Get the free Email Sender Authentication Deployment - bits
Show details
Este documento proporciona las mejores prácticas y consideraciones sobre la implementación de la autenticación del remitente de correos electrónicos para instituciones financieras. Se centra en
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign email sender auformntication deployment
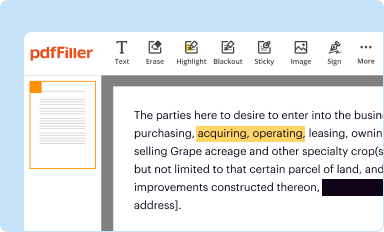
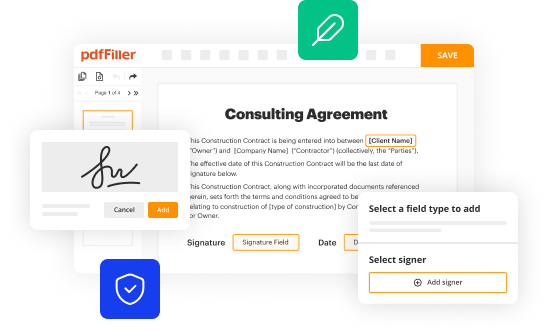
Edit your email sender auformntication deployment form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
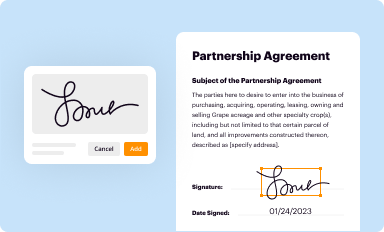
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
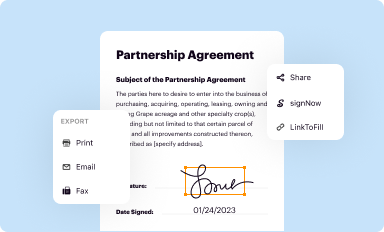
Share your form instantly
Email, fax, or share your email sender auformntication deployment form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing email sender auformntication deployment online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit email sender auformntication deployment. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out email sender auformntication deployment
How to fill out Email Sender Authentication Deployment
01
Log in to your email service provider's administration dashboard.
02
Navigate to the authentication settings section.
03
Select the option for Email Sender Authentication Deployment.
04
Enter your domain name for the emails you want to authenticate.
05
Configure SPF (Sender Policy Framework) by adding the appropriate DNS TXT record.
06
Set up DKIM (DomainKeys Identified Mail) by generating a key and adding it to your DNS records.
07
Optionally, implement DMARC (Domain-based Message Authentication, Reporting & Conformance) by creating a DMARC record in your DNS.
08
Verify the settings to ensure they are correctly implemented.
09
Test email delivery to confirm that authentication works as intended.
Who needs Email Sender Authentication Deployment?
01
Businesses that send marketing emails.
02
Organizations that want to improve email deliverability.
03
Any entity that needs to secure their email communications.
04
Email marketers who want to prevent spoofing and phishing.
05
Companies that require compliance with email authentication standards.
Fill
form
: Try Risk Free






People Also Ask about
What are the 3 email protocols?
What are the different email protocols? The common protocols for email delivery are Post Office Protocol (POP), Internet Message Access Protocol (IMAP), and Simple Mail Transfer Protocol (SMTP). Each of these protocols has a standard methodology to deal with the emails and also has defined functions.
What are the authentication methods for email?
5 standards of email authentication: Protocols and methods SPF. DKIM. DMARC. ARC. BIMI.
How can you verify the authenticity of an email sender?
How to check if an email is legitimate Check the actual email address, not just the display name. Look at the sender domain closely. Check the email headers. Exact-domain spoofing. Lookalike domains. Open signups that use a recognizable name. Implement DMARC, SPF, and DKIM. Use advanced email filtering solutions.
What are the authentication protocols for email?
SPF, DKIM, and DMARC help authenticate email senders by verifying that the emails came from the domain that they claim to be from. These three authentication methods are important for preventing spam, phishing attacks, and other email security risks.
What is SPF and DKIM and DMARC?
DKIM (DomainKeys Identified Mail), SPF (Sender Policy Framework), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) are three technologies that are commonly used by ISPs (Internet Service Providers) to protect users from cyber threats and email fraud, improving the legitimacy of delivered
What are the three major email authentication protocols?
Three primary email authentication methods SPF. DKIM / DomainKeys. DMARC.
How to authenticate an email sender?
How to authenticate email Use consistent sender addresses. Be consistent with the from addresses and friendly from names you use. Authenticate your IP addresses with SPF. Configure DKIM signatures for your messages. Protect your domain with DMARC authentication. Prepare for BIMI.
What are the different types of email authentication?
By implementing the three core email authentication methods: SPF, DKIM, and DMARC, you'll be able to protect your email. But each protocol requires steps to take to configure the elements properly. SPF is the starting point and is the easiest place to start.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Email Sender Authentication Deployment?
Email Sender Authentication Deployment refers to the process of implementing various authentication protocols to verify the identity of the sender of an email. This helps to prevent email spoofing and ensures that messages originate from legitimate sources.
Who is required to file Email Sender Authentication Deployment?
Organizations that send emails, especially those that engage in marketing or transactional communications, are required to file Email Sender Authentication Deployment to ensure compliance with email authentication standards.
How to fill out Email Sender Authentication Deployment?
To fill out the Email Sender Authentication Deployment, organizations need to provide specific information about their email authentication methods, such as SPF, DKIM, and DMARC configurations, along with the domain names used for sending emails.
What is the purpose of Email Sender Authentication Deployment?
The purpose of Email Sender Authentication Deployment is to enhance email security, protect recipients from phishing and spoofing attacks, and improve email deliverability by establishing trust in the sender's identity.
What information must be reported on Email Sender Authentication Deployment?
The information that must be reported includes details about the authentication methods used (like SPF, DKIM, DMARC), the domains involved, and any policies regarding how unverified emails should be handled.
Fill out your email sender auformntication deployment online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Email Sender Auformntication Deployment is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.