Get the free DDoS Botnets are Exploiting Critical Vulnerability in Zyxel ...
Show details
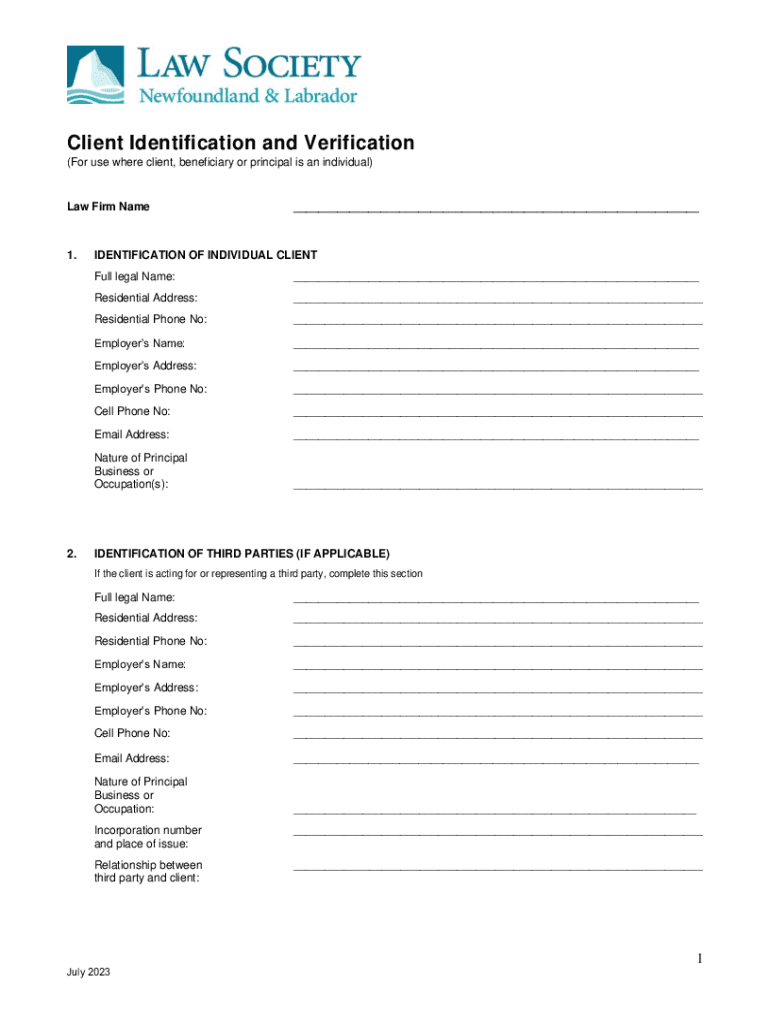
Client Identification and Verification (For use where client, beneficiary or principal is an individual)Law Firm Name1.2.___IDENTIFICATION OF INDIVIDUAL CLIENT Full legal Name:___Residential Address:___Residential
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign ddos botnets are exploiting

Edit your ddos botnets are exploiting form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your ddos botnets are exploiting form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing ddos botnets are exploiting online
Follow the guidelines below to benefit from a competent PDF editor:
1
Log in to your account. Click Start Free Trial and register a profile if you don't have one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit ddos botnets are exploiting. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out ddos botnets are exploiting

How to fill out ddos botnets are exploiting
01
Identify the IP addresses and websites being targeted by the botnets.
02
Contact the hosting providers and work with them to mitigate the attack.
03
Implement strong network security measures such as firewalls and intrusion detection systems.
04
Regularly monitor network traffic for any suspicious activity and take action immediately.
05
Collaborate with other organizations and authorities to share information and resources for dealing with botnet attacks.
Who needs ddos botnets are exploiting?
01
Companies with online services or websites that are vulnerable to DDoS attacks.
02
Government agencies with critical infrastructure that could be targeted by malicious actors.
03
Internet service providers that need to protect their networks and customers from disruptions caused by botnet attacks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit ddos botnets are exploiting online?
pdfFiller not only allows you to edit the content of your files but fully rearrange them by changing the number and sequence of pages. Upload your ddos botnets are exploiting to the editor and make any required adjustments in a couple of clicks. The editor enables you to blackout, type, and erase text in PDFs, add images, sticky notes and text boxes, and much more.
Can I create an electronic signature for the ddos botnets are exploiting in Chrome?
Yes. By adding the solution to your Chrome browser, you may use pdfFiller to eSign documents while also enjoying all of the PDF editor's capabilities in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a photo of your handwritten signature using the extension. Whatever option you select, you'll be able to eSign your ddos botnets are exploiting in seconds.
How do I fill out ddos botnets are exploiting using my mobile device?
Use the pdfFiller mobile app to complete and sign ddos botnets are exploiting on your mobile device. Visit our web page (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, the capabilities you’ll have access to, and the steps to take to get up and running.
What is ddos botnets are exploiting?
DDoS botnets are exploiting vulnerable internet-connected devices to carry out massive distributed denial of service attacks.
Who is required to file ddos botnets are exploiting?
Organizations and individuals who are victims of DDoS botnets attacks are required to report and file the incidents.
How to fill out ddos botnets are exploiting?
DDoS botnets incidents can be reported by providing details of the attack, including source IP addresses, duration, and impact of the attack.
What is the purpose of ddos botnets are exploiting?
The purpose of DDoS botnets exploitation is to disrupt online services, websites, and networks by overwhelming them with malicious traffic.
What information must be reported on ddos botnets are exploiting?
Information such as date and time of the attack, target IP addresses, type of DDoS attack, and any mitigations taken must be reported.
Fill out your ddos botnets are exploiting online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Ddos Botnets Are Exploiting is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.

















