Get the free Cyber Investigation Technology
Show details
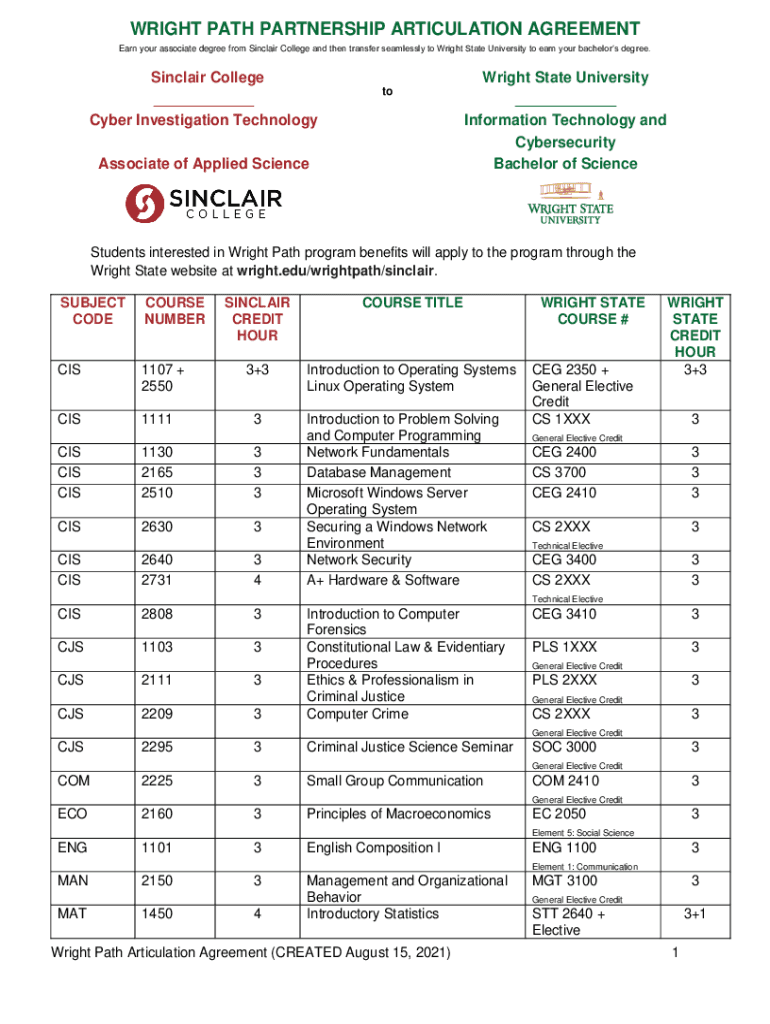
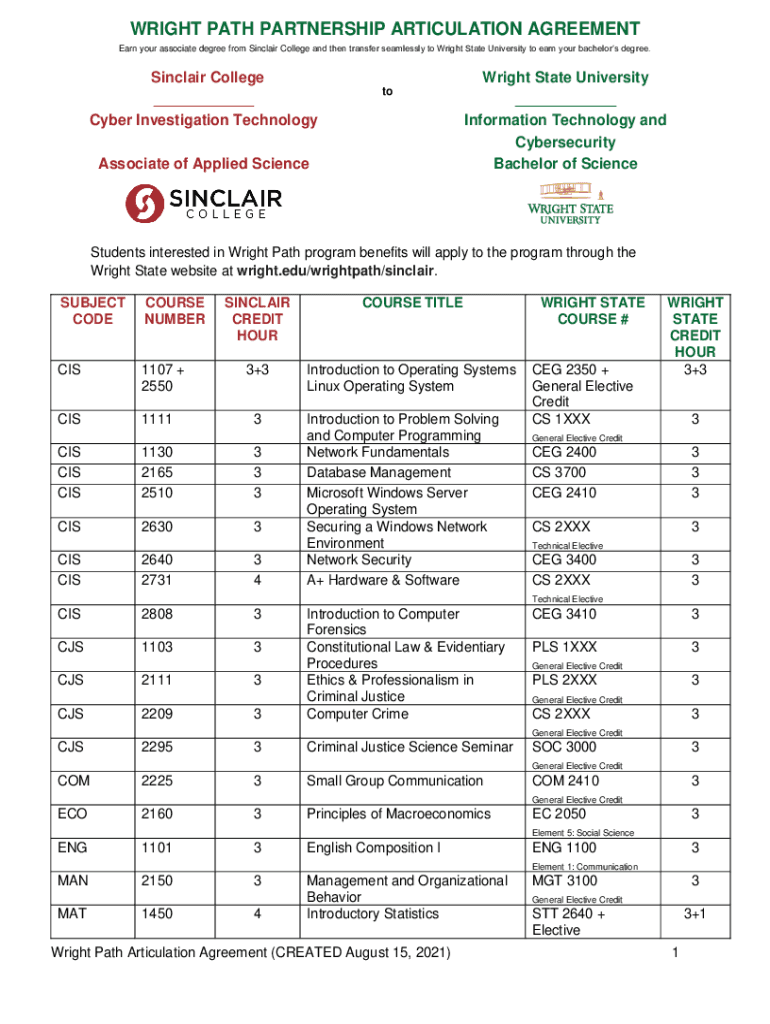
WRIGHT PATH PARTNERSHIP ARTICULATION AGREEMENT Earn your associate degree from Sinclair College and then transfer seamlessly to Wright State University to earn your bachelors degree. Sinclair College
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber investigation technology

Edit your cyber investigation technology form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyber investigation technology form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing cyber investigation technology online
To use the services of a skilled PDF editor, follow these steps:
1
Check your account. It's time to start your free trial.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit cyber investigation technology. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
It's easier to work with documents with pdfFiller than you could have ever thought. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber investigation technology

How to fill out cyber investigation technology
01
Start by gathering all the relevant information and evidence related to the cyber investigation.
02
Analyze the information and evidence collected to identify any patterns, motives, or potential suspects.
03
Utilize cyber investigation technology tools such as forensic software, data recovery tools, and network analysis tools to extract and analyze digital evidence.
04
Document all the findings and organize them in a structured manner for further analysis and presentation.
05
Use advanced techniques like data mining, data visualization, and machine learning algorithms to uncover hidden patterns or connections in the digital data.
06
Continuously update and maintain knowledge of the latest cyber investigation technology trends and tools to stay ahead in the field.
07
Collaborate with other experts and law enforcement agencies to share information and leverage their expertise for more effective cyber investigations.
08
Ensure compliance with legal and ethical standards throughout the investigation process.
09
Communicate the findings and conclusions of the cyber investigation in a clear and concise manner to relevant stakeholders.
10
Regularly review and update cyber investigation procedures and techniques to adapt to the evolving nature of cybercrime.
Who needs cyber investigation technology?
01
Law enforcement agencies: Cyber investigation technology is crucial for law enforcement agencies to effectively investigate and solve cybercrimes.
02
Private investigators: Private investigators dealing with digital forensics or cyber-related cases can benefit from utilizing cyber investigation technology.
03
Corporate cybersecurity teams: Cyber investigation technology helps corporate cybersecurity teams to conduct internal investigations and mitigate threats to their digital infrastructure.
04
Government agencies: Government agencies responsible for national security and intelligence gathering rely on cyber investigation technology for counterintelligence and cyber defense purposes.
05
Digital forensic experts: Professionals specializing in digital forensics and cyber investigations heavily rely on specialized technology tools and techniques.
06
IT and cybersecurity professionals: Having knowledge of cyber investigation technology is beneficial for IT and cybersecurity professionals to identify and respond to potential cyber threats efficiently.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an eSignature for the cyber investigation technology in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your cyber investigation technology directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
How do I complete cyber investigation technology on an iOS device?
In order to fill out documents on your iOS device, install the pdfFiller app. Create an account or log in to an existing one if you have a subscription to the service. Once the registration process is complete, upload your cyber investigation technology. You now can take advantage of pdfFiller's advanced functionalities: adding fillable fields and eSigning documents, and accessing them from any device, wherever you are.
How do I complete cyber investigation technology on an Android device?
On Android, use the pdfFiller mobile app to finish your cyber investigation technology. Adding, editing, deleting text, signing, annotating, and more are all available with the app. All you need is a smartphone and internet.
What is cyber investigation technology?
Cyber investigation technology refers to the tools, techniques, and processes used to investigate and analyze cyber incidents.
Who is required to file cyber investigation technology?
Organizations or individuals involved in cyber incidents may be required to file cyber investigation technology.
How to fill out cyber investigation technology?
Cyber investigation technology can be filled out by providing detailed information about the cyber incident, including any evidence or findings.
What is the purpose of cyber investigation technology?
The purpose of cyber investigation technology is to gather information, analyze data, and identify the root cause of cyber incidents.
What information must be reported on cyber investigation technology?
Information such as the date and time of the incident, affected systems, and any security measures taken must be reported on cyber investigation technology.
Fill out your cyber investigation technology online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Investigation Technology is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















