Get the free Technology Against Terrorism. Terrorism is not a new phenomenon, but it has become m...
Show details
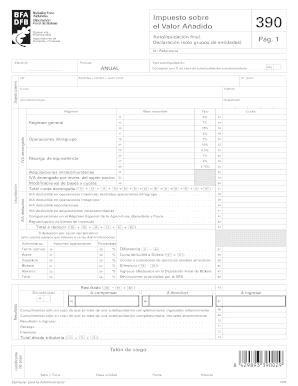
VAS1 9990301026Lt\'.5/ eingPreceding PageBilank0.U CEC 00) 0.\' 00)0)C .o C.) \'ioC\'a CIC 0))0.Foreword Terrorism is not a new phenomenon, but it has become more prominent during the past two decades.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign technology against terrorism terrorism

Edit your technology against terrorism terrorism form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your technology against terrorism terrorism form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit technology against terrorism terrorism online
To use the professional PDF editor, follow these steps below:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit technology against terrorism terrorism. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out technology against terrorism terrorism

How to fill out technology against terrorism terrorism
01
To fill out technology against terrorism, follow these steps:
02
Identify the specific technological aspects that can be used to combat terrorism, such as data analytics, artificial intelligence, machine learning, and cybersecurity.
03
Develop robust systems and tools that can detect, analyze, and prevent terrorist activities in real-time using advanced technology.
04
Collaborate with intelligence agencies, law enforcement bodies, and government organizations to gather relevant data and insights regarding terrorist threats.
05
Continuously update and improve the technology against terrorism by staying up-to-date with the latest advancements in the field.
06
Conduct thorough testing and evaluation of the technology to ensure its effectiveness and reliability in countering terrorist activities.
07
Establish strong security protocols and measures to safeguard the technology against potential misuse or infiltration by terrorists.
08
Train and educate personnel on how to utilize and operate the technology effectively in their counter-terrorism efforts.
09
Foster international cooperation and information sharing to enhance the global effectiveness of technology against terrorism.
10
Monitor and analyze the impact of the technology against terrorism to identify areas for improvement and further innovation.
11
Continuously adapt and evolve the technology against terrorism to stay ahead of evolving terrorist strategies and tactics.
Who needs technology against terrorism terrorism?
01
Technology against terrorism is needed by various stakeholders, including:
02
- Government agencies and law enforcement bodies responsible for maintaining national security and combating terrorism.
03
- Intelligence agencies and counter-terrorism units that gather and analyze information on potential threats.
04
- Military organizations involved in counter-insurgency operations and protecting nations from terrorist attacks.
05
- Private sector companies operating critical infrastructure or providing essential services susceptible to terrorist attacks.
06
- Non-governmental organizations (NGOs) working on humanitarian missions or providing aid in conflict zones.
07
- Citizens and communities affected by terrorism, who rely on technology to ensure their safety and prevent future attacks.
08
- International alliances and organizations dedicated to combatting terrorism and promoting peace and security globally.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send technology against terrorism terrorism to be eSigned by others?
Once you are ready to share your technology against terrorism terrorism, you can easily send it to others and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail, or notarize it online. You can do all of this without ever leaving your account.
How do I fill out the technology against terrorism terrorism form on my smartphone?
The pdfFiller mobile app makes it simple to design and fill out legal paperwork. Complete and sign technology against terrorism terrorism and other papers using the app. Visit pdfFiller's website to learn more about the PDF editor's features.
How can I fill out technology against terrorism terrorism on an iOS device?
Install the pdfFiller iOS app. Log in or create an account to access the solution's editing features. Open your technology against terrorism terrorism by uploading it from your device or online storage. After filling in all relevant fields and eSigning if required, you may save or distribute the document.
What is technology against terrorism terrorism?
Technology against terrorism refers to the utilization of advanced tools, software, and systems designed to prevent, detect, and respond to terrorist activities. This includes surveillance systems, data analysis, and communication technology aimed at enhancing national security.
Who is required to file technology against terrorism terrorism?
Entities involved in activities related to national security, law enforcement, and certain businesses that may be impacted by terrorism, such as transportation and critical infrastructure sectors, may be required to file disclosures related to technology against terrorism.
How to fill out technology against terrorism terrorism?
To fill out the technology against terrorism filing, one typically needs to complete specific forms provided by relevant government authorities, detailing the types of technology utilized, their purpose, and how they are used in relation to combating terrorism.
What is the purpose of technology against terrorism terrorism?
The purpose of technology against terrorism is to enhance the ability of governments and organizations to prevent terrorist attacks, safeguard citizens, and respond effectively to incidents of terrorism.
What information must be reported on technology against terrorism terrorism?
Information required to be reported may include the types of technology used, their operational capabilities, data privacy measures, and any incidents or actions taken in relation to counter-terrorism efforts.
Fill out your technology against terrorism terrorism online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Technology Against Terrorism Terrorism is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.