
Get the free Email Alias Detection Using Social Network Analysis - dataprivacylab
Show details
This research paper addresses the problem of linking email aliases to their respective entities using social network analysis methods. It evaluates various approaches based on email collocation data
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign email alias detection using
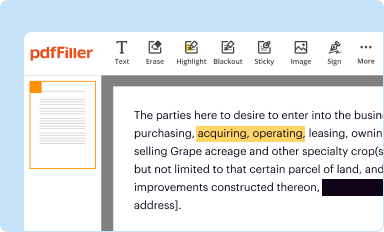
Edit your email alias detection using form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
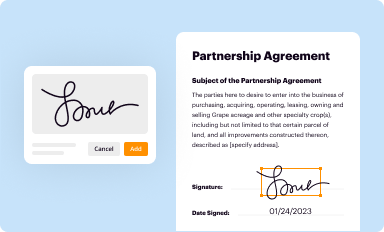
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
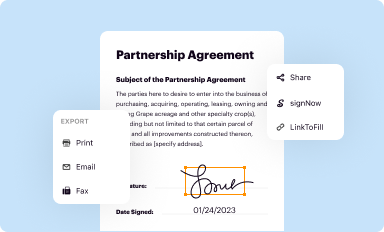
Share your form instantly
Email, fax, or share your email alias detection using form via URL. You can also download, print, or export forms to your preferred cloud storage service.
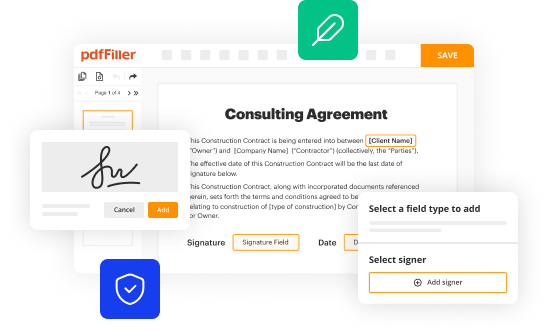
Editing email alias detection using online
Use the instructions below to start using our professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit email alias detection using. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out email alias detection using
How to fill out Email Alias Detection Using Social Network Analysis
01
Identify the individuals whose email aliases you want to detect.
02
Gather data from various social networks relating to these individuals, including their profiles, posts, and interactions.
03
Use social network analysis tools to map the connections and interactions among the identified individuals.
04
Analyze the data to spot patterns or commonalities that may indicate related email addresses or aliases.
05
Validate the findings by cross-referencing with additional datasets or email verification tools.
06
Document the discovered email aliases and their connections for future reference.
Who needs Email Alias Detection Using Social Network Analysis?
01
Organizations wanting to enhance their email outreach strategies.
02
The security teams looking to prevent phishing attacks by identifying potential alias accounts.
03
Marketing teams aiming to analyze customer behavior through multiple email aliases.
04
Researchers conducting studies on social networks and communication patterns.
Fill
form
: Try Risk Free






People Also Ask about
What is the difference between an email address and an alias?
An alias looks like an email account address but it is technically different. An alias does not have a storage area on an email server; rather, it immediately forwards all messages to one or more email accounts.
When should you use an email alias?
8 types of alias use cases Avoiding disclosure of your personal email. Using a temporary email address. Remaining in contact with former employees. Employees filling multiple roles within a company. Maintaining a private identity. Saving space. Sending emails from a different email address. Creating a memorable email address.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Email Alias Detection Using Social Network Analysis?
Email Alias Detection Using Social Network Analysis is a method that analyzes email communication patterns within a social network to identify and link various email aliases associated with a single individual. It leverages the connections and interactions among users to determine how different email addresses are related.
Who is required to file Email Alias Detection Using Social Network Analysis?
Individuals and organizations that need to identify email alias associations for security, compliance, or investigative reasons are typically required to file Email Alias Detection Using Social Network Analysis.
How to fill out Email Alias Detection Using Social Network Analysis?
To fill out Email Alias Detection Using Social Network Analysis, one must gather data about email interactions, including the email addresses involved, timestamps, and connection details. This data is then analyzed to map out connections and identify potential aliases.
What is the purpose of Email Alias Detection Using Social Network Analysis?
The purpose of Email Alias Detection Using Social Network Analysis is to enhance security measures, detect fraudulent activities, combat phishing, and ensure compliance with regulations by accurately identifying individuals behind multiple email aliases.
What information must be reported on Email Alias Detection Using Social Network Analysis?
The information that must be reported includes the list of email addresses analyzed, the patterns of interaction observed, the identified aliases, and any notable findings or associations that may warrant further investigation.
Fill out your email alias detection using online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Email Alias Detection Using is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















