Get the free Cyber threat activity in Ukraine: analysis and resources
Show details
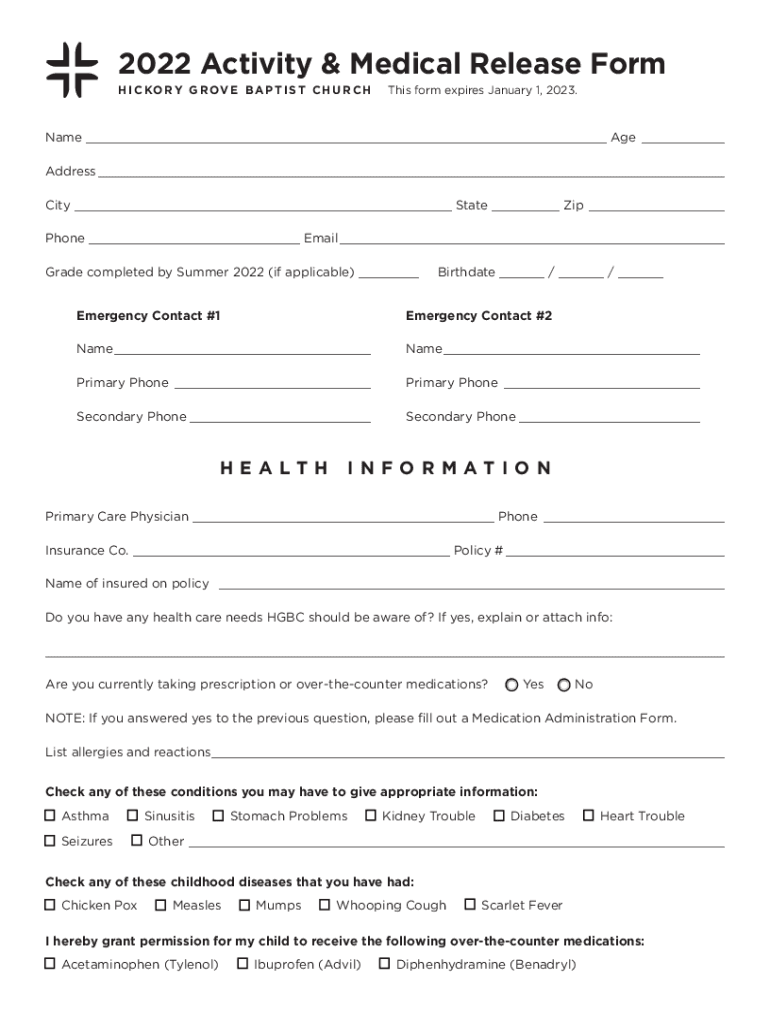
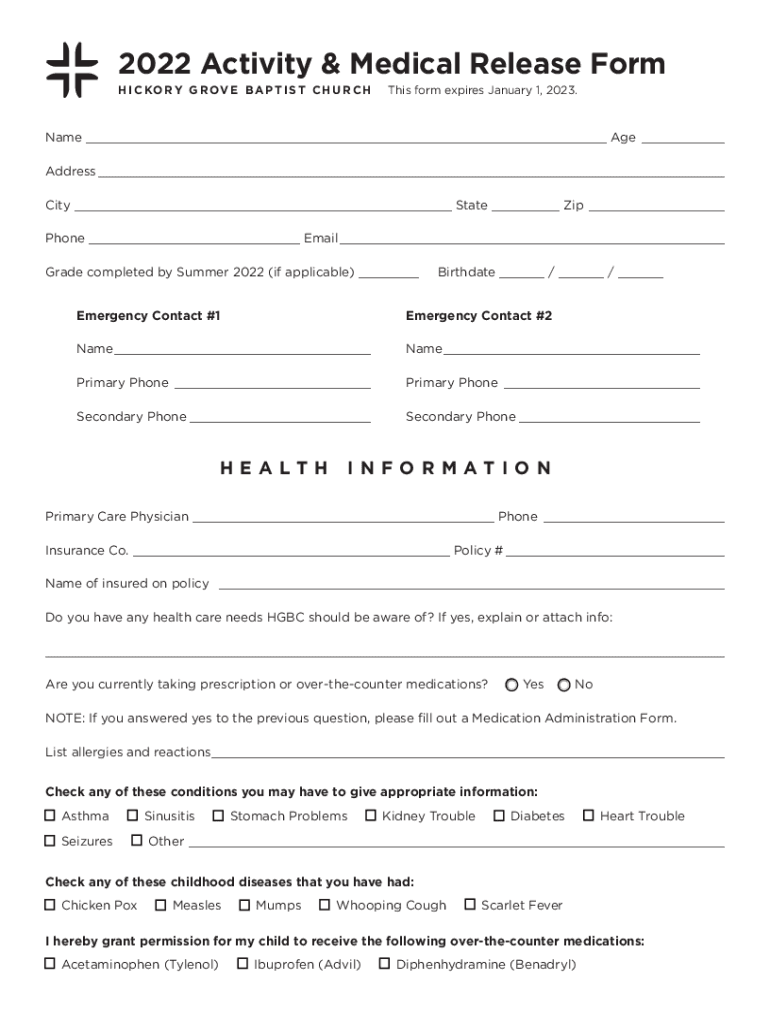
2022 Activity & Medical Release Form H I C KO R Y G R O V E B A P T I S T C H U R CH This form expires January 1, 2023. Name ___ Age___ Address___ City ___ State ___ Zip___Phone ___ Email___ Grade
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber threat activity in

Edit your cyber threat activity in form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyber threat activity in form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing cyber threat activity in online
To use the professional PDF editor, follow these steps below:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit cyber threat activity in. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
It's easier to work with documents with pdfFiller than you could have believed. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber threat activity in

How to fill out cyber threat activity in
01
Gather all available information on the cyber threat activity.
02
Fill out the Cyber Threat Activity Form with as much detail as possible.
03
Include any relevant evidence or documentation to support your findings.
04
Submit the completed form to the appropriate security team or authorities for further action.
Who needs cyber threat activity in?
01
Cybersecurity professionals
02
Law enforcement agencies
03
Government agencies
04
Organizations with sensitive information or valuable assets
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for the cyber threat activity in in Chrome?
Yes. You can use pdfFiller to sign documents and use all of the features of the PDF editor in one place if you add this solution to Chrome. In order to use the extension, you can draw or write an electronic signature. You can also upload a picture of your handwritten signature. There is no need to worry about how long it takes to sign your cyber threat activity in.
How do I edit cyber threat activity in straight from my smartphone?
Using pdfFiller's mobile-native applications for iOS and Android is the simplest method to edit documents on a mobile device. You may get them from the Apple App Store and Google Play, respectively. More information on the apps may be found here. Install the program and log in to begin editing cyber threat activity in.
How do I fill out cyber threat activity in on an Android device?
Use the pdfFiller mobile app to complete your cyber threat activity in on an Android device. The application makes it possible to perform all needed document management manipulations, like adding, editing, and removing text, signing, annotating, and more. All you need is your smartphone and an internet connection.
What is cyber threat activity in?
Cyber threat activity is the unauthorized access, use, disclosure, disruption, modification, or destruction of information systems or networks.
Who is required to file cyber threat activity in?
Organizations and businesses that are victims of cyber threats are required to file cyber threat activity reports.
How to fill out cyber threat activity in?
Cyber threat activity reports can be filled out online through the designated reporting portal provided by the relevant authorities.
What is the purpose of cyber threat activity in?
The purpose of cyber threat activity reports is to gather information on cyber threats to improve cybersecurity measures and prevent future cyber attacks.
What information must be reported on cyber threat activity in?
Cyber threat activity reports must include details of the incident, impact on the organization, and any remediation steps taken.
Fill out your cyber threat activity in online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Threat Activity In is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















