Get the free Key and Lock Policy - ppd ufl
Show details
Este documento aborda la política de llaves y cerraduras de la Universidad de Florida, incluyendo responsabilidades, procedimientos para solicitar y devolver llaves, gestión de llaves perdidas o
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign key and lock policy

Edit your key and lock policy form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your key and lock policy form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit key and lock policy online
Use the instructions below to start using our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit key and lock policy. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
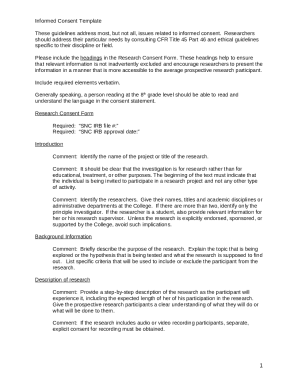
How to fill out key and lock policy

How to fill out Key and Lock Policy
01
Determine the purpose of the Key and Lock Policy.
02
Identify the types of keys and locks that will be covered by the policy.
03
Define roles and responsibilities regarding key distribution and management.
04
Establish protocols for key issuance, return, and reporting lost keys.
05
Outline security measures to prevent unauthorized access.
06
Create a method for tracking keys and access to locked areas.
07
Set a review schedule for the policy to ensure it remains up-to-date.
08
Provide training for employees on the importance of the policy.
Who needs Key and Lock Policy?
01
Facility managers.
02
Security personnel.
03
IT departments handling secure areas.
04
Employees responsible for access control.
05
Contractors or third parties who require access.
Fill
form
: Try Risk Free






People Also Ask about
What is the key control policy?
Key control is a critically important aspect of security management within any business, directly impacting both physical and risk management strategies. At its core, key control refers to the policies, systems, and procedures that govern how keys are issued, tracked, and managed.
What is the lock and key system?
In its simplest implementation, a key operates one lock or set of locks that are keyed alike, a lock/key system where each similarly keyed lock requires the same, unique key.
What does the lock and key system refer to?
In 1894, German chemist Emil Fischer proposed the lock and key theory, which states that enzymes have a specific shape that directly correlates to the shape of the substrate. Basically, substrates fit into an enzyme the way a key fits into a lock.
What is the lock and key system in psychology?
Receptors and neurotransmitters act like a lock-and-key system. Just as it takes the right key to open a specific lock, a neurotransmitter (the key) will only bind to a specific receptor (the lock). If the neurotransmitter is able to work on the receptor site, it triggers changes in the receiving cell.
How often should a key and lock custodian audit keys?
Yet when we think of locks and keys, we don't only think of doors; we think of the ways these objects can have symbolic meaning in our lives. As such, some people take the two as a symbol of freedom and confinement. Others see them as symbols of closing one chapter in their life and opening another.
What is the lock and key system of enzymes?
"Lock and key" model To explain the observed specificity of enzymes, in 1894 Emil Fischer proposed that both the enzyme and the substrate possess specific complementary geometric shapes that fit exactly into one another. This is often referred to as "the lock and key" model.
How does the lock and key system work?
When the right key slides into a pin-and-tumbler lock, the pointed teeth and notches on the blade of the key allow the spring-loaded pins to move up and down until they line up with a track called the shear line. When the pins align with the shear line, the cylinder can turn and the lock will open.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Key and Lock Policy?
The Key and Lock Policy is a regulatory framework that outlines the procedures for managing keys and locks to ensure the security of physical and electronic assets.
Who is required to file Key and Lock Policy?
Organizations that handle sensitive information and valuable assets are typically required to file a Key and Lock Policy, including businesses, government agencies, and educational institutions.
How to fill out Key and Lock Policy?
To fill out a Key and Lock Policy, organizations should document their key management procedures, identify responsible personnel, outline access controls, and specify regular audits and reviews.
What is the purpose of Key and Lock Policy?
The purpose of the Key and Lock Policy is to establish protocols for securing, tracking, and managing keys and locks to minimize risks of unauthorized access and improve overall security.
What information must be reported on Key and Lock Policy?
Key and Lock Policy must report information such as a list of keys and locks, assigned personnel, access levels, usage logs, and procedures for lost or stolen keys.
Fill out your key and lock policy online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Key And Lock Policy is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.