Get the free Cyber Warfare and Cyber Terrorism PDF Computer ...
Show details
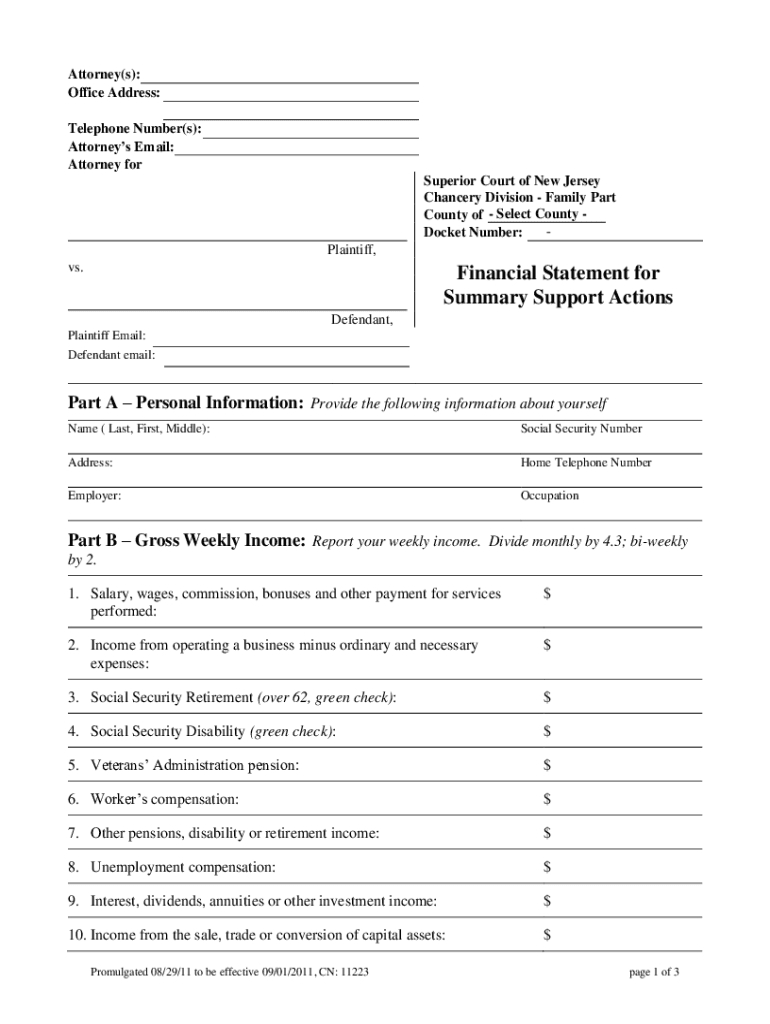
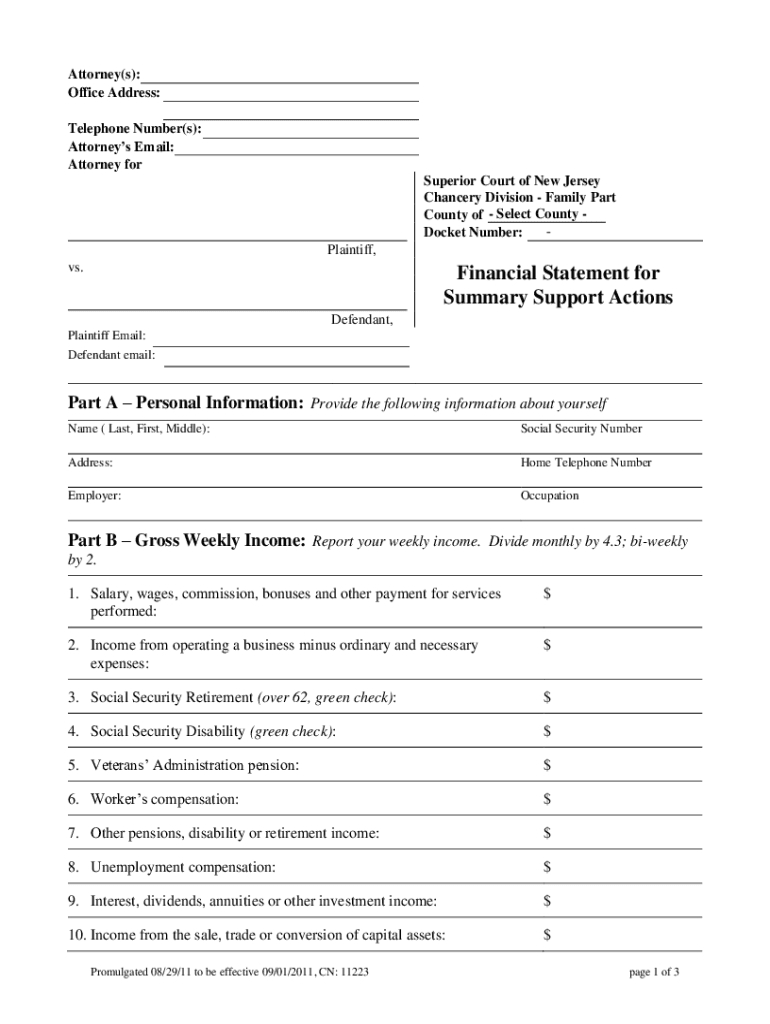
SavePrintClearAttorney(s): Office Address: Telephone Number(s): Attorneys Email: Attorney for Superior Court of New Jersey Chancery Division Family Part County of Select County Docket Number: Plaintiff,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber warfare and cyber

Edit your cyber warfare and cyber form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyber warfare and cyber form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cyber warfare and cyber online
To use our professional PDF editor, follow these steps:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit cyber warfare and cyber. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber warfare and cyber

How to fill out cyber warfare and cyber
01
To fill out cyber warfare and cyber, follow these steps:
02
Identify the purpose of the cyber warfare or cyber activity. Determine if it is for defensive or offensive purposes.
03
Assess the resources and capabilities available for the cyber warfare or cyber activity. This includes technical expertise, infrastructure, and tools.
04
Develop a comprehensive plan that outlines the objectives, targets, and strategies for the cyber warfare or cyber activity.
05
Implement necessary security measures to protect the actors involved in the cyber warfare or cyber activity.
06
Execute the plan by carrying out the cyber attacks or defensive actions according to the defined strategies.
07
Continuously monitor and evaluate the effectiveness of the cyber warfare or cyber activity. Make necessary adjustments if required.
08
Maintain secrecy and confidentiality to avoid detection and attribution.
09
Gather intelligence and learn from each cyber warfare or cyber operation to improve future capabilities.
10
Adhere to international laws and norms governing cyber warfare and cyber activities.
11
Keep up with the latest advancements in technology and cyber threats to stay ahead of potential adversaries.
Who needs cyber warfare and cyber?
01
Various entities and organizations may have a need for cyber warfare and cyber capabilities, including:
02
- Governments: National defense organizations may require cyber warfare capabilities to protect their country's interests, gather intelligence, or respond to cyber attacks from other nations.
03
- Military: Armed forces may utilize cyber warfare capabilities as part of their overall defense strategy, enabling them to disrupt enemy communication, cripple enemy infrastructure, or gain a strategic advantage in conflicts.
04
- Intelligence Agencies: Organizations engaged in intelligence gathering and analysis may leverage cyber warfare and cyber capabilities to collect information, conduct espionage, or sabotage hostile networks.
05
- Law Enforcement: Digital crime units and law enforcement agencies may require cyber capabilities to investigate and counteract cybercriminals and organized hacking groups.
06
- Critical Infrastructure: Companies and organizations responsible for critical infrastructure, such as power grids, transportation systems, or financial networks, may need cyber warfare and cyber capabilities to protect against cyber threats and potential attacks.
07
- Cybersecurity Companies: Organizations specializing in cybersecurity may develop and provide cyber warfare and cyber tools to assist governments and businesses in defending against cyber threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find cyber warfare and cyber?
The premium version of pdfFiller gives you access to a huge library of fillable forms (more than 25 million fillable templates). You can download, fill out, print, and sign them all. State-specific cyber warfare and cyber and other forms will be easy to find in the library. Find the template you need and use advanced editing tools to make it your own.
Can I create an electronic signature for the cyber warfare and cyber in Chrome?
Yes, you can. With pdfFiller, you not only get a feature-rich PDF editor and fillable form builder but a powerful e-signature solution that you can add directly to your Chrome browser. Using our extension, you can create your legally-binding eSignature by typing, drawing, or capturing a photo of your signature using your webcam. Choose whichever method you prefer and eSign your cyber warfare and cyber in minutes.
How do I fill out cyber warfare and cyber using my mobile device?
You can quickly make and fill out legal forms with the help of the pdfFiller app on your phone. Complete and sign cyber warfare and cyber and other documents on your mobile device using the application. If you want to learn more about how the PDF editor works, go to pdfFiller.com.
What is cyber warfare and cyber?
Cyber warfare refers to attacks on computer systems and networks carried out by one nation against another. Cyber refers to anything related to computers, data, software, and information.
Who is required to file cyber warfare and cyber?
Entities involved in cyber activities or those who have suffered cyber attacks are required to file cyber warfare and cyber reports.
How to fill out cyber warfare and cyber?
Cyber warfare and cyber reports can be filled out online through the designated reporting portal or submitted via email to the appropriate authorities.
What is the purpose of cyber warfare and cyber?
The purpose of cyber warfare and cyber reports is to track and analyze cyber attacks, assess vulnerabilities, and enhance cybersecurity measures.
What information must be reported on cyber warfare and cyber?
Information such as the nature of the cyber attack, date and time of occurrence, impact on operations, and any mitigating actions taken must be reported on cyber warfare and cyber.
Fill out your cyber warfare and cyber online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Warfare And Cyber is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.