Get the free transition from using penetration grade specifications to ... - open alberta
Show details
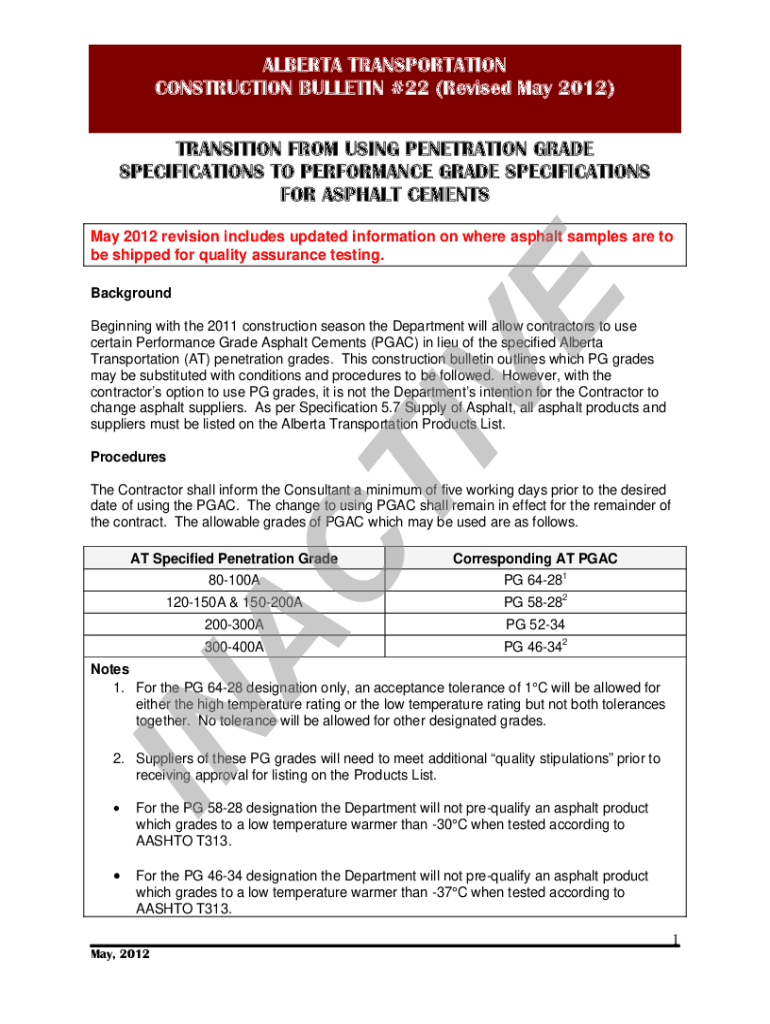
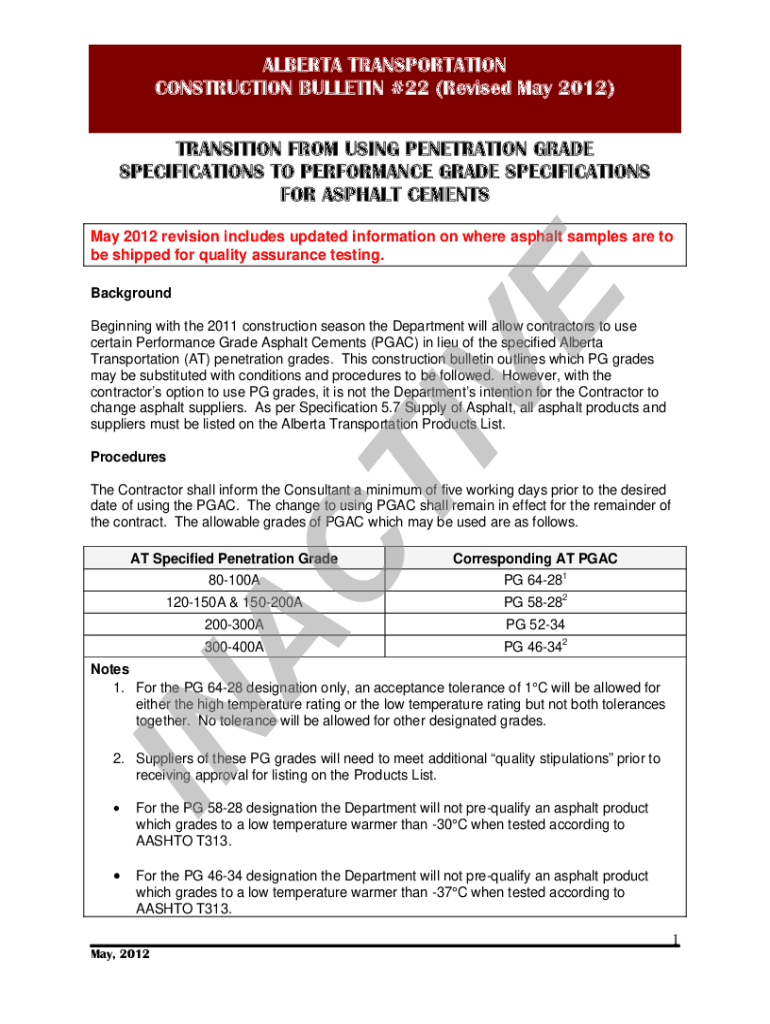
ALBERTA TRANSPORTATION CONSTRUCTION BULLETIN #22 (Revised May 2012) TRANSITION FROM USING PENETRATION GRADE SPECIFICATIONS TO PERFORMANCE GRADE SPECIFICATIONS FOR ASPHALT CEMENTS May 2012 revision
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign transition from using penetration

Edit your transition from using penetration form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your transition from using penetration form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit transition from using penetration online
Use the instructions below to start using our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit transition from using penetration. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out transition from using penetration

How to fill out transition from using penetration
01
Start by thoroughly understanding the reasons for transitioning from using penetration.
02
Assess the current penetration techniques being used and evaluate their effectiveness.
03
Research and identify alternative methods or technologies that can replace or enhance penetration techniques.
04
Develop a transition plan with clear goals, timelines, and milestones.
05
Communicate the transition plan to all relevant stakeholders and ensure their buy-in and support.
06
Provide training and resources to employees or teams involved in the transition process.
07
Begin implementing the new methods or technologies gradually, allowing for testing and adjustments.
08
Monitor and measure the effectiveness of the transition, making any necessary refinements.
09
Provide ongoing support and guidance to teams during the transition period.
10
Evaluate the success of the transition and celebrate milestones or achievements.
11
Continuously assess and improve the new methods or technologies to ensure long-term success.
Who needs transition from using penetration?
01
Any individual or organization that currently relies on penetration techniques and wants to improve their security measures.
02
Companies or individuals who have experienced security breaches or vulnerabilities due to traditional penetration techniques.
03
Organizations seeking to align with industry best practices and comply with regulations or standards.
04
IT professionals looking to enhance their knowledge and skills in the field of cybersecurity.
05
Businesses or individuals considering a proactive approach to security rather than a reactive one.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify transition from using penetration without leaving Google Drive?
Simplify your document workflows and create fillable forms right in Google Drive by integrating pdfFiller with Google Docs. The integration will allow you to create, modify, and eSign documents, including transition from using penetration, without leaving Google Drive. Add pdfFiller’s functionalities to Google Drive and manage your paperwork more efficiently on any internet-connected device.
How do I edit transition from using penetration in Chrome?
Install the pdfFiller Google Chrome Extension in your web browser to begin editing transition from using penetration and other documents right from a Google search page. When you examine your documents in Chrome, you may make changes to them. With pdfFiller, you can create fillable documents and update existing PDFs from any internet-connected device.
Can I edit transition from using penetration on an iOS device?
You certainly can. You can quickly edit, distribute, and sign transition from using penetration on your iOS device with the pdfFiller mobile app. Purchase it from the Apple Store and install it in seconds. The program is free, but in order to purchase a subscription or activate a free trial, you must first establish an account.
What is transition from using penetration?
The transition from using penetration refers to the process of changing practices or policies regarding penetration testing or vulnerability assessments within an organization, often in response to updated regulations, technological changes, or improved security standards.
Who is required to file transition from using penetration?
Organizations that conduct penetration testing or are subject to regulatory requirements related to cybersecurity may be required to file a transition report, typically including IT and security departments.
How to fill out transition from using penetration?
To fill out the transition report, organizations should provide details about their current penetration testing practices, outline the changes being made, document compliance with applicable standards, and specify timelines and responsible personnel.
What is the purpose of transition from using penetration?
The purpose of the transition is to ensure that organizations adapt to evolving cybersecurity threats and compliance requirements, thereby enhancing their overall security posture.
What information must be reported on transition from using penetration?
The report should include information on current practices, changes to be implemented, compliance status, timelines, risk assessments, and roles and responsibilities.
Fill out your transition from using penetration online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Transition From Using Penetration is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















