Get the free 30 Exploit-DB(http://exploit-db
Show details
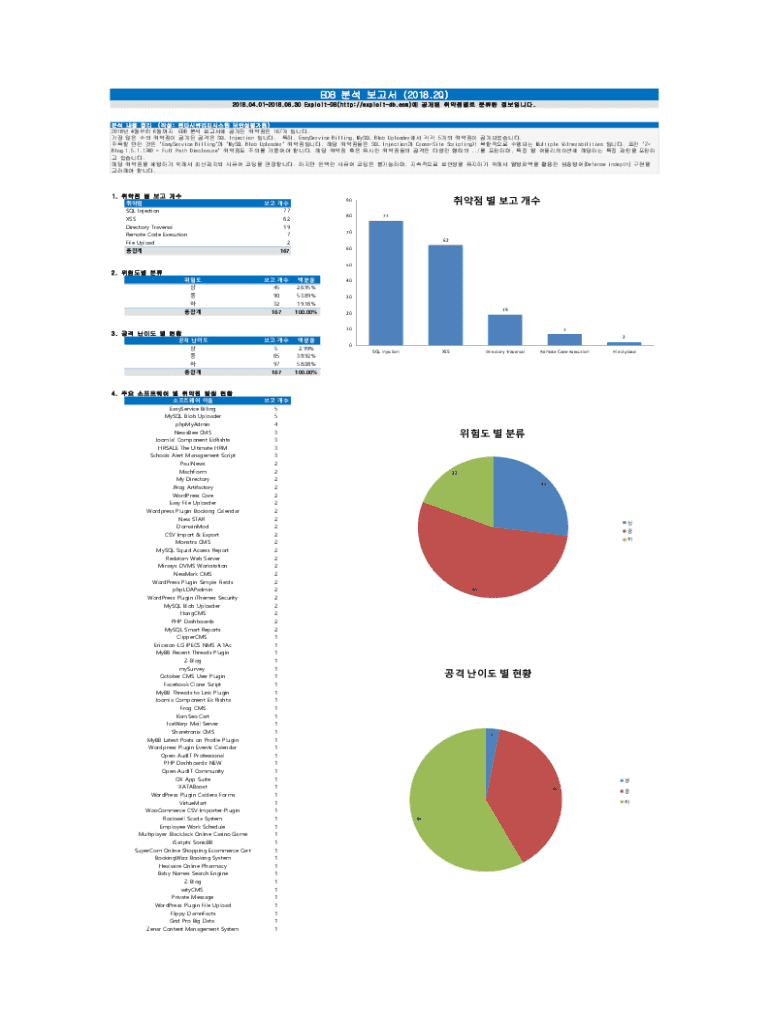
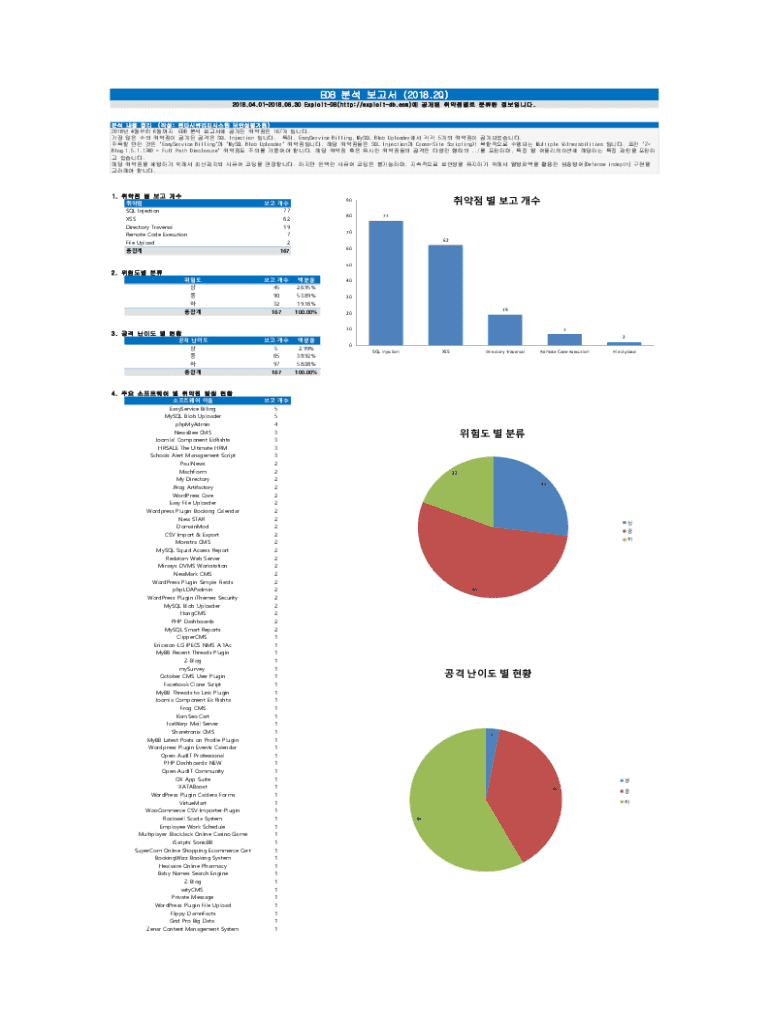
EDB (2018.2Q)
2018.04.012018.06.30 ExploitDB(http://exploitdb.com) . (: )
2018 4 6 EDB 167 .
SQL Injection . , EasyService Billing, MySQL Blob Uploader 5
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign 30 exploit-dbhttpexploit-db

Edit your 30 exploit-dbhttpexploit-db form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your 30 exploit-dbhttpexploit-db form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing 30 exploit-dbhttpexploit-db online
Use the instructions below to start using our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit 30 exploit-dbhttpexploit-db. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out 30 exploit-dbhttpexploit-db

How to fill out 30 exploit-dbhttpexploit-db
01
To fill out the 30 exploit-dbhttpexploit-db, follow these steps:
02
Access the 30 exploit-dbhttpexploit-db website.
03
Create an account if you don't have one.
04
Log in to your account.
05
Navigate to the exploit-db section.
06
Click on the 'Submit Exploit' button.
07
Fill out the required fields, such as the exploit details, CVE number (if applicable), affected software, and exploit code.
08
Provide any additional information or notes in the relevant sections.
09
Click on the 'Submit' or 'Publish' button to submit your exploit to the 30 exploit-dbhttpexploit-db database.
10
Wait for the exploit to be reviewed and approved by the 30 exploit-dbhttpexploit-db team.
11
Once approved, your exploit will be published and available for others to access and use.
Who needs 30 exploit-dbhttpexploit-db?
01
Anyone interested in cybersecurity, penetration testing, or vulnerability research can benefit from the 30 exploit-dbhttpexploit-db database.
02
Security researchers, ethical hackers, and IT professionals often rely on this database to find and understand different exploits.
03
Organizations and individuals concerned about their software's security can also use the database to identify vulnerabilities and take appropriate actions to mitigate them.
04
Moreover, developers and software vendors can utilize the 30 exploit-dbhttpexploit-db to stay updated about known vulnerabilities and develop patches or countermeasures.
05
In summary, anyone involved in cybersecurity, software development, or IT security can find value in the 30 exploit-dbhttpexploit-db database.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my 30 exploit-dbhttpexploit-db directly from Gmail?
Using pdfFiller's Gmail add-on, you can edit, fill out, and sign your 30 exploit-dbhttpexploit-db and other papers directly in your email. You may get it through Google Workspace Marketplace. Make better use of your time by handling your papers and eSignatures.
How can I get 30 exploit-dbhttpexploit-db?
The premium version of pdfFiller gives you access to a huge library of fillable forms (more than 25 million fillable templates). You can download, fill out, print, and sign them all. State-specific 30 exploit-dbhttpexploit-db and other forms will be easy to find in the library. Find the template you need and use advanced editing tools to make it your own.
How do I complete 30 exploit-dbhttpexploit-db on an iOS device?
pdfFiller has an iOS app that lets you fill out documents on your phone. A subscription to the service means you can make an account or log in to one you already have. As soon as the registration process is done, upload your 30 exploit-dbhttpexploit-db. You can now use pdfFiller's more advanced features, like adding fillable fields and eSigning documents, as well as accessing them from any device, no matter where you are in the world.
What is 30 exploit-dbhttpexploit-db?
The '30 exploit-dbhttpexploit-db' typically refers to a specific database or reporting mechanism that addresses security vulnerabilities in web applications, often used by security professionals to manage and track exploits.
Who is required to file 30 exploit-dbhttpexploit-db?
Organizations and individuals who manage or develop web applications and are aware of vulnerabilities related to their systems are generally required to file or report findings in relation to '30 exploit-dbhttpexploit-db'.
How to fill out 30 exploit-dbhttpexploit-db?
To fill out the '30 exploit-dbhttpexploit-db', one should collect relevant details about the exploit, including its nature, affected systems, potential impacts, and proposed mitigation strategies, and complete the required fields according to the provided guidelines.
What is the purpose of 30 exploit-dbhttpexploit-db?
The purpose of '30 exploit-dbhttpexploit-db' is to document and report security vulnerabilities and exploits, facilitating better understanding and mitigation of risks within web applications.
What information must be reported on 30 exploit-dbhttpexploit-db?
The information typically reported on '30 exploit-dbhttpexploit-db' includes the description of the exploit, affected systems, severity level, evidence of the exploit, recommendations for remediation, and any related URL or resources.
Fill out your 30 exploit-dbhttpexploit-db online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
30 Exploit-Dbhttpexploit-Db is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















