Get the free Zero Trust Maturity Model Version 2.0
Show details
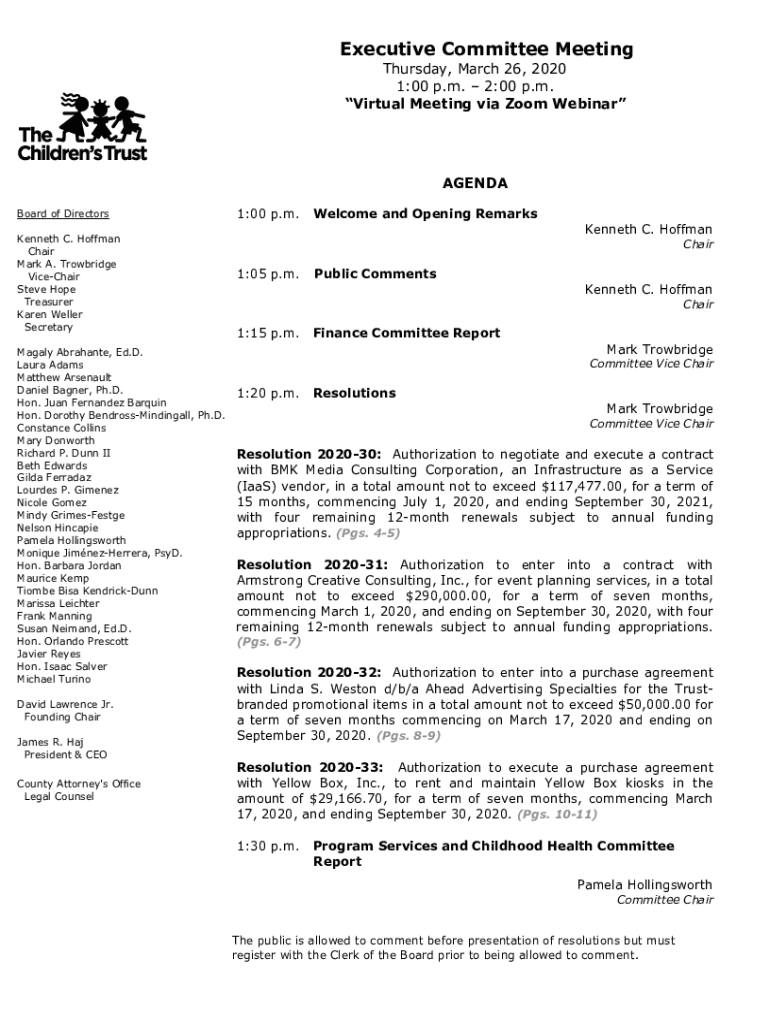
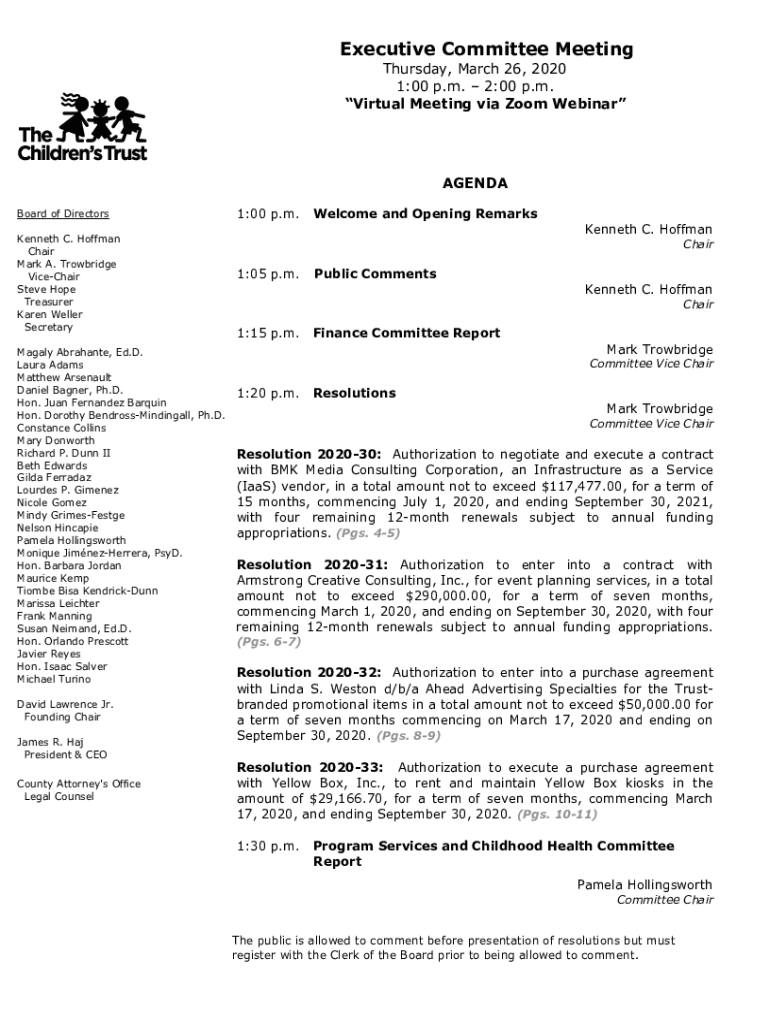
Executive Committee Meeting
Thursday, March 26, 2020
1:00 p.m. 2:00 p.m.
Virtual Meeting via Zoom WebinarAGENDA
1:00 p.m. Board of Directors
Kenneth C. Hoffman
Chair
Mark A. Trow bridge
Timeshare
Steve
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign zero trust maturity model

Edit your zero trust maturity model form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your zero trust maturity model form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing zero trust maturity model online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit zero trust maturity model. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out zero trust maturity model

How to fill out zero trust maturity model
01
To fill out the zero trust maturity model, follow these steps:
02
Understand the components of the zero trust maturity model, which include identity and access management, network security, data protection, and security analytics.
03
Assess your current level of maturity in each component by evaluating your existing security controls, processes, and technologies.
04
Identify the gaps between your current state and the desired state of zero trust maturity in each component.
05
Develop a roadmap that outlines the steps and actions required to bridge the gaps and improve your maturity level.
06
Implement the necessary changes, such as enhancing authentication methods, implementing micro-segmentation, and deploying advanced threat detection and response systems.
07
Continuously monitor and reassess your progress to ensure ongoing improvement and alignment with the zero trust principles.
08
Regularly update the zero trust maturity model based on evolving threats, technologies, and business requirements.
09
Collaborate with stakeholders, security teams, and other relevant departments to ensure a comprehensive and holistic approach to zero trust.
10
Document the process and outcomes of filling out the zero trust maturity model for future reference and audit purposes.
Who needs zero trust maturity model?
01
The zero trust maturity model is beneficial for organizations that value security and want to improve their overall security posture. It is particularly relevant for:
02
- Organizations with complex and distributed IT environments.
03
- Organizations that handle sensitive or confidential data.
04
- Organizations that prioritize protecting against advanced and persistent threats.
05
- Organizations that are transitioning to cloud-based or hybrid environments.
06
- Organizations that want to establish a strong security foundation based on zero trust principles.
07
- Organizations that want to ensure compliance with industry regulations and standards.
08
- Organizations that recognize the importance of continuous improvement and adaptability in response to evolving cyber threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit zero trust maturity model from Google Drive?
Using pdfFiller with Google Docs allows you to create, amend, and sign documents straight from your Google Drive. The add-on turns your zero trust maturity model into a dynamic fillable form that you can manage and eSign from anywhere.
How can I send zero trust maturity model to be eSigned by others?
zero trust maturity model is ready when you're ready to send it out. With pdfFiller, you can send it out securely and get signatures in just a few clicks. PDFs can be sent to you by email, text message, fax, USPS mail, or notarized on your account. You can do this right from your account. Become a member right now and try it out for yourself!
How do I edit zero trust maturity model on an iOS device?
Use the pdfFiller app for iOS to make, edit, and share zero trust maturity model from your phone. Apple's store will have it up and running in no time. It's possible to get a free trial and choose a subscription plan that fits your needs.
What is zero trust maturity model?
The zero trust maturity model is a framework that helps organizations assess and improve their security posture by implementing zero trust principles, which focus on strict access controls, continuous verification of users and devices, and minimizing the trust placed on internal networks.
Who is required to file zero trust maturity model?
Organizations that are subject to federal regulations or that participate in certain cybersecurity programs may be required to file the zero trust maturity model assessments as part of their compliance obligations.
How to fill out zero trust maturity model?
To fill out the zero trust maturity model, organizations should evaluate their current security practices against the model's criteria, assign maturity levels to different domains, and document their findings and remediation plans to achieve higher levels of maturity.
What is the purpose of zero trust maturity model?
The purpose of the zero trust maturity model is to provide a structured approach for organizations to understand their current security capabilities, identify gaps, and develop a roadmap for implementing zero trust principles to enhance their cybersecurity defenses.
What information must be reported on zero trust maturity model?
Organizations must report their current maturity levels across various domains of the zero trust framework, including identity verification, device security, data protection, and incident response capabilities, along with any plans for improvement and timelines.
Fill out your zero trust maturity model online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Zero Trust Maturity Model is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.