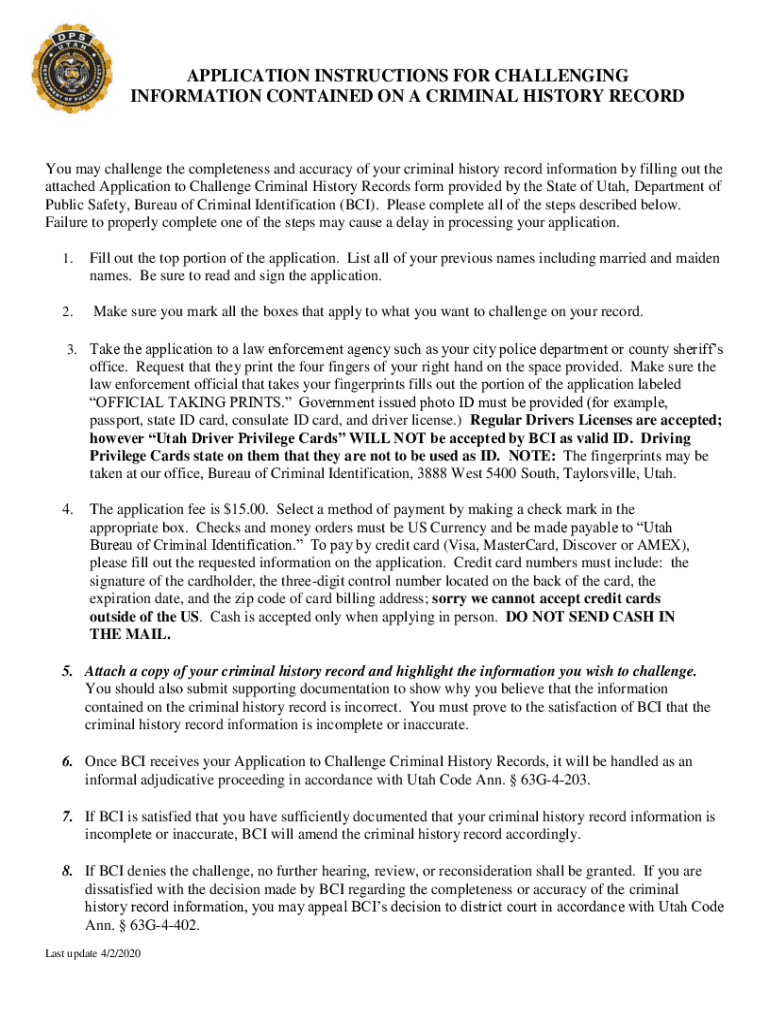
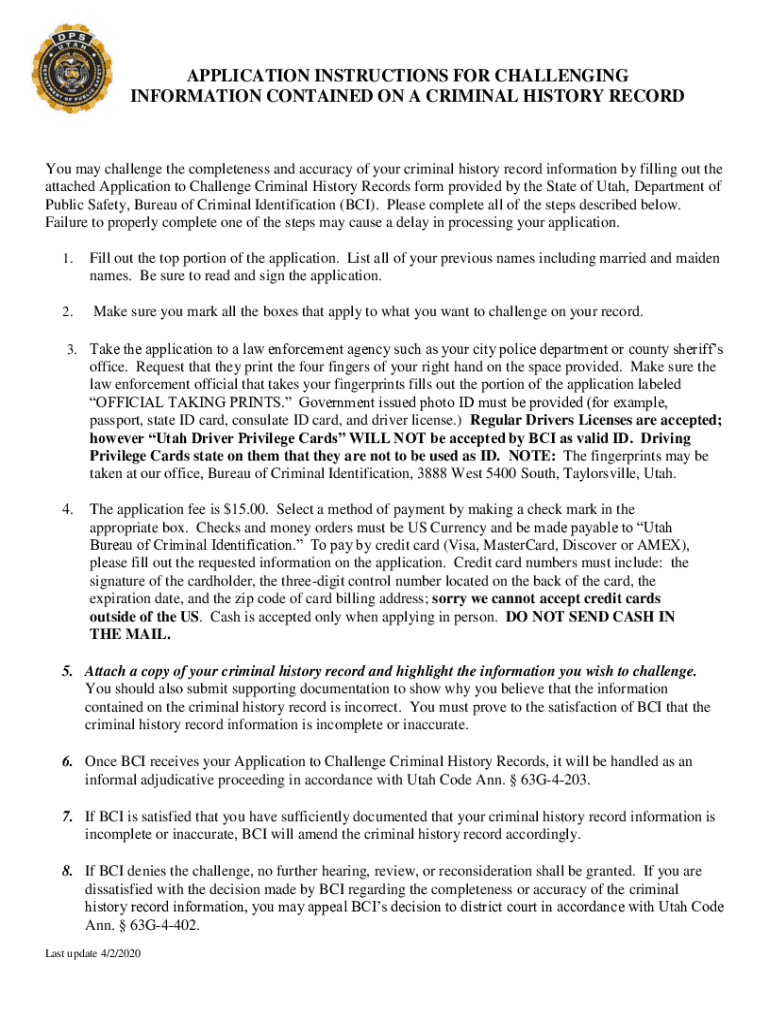
APPLICATION INSTRUCTIONS FOR CHALLENGING INFORMATION CONTAINED ON A CRIMINAL HISTORY Record may challenge the completeness and accuracy of your criminal history record information by filling out the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign anti cyber forensics
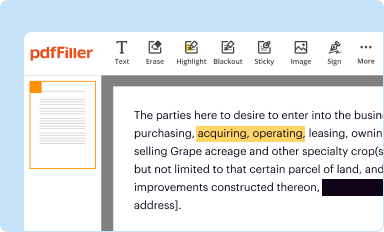
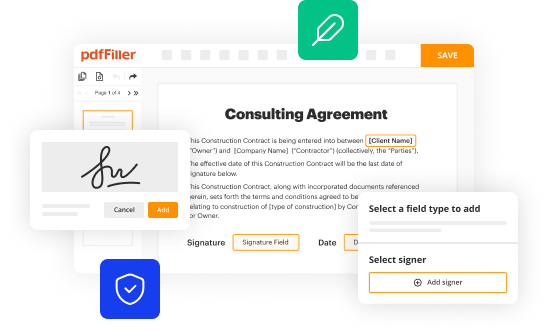
Edit your anti cyber forensics form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
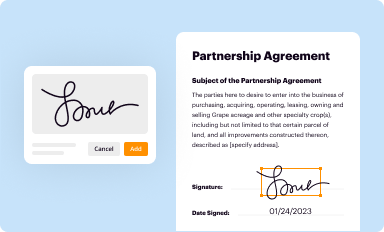
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your anti cyber forensics form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing anti cyber forensics online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit anti cyber forensics. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out anti cyber forensics
How to fill out anti cyber forensics
01
Gather all relevant information: Before filling out the anti cyber forensics, collect and document all pertinent information related to the cyber incident or crime.
02
Follow the forensic process: Be familiar with the established forensic process, which typically involves steps such as identification, preservation, extraction, analysis, and reporting of electronic evidence.
03
Document everything: Maintain a thorough documentation of every step and action taken during the anti cyber forensics process. This includes documenting timestamps, activities performed, and the tools or software used.
04
Preserve the evidence: Ensure the integrity and authenticity of the evidence by using proper techniques for preserving and securing digital evidence. This includes making backup copies and storing them in a secure location.
05
Analyze the evidence: Utilize specialized forensic tools and techniques to analyze the collected evidence. This may involve techniques such as data recovery, keyword searching, metadata analysis, and timeline reconstruction.
06
Draw conclusions and report findings: Based on the analysis of the evidence, form conclusions regarding the cybercrime or incident. Prepare a comprehensive report detailing the findings, including any supporting evidence and analysis performed.
07
Collaboration and legal considerations: Depending on the circumstances, it may be necessary to collaborate with law enforcement agencies or legal teams. Be prepared to comply with legal requirements and guidelines throughout the anti cyber forensics process.
08
Continuous learning and improvement: Stay updated with the latest cyber forensic techniques, tools, and regulations. Regularly engage in professional development activities to enhance your skills and knowledge in the field.
Who needs anti cyber forensics?
01
Anti cyber forensics is needed by various entities and individuals involved in investigating and solving cybercrimes. This can include but is not limited to:
02
- Law enforcement agencies: Police departments, cybercrime units, and other agencies responsible for combating cybercrimes require anti cyber forensics to gather evidence, analyze digital information, and build strong cases against perpetrators.
03
- Legal professionals: Lawyers, prosecutors, and defense attorneys often rely on anti cyber forensics to examine digital evidence and present it in court during cybercrime trials.
04
- Cybersecurity teams: Organizations with dedicated cybersecurity teams employ anti cyber forensics to investigate and respond to cyber incidents, identify vulnerabilities, and strengthen their overall security posture.
05
- Incident response teams: Incident response teams utilize anti cyber forensics to determine the cause and extent of a cyber incident, as well as to guide the appropriate remediation actions.
06
- Digital forensic investigators: Professionals specializing in digital forensics rely heavily on anti cyber forensics to uncover evidence, reconstruct digital activities, and support criminal investigations or civil litigation.
07
- Private companies: Businesses may require anti cyber forensics to investigate internal incidents, such as data breaches or employee misconduct, and to gather evidence for potential legal actions.
08
- Individuals affected by cybercrimes: Victims of cybercrimes, such as identity theft or online fraud, may seek assistance from professionals proficient in anti cyber forensics to help identify the perpetrators and gather evidence for legal action.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find anti cyber forensics?
It’s easy with pdfFiller, a comprehensive online solution for professional document management. Access our extensive library of online forms (over 25M fillable forms are available) and locate the anti cyber forensics in a matter of seconds. Open it right away and start customizing it using advanced editing features.
How can I edit anti cyber forensics on a smartphone?
The easiest way to edit documents on a mobile device is using pdfFiller’s mobile-native apps for iOS and Android. You can download those from the Apple Store and Google Play, respectively. You can learn more about the apps here. Install and log in to the application to start editing anti cyber forensics.
Can I edit anti cyber forensics on an iOS device?
You can. Using the pdfFiller iOS app, you can edit, distribute, and sign anti cyber forensics. Install it in seconds at the Apple Store. The app is free, but you must register to buy a subscription or start a free trial.
What is anti cyber forensics?
Anti cyber forensics is the process of identifying, preserving, analyzing, and presenting digital evidence in a way that is legally admissible.
Who is required to file anti cyber forensics?
Organizations and individuals involved in cyber incidents are required to file anti cyber forensics.
How to fill out anti cyber forensics?
To fill out anti cyber forensics, one must gather and analyze digital evidence related to a cyber incident, document findings, and report them in a forensically sound manner.
What is the purpose of anti cyber forensics?
The purpose of anti cyber forensics is to investigate cyber incidents, identify perpetrators, and provide evidence for legal proceedings.
What information must be reported on anti cyber forensics?
Information such as IP addresses, timestamps, logs, and any other digital evidence related to the cyber incident must be reported on anti cyber forensics.
Fill out your anti cyber forensics online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Anti Cyber Forensics is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.