Get the free Identity-based policy examples for Amazon CloudFront
Show details
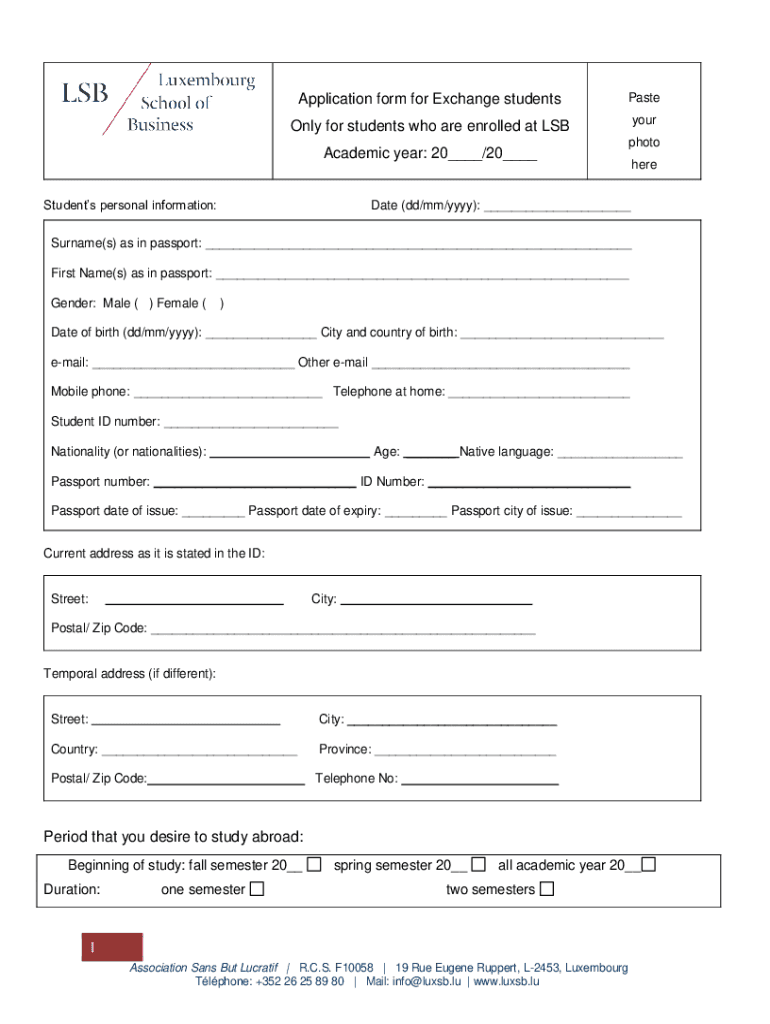
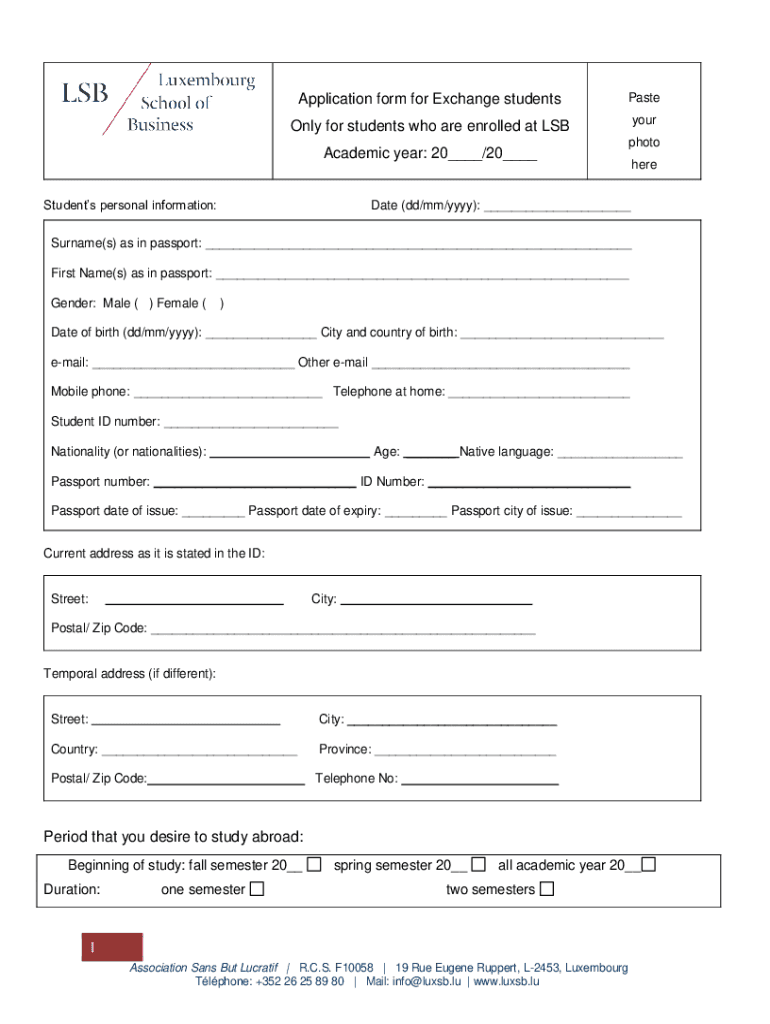
Application form for Exchange studentsPasteOnly for students who are enrolled at LSByour photoAcademic year: 20___/20___ Students personal information:hereDate (dd/mm/yyyy): ___Surname(s) as in passport:
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign identity-based policy examples for
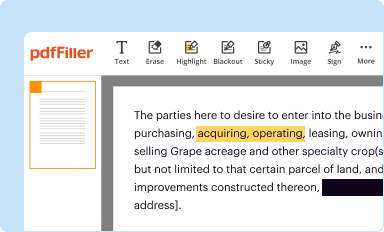
Edit your identity-based policy examples for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
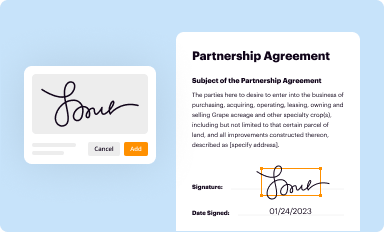
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
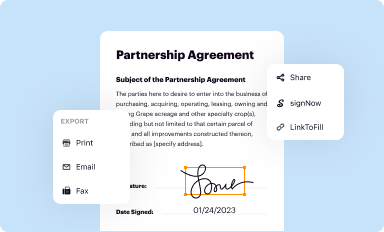
Share your form instantly
Email, fax, or share your identity-based policy examples for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
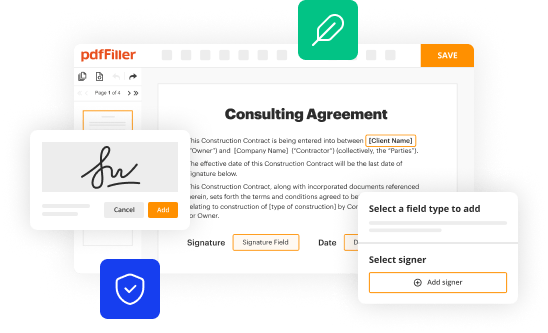
How to edit identity-based policy examples for online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit identity-based policy examples for. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out identity-based policy examples for
How to fill out identity-based policy examples for
01
Start by understanding the purpose of identity-based policy examples. These examples are used to demonstrate how to define access policies based on user identity.
02
Identify the specific resources or services for which you want to create identity-based policy examples.
03
Define the permissions or actions that users with specific identities should be allowed or denied on these resources or services.
04
Determine the conditions or qualifiers under which these permissions or denials should apply for different user identities.
05
Structure the policy examples in a format compatible with the identity-based policy framework you are using (e.g., JSON, YAML, etc.).
06
Test the policy examples to ensure they work as expected.
07
Document the usage and details of the identity-based policy examples for future reference or sharing with others.
Who needs identity-based policy examples for?
01
Developers: Developers who are responsible for implementing access control systems or applications that rely on user identity-based policies can benefit from identity-based policy examples as a reference.
02
Security Professionals: Security professionals involved in defining and enforcing access controls in organizations can use identity-based policy examples to ensure the correct and secure implementation of policies.
03
System Administrators: System administrators who manage user access to resources or services can utilize identity-based policy examples to effectively configure and enforce access rules.
04
Auditors: Auditors who need to validate the compliance of access controls with regulations and policies can refer to identity-based policy examples for verification purposes.
05
Organizations: Any organization that wants to establish consistent and well-defined access controls based on user identity can use identity-based policy examples as a starting point.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit identity-based policy examples for online?
The editing procedure is simple with pdfFiller. Open your identity-based policy examples for in the editor. You may also add photos, draw arrows and lines, insert sticky notes and text boxes, and more.
How do I fill out identity-based policy examples for using my mobile device?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign identity-based policy examples for and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
Can I edit identity-based policy examples for on an Android device?
The pdfFiller app for Android allows you to edit PDF files like identity-based policy examples for. Mobile document editing, signing, and sending. Install the app to ease document management anywhere.
What is identity-based policy examples for?
Identity-based policy examples are used to establish guidelines and regulations that govern the identification and verification of individuals within systems, such as healthcare, finance, or security.
Who is required to file identity-based policy examples for?
Organizations that handle personal data, such as financial institutions, healthcare providers, and governmental agencies are typically required to file identity-based policy examples.
How to fill out identity-based policy examples for?
To fill out identity-based policy examples, organizations should outline their identification processes, data storage methods, security measures, and compliance with relevant laws and regulations.
What is the purpose of identity-based policy examples for?
The purpose of identity-based policy examples is to ensure the protection of personal information, to comply with legal requirements, and to foster trust among users regarding data handling practices.
What information must be reported on identity-based policy examples for?
The information that must be reported includes identity verification processes, data protection measures, user consent protocols, and compliance with applicable regulations.
Fill out your identity-based policy examples for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Identity-Based Policy Examples For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.