Get the free Security in Depth
Show details
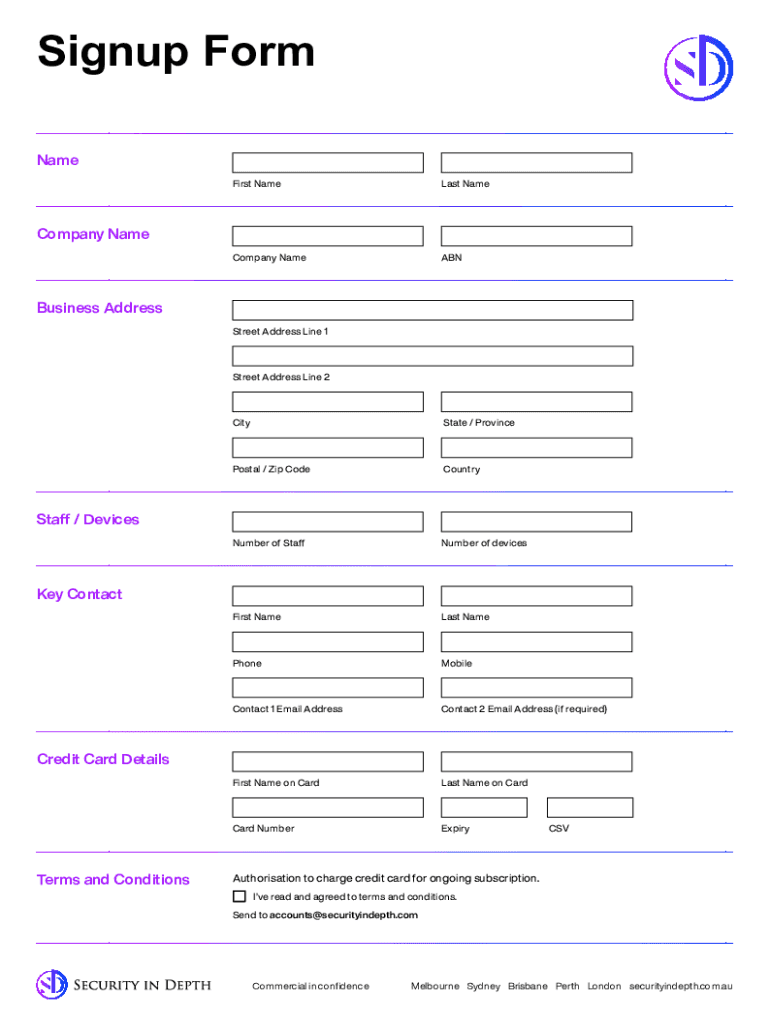
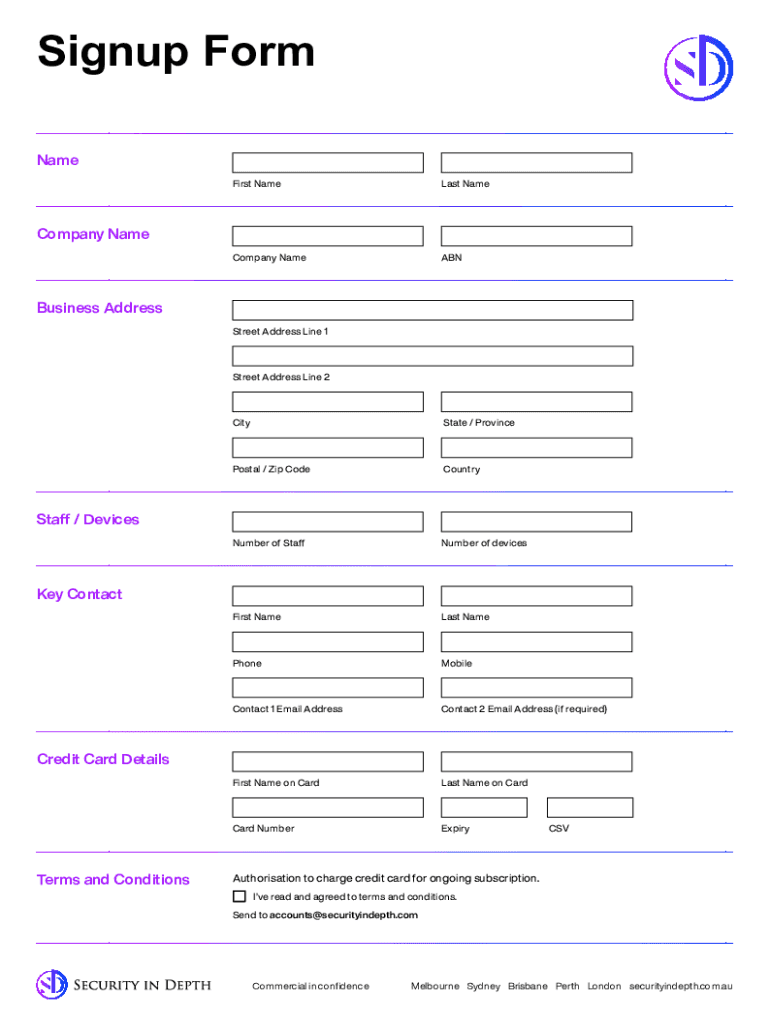
Security in Depth Security Services Sign Up Formsecurityindepth.com.assigned Form Name First Nameless Accompany NameABNCompany NameBusiness Address Street Address Line 1Street Address Line 2CityState
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security in depth

Edit your security in depth form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your security in depth form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit security in depth online
Use the instructions below to start using our professional PDF editor:
1
Log in to your account. Start Free Trial and sign up a profile if you don't have one.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit security in depth. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security in depth

How to fill out security in depth
01
Start by identifying the assets that need protection. This could include sensitive data, technology systems, physical premises, or intellectual property.
02
Conduct a risk assessment to understand the potential threats and vulnerabilities that could compromise the security of these assets.
03
Implement multiple layers of security controls. This could include physical controls like locks and access control systems, technical controls like firewalls and encryption, and procedural controls like security policies and employee training.
04
Regularly monitor and update security measures to address new risks and vulnerabilities.
05
Establish incident response procedures to quickly detect, respond to, and recover from security incidents.
06
Continuously evaluate and improve the security in depth strategy to adapt to changing threat landscapes.
07
Consider involving external experts or consultants to ensure a comprehensive and unbiased approach to security in depth.
Who needs security in depth?
01
Any organization or individual that wants to protect their valuable assets from potential threats and mitigate the impact of security breaches needs security in depth.
02
Industries such as finance, healthcare, government, and e-commerce that handle sensitive data are prime candidates for implementing security in depth.
03
Organizations that want to comply with industry regulations or standards also benefit from security in depth.
04
Additionally, individuals or organizations that have experienced previous security incidents or have valuable intellectual property should prioritize security in depth measures.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit security in depth from Google Drive?
By integrating pdfFiller with Google Docs, you can streamline your document workflows and produce fillable forms that can be stored directly in Google Drive. Using the connection, you will be able to create, change, and eSign documents, including security in depth, all without having to leave Google Drive. Add pdfFiller's features to Google Drive and you'll be able to handle your documents more effectively from any device with an internet connection.
Can I edit security in depth on an iOS device?
Create, edit, and share security in depth from your iOS smartphone with the pdfFiller mobile app. Installing it from the Apple Store takes only a few seconds. You may take advantage of a free trial and select a subscription that meets your needs.
How can I fill out security in depth on an iOS device?
Make sure you get and install the pdfFiller iOS app. Next, open the app and log in or set up an account to use all of the solution's editing tools. If you want to open your security in depth, you can upload it from your device or cloud storage, or you can type the document's URL into the box on the right. After you fill in all of the required fields in the document and eSign it, if that is required, you can save or share it with other people.
What is security in depth?
Security in depth is a multilayered approach to security that aims to protect information and assets by implementing multiple layers of defense. This strategy provides redundancy in case one layer fails, thereby reducing the chances of a successful attack.
Who is required to file security in depth?
Organizations that handle sensitive information or operate in regulated industries, such as financial services, healthcare, and government sectors, are typically required to file security in depth.
How to fill out security in depth?
To fill out security in depth, organizations must assess their security measures, identify potential vulnerabilities, and document the layers of security in place. This may include policies, physical security, access controls, and technology used to protect assets.
What is the purpose of security in depth?
The purpose of security in depth is to enhance the overall security posture of an organization by employing various defensive measures. It aims to provide comprehensive protection and ensure that if one layer is compromised, others remain intact to prevent a breach.
What information must be reported on security in depth?
Organizations must report details on their security policies, implemented security technologies, incident response strategies, and any previous security breaches, along with their measures for mitigating future risks.
Fill out your security in depth online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Security In Depth is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















