Get the free Cyber Security & Risk Solutions
Show details
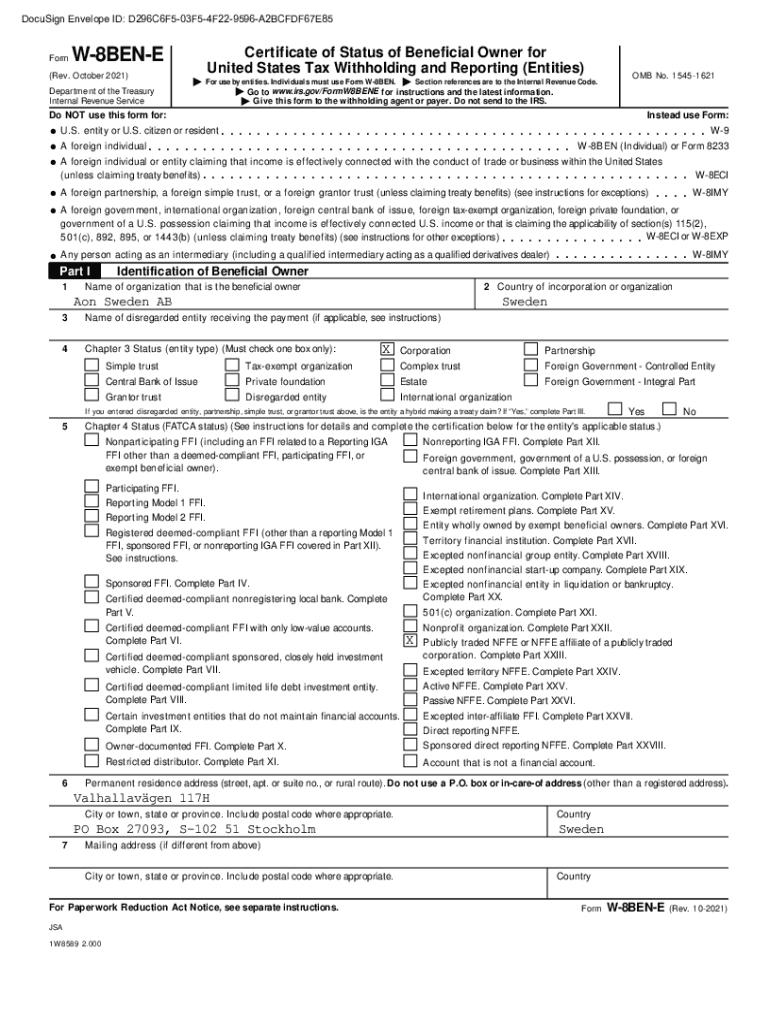
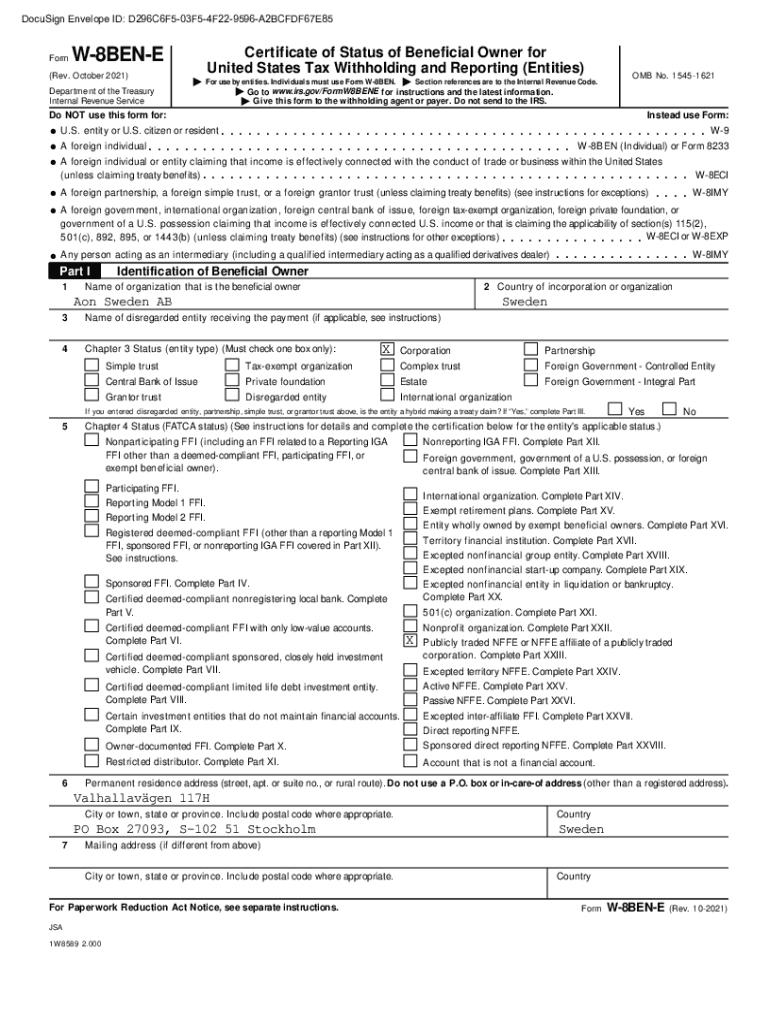
DocuSign Envelope ID: D296C6F503F54F229596A2BCFDF67E85FormW8BENE(Rev. October 2021)Certificate of Status of Beneficial Owner for
United States Tax Withholding and Reporting (Entities)BOMB No. 15451621II
mmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmm
mmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmm
mmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmmm
mmmmDepartment
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber security amp risk

Edit your cyber security amp risk form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyber security amp risk form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing cyber security amp risk online
Use the instructions below to start using our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit cyber security amp risk. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
It's easier to work with documents with pdfFiller than you can have believed. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber security amp risk

How to fill out cyber security amp risk
01
Start by gathering information about the cyber security and risk assessment form. Understand the purpose and requirements of the form.
02
Read and review the instructions provided with the form. Make sure you understand each section and the information needed.
03
Begin by entering your personal information accurately. This may include your name, contact details, and any other relevant information required.
04
Proceed to the specific sections related to cyber security and risk. Provide accurate and detailed information about any security measures you have implemented, previous incidents or breaches, and any risk mitigation strategies.
05
Take your time to fill out each section carefully, ensuring that the information you provide is clear and concise.
06
If required, attach any supporting documentation or evidence to support your responses. This may include security policies, incident reports, or risk analysis documents.
07
Double-check all the information you have entered before submitting the form. Make sure there are no errors or missing details.
08
Once you are satisfied with the completed form, submit it according to the specified instructions. Follow any additional procedures or requirements, such as signing or obtaining approvals.
09
Keep a copy of the filled-out form for your records, in case you need to refer to it in the future.
10
If you have any further questions or concerns, contact the relevant authorities or individuals responsible for the cyber security and risk assessment process.
Who needs cyber security amp risk?
01
Individuals or organizations that handle sensitive or confidential information, such as financial institutions, healthcare providers, and government agencies, need cyber security and risk assessment.
02
Businesses that heavily rely on technology for their operations, such as e-commerce platforms, online service providers, and software development companies, need cyber security and risk measures.
03
Any individual or organization that wants to protect their digital assets, including personal data, intellectual property, or sensitive business information, can benefit from cyber security and risk practices.
04
Companies that value the trust and confidence of their customers or clients need to prioritize cyber security and risk management.
05
Industries that are frequently targeted by cyber threats, such as the financial sector, healthcare industry, and government institutions, require cyber security and risk assessment.
06
Startups and small businesses may also need cyber security and risk measures to safeguard their limited resources and ensure business continuity.
07
Any individual or organization that wants to comply with industry regulations, data protection laws, or contractual requirements related to cyber security and risk must prioritize these practices.
08
Educational institutions, research facilities, and organizations involved in scientific or technological advancements need to ensure the protection of sensitive data and intellectual property through cyber security and risk assessment.
09
Non-profit organizations and charities can also benefit from cyber security and risk measures to protect donor information and maintain their reputation.
10
Essentially, anyone who values the security, integrity, and confidentiality of their digital information and assets needs to consider cyber security and risk management.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I sign the cyber security amp risk electronically in Chrome?
Yes. By adding the solution to your Chrome browser, you may use pdfFiller to eSign documents while also enjoying all of the PDF editor's capabilities in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a photo of your handwritten signature using the extension. Whatever option you select, you'll be able to eSign your cyber security amp risk in seconds.
How can I edit cyber security amp risk on a smartphone?
You can do so easily with pdfFiller’s applications for iOS and Android devices, which can be found at the Apple Store and Google Play Store, respectively. Alternatively, you can get the app on our web page: https://edit-pdf-ios-android.pdffiller.com/. Install the application, log in, and start editing cyber security amp risk right away.
How do I edit cyber security amp risk on an iOS device?
Yes, you can. With the pdfFiller mobile app, you can instantly edit, share, and sign cyber security amp risk on your iOS device. Get it at the Apple Store and install it in seconds. The application is free, but you will have to create an account to purchase a subscription or activate a free trial.
What is cyber security amp risk?
Cyber security and risk refer to the practices and measures taken to protect digital information and systems from cyber threats, as well as the assessment and management of potential risks associated with these threats.
Who is required to file cyber security amp risk?
Organizations that handle sensitive information, such as financial institutions, healthcare providers, and any business that collects personal data, are typically required to file cyber security and risk assessments.
How to fill out cyber security amp risk?
To fill out a cyber security and risk assessment, one must gather relevant data about the organization's security measures, identify potential vulnerabilities, assess the impact of various risks, and provide recommendations for mitigation.
What is the purpose of cyber security amp risk?
The purpose of cyber security and risk assessments is to identify vulnerabilities, protect sensitive information, comply with regulations, and reduce the likelihood and impact of cyber threats.
What information must be reported on cyber security amp risk?
Information that must be reported includes the organization's security policies, identified vulnerabilities, risk assessments, incident response plans, and measures taken to mitigate risks.
Fill out your cyber security amp risk online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Security Amp Risk is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















