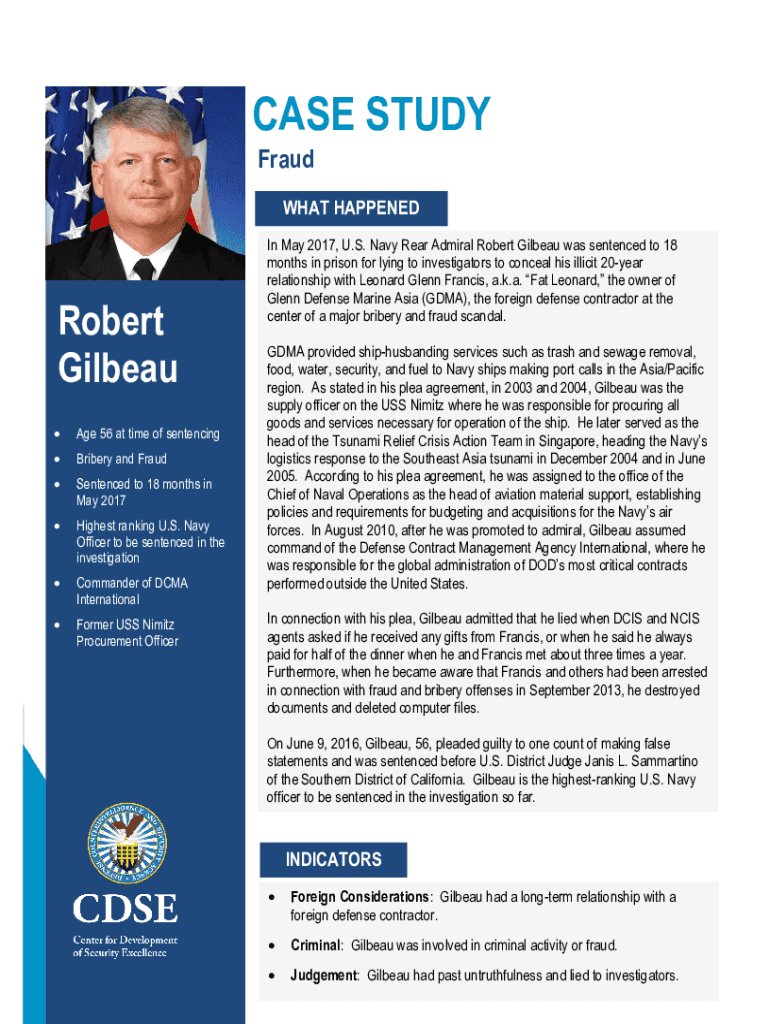
Get the free Insider Threat Case Study: Robert Gilbeau
Show details
CASE STUDY
Fraught HAPPENED Robert
GilbeauFIRST/ LAST
NAME
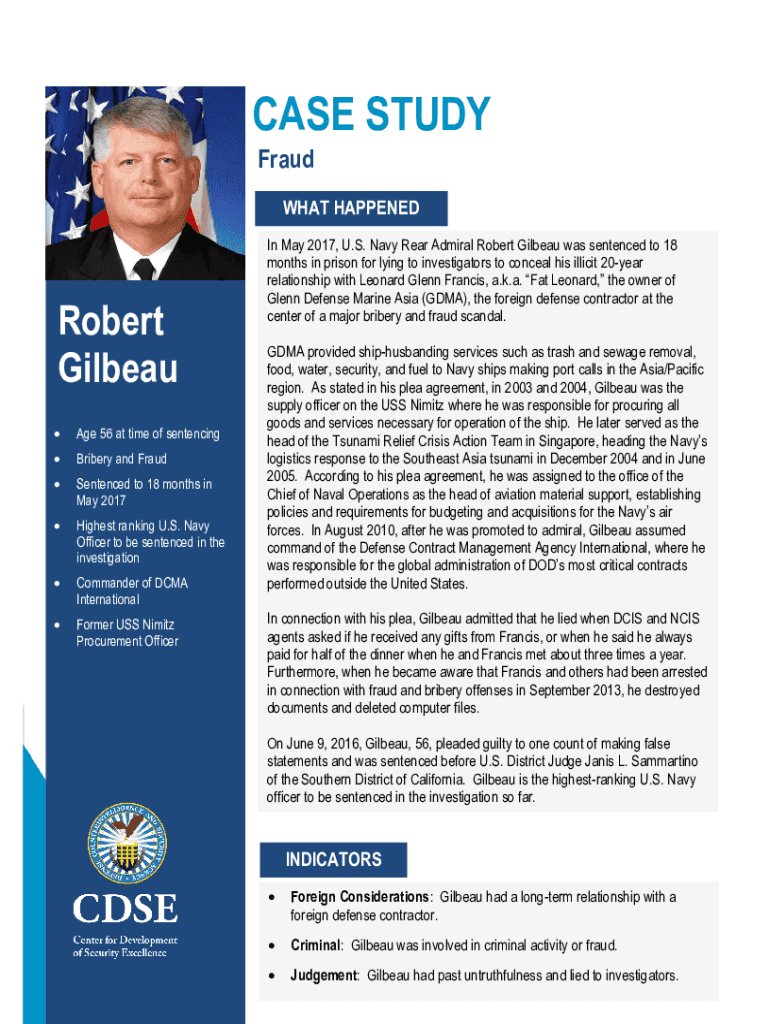
Age 56 at time of sentencingBribery and FraudSentenced to 18 months in
May 2017Highest ranking U.S. Navy
Officer to be sentenced in the
investigationCommander
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign insider threat case study
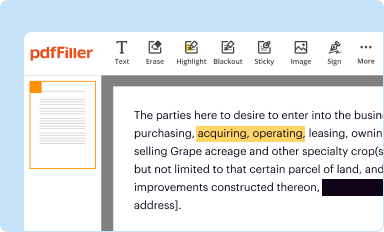
Edit your insider threat case study form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
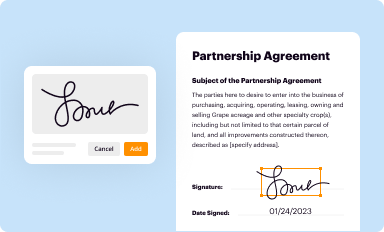
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
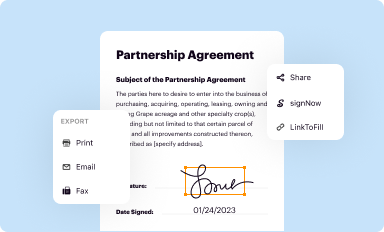
Share your form instantly
Email, fax, or share your insider threat case study form via URL. You can also download, print, or export forms to your preferred cloud storage service.
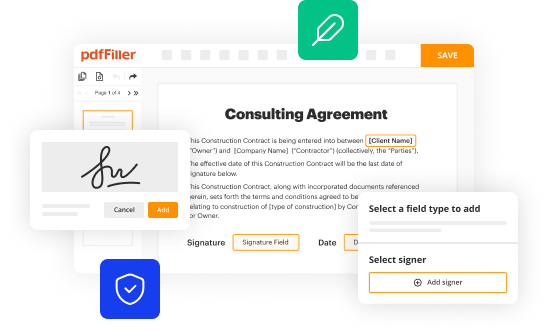
How to edit insider threat case study online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit insider threat case study. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out insider threat case study
How to fill out insider threat case study
01
Start by identifying the purpose of the insider threat case study. Determine what specific information or insights you want to capture and convey through the case study.
02
Gather relevant data and information related to the insider threat incident or incidents you want to document in the case study. This may include incident reports, employee interviews, surveillance footage, and any other supporting evidence.
03
Structure the case study in a clear and organized manner. Use headings and subheadings to divide the content into sections such as background information, incident details, contributing factors, impact, response measures taken, and lessons learned.
04
Provide a brief overview of the organization or company involved in the case study. Include relevant details such as its industry, size, and any unique aspects that may impact the insider threat scenario.
05
Describe the insider threat incident(s) in detail, including the nature of the threats, the individuals involved, their motivations, and any indicators or red flags that were missed or ignored.
06
Analyze the contributing factors that allowed the insider threat to occur. This may involve examining weaknesses in policies, procedures, employee training, or technology systems.
07
Discuss the impact of the insider threat on the organization, such as financial losses, damage to reputation, or compromised data or systems.
08
Detail the response measures taken by the organization to mitigate the insider threat incident and prevent future occurrences. This may include changes in policies, enhanced security measures, or improved training programs.
09
Provide insights and lessons learned from the insider threat case study. Discuss best practices for preventing, detecting, and responding to insider threats, as well as any recommendations for other organizations facing similar risks.
10
Conclude the case study by summarizing the key findings and emphasizing the importance of proactive insider threat detection and prevention strategies.
Who needs insider threat case study?
01
Organizations or companies with sensitive or valuable information that could be targeted by insiders.
02
Security professionals and consultants who specialize in insider threat detection and prevention.
03
Law enforcement agencies and investigators involved in handling insider threat incidents and conducting related investigations.
04
Human resources professionals responsible for employee monitoring and risk management.
05
Corporate executives and decision-makers who need to understand the potential impact of insider threats on their organizations.
06
IT and cybersecurity professionals seeking to enhance their knowledge and skills in dealing with insider threats.
07
Academics and researchers studying the field of insider threat management and seeking real-world case studies for analysis and reference.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get insider threat case study?
The premium pdfFiller subscription gives you access to over 25M fillable templates that you can download, fill out, print, and sign. The library has state-specific insider threat case study and other forms. Find the template you need and change it using powerful tools.
Can I create an electronic signature for the insider threat case study in Chrome?
Yes. With pdfFiller for Chrome, you can eSign documents and utilize the PDF editor all in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a handwritten signature image. You may eSign your insider threat case study in seconds.
How do I fill out the insider threat case study form on my smartphone?
Use the pdfFiller mobile app to complete and sign insider threat case study on your mobile device. Visit our web page (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, the capabilities you’ll have access to, and the steps to take to get up and running.
What is insider threat case study?
An insider threat case study examines incidents where individuals within an organization misuse their access to sensitive information, posing security risks. It analyzes real cases to identify vulnerabilities and improve security protocols.
Who is required to file insider threat case study?
Organizations involved in handling sensitive, proprietary, or classified information are required to file insider threat case studies to document and analyze potential threats from within.
How to fill out insider threat case study?
To fill out an insider threat case study, gather detailed information about the incident, including timelines, involved parties, actions taken, and outcomes. Follow your organization’s standard reporting formats and provide all necessary documentation.
What is the purpose of insider threat case study?
The purpose of an insider threat case study is to enhance organizational security by identifying weaknesses, analyzing threats, and developing strategies to prevent future incidents.
What information must be reported on insider threat case study?
Reported information should include the nature of the threat, individuals involved, methods of detection, response actions taken, and lessons learned to mitigate future risks.
Fill out your insider threat case study online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Insider Threat Case Study is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.