Get the free Exploring Qualcomm's Secure Execution Environment
Show details
REF: 2022/SEC/02/01 7 February 2022Dear Parents / Guardians, Please take time to read through this letter and acknowledge receipt of the letter in Annex A. Please return the acknowledgment to the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign exploring qualcomms secure execution

Edit your exploring qualcomms secure execution form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your exploring qualcomms secure execution form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing exploring qualcomms secure execution online
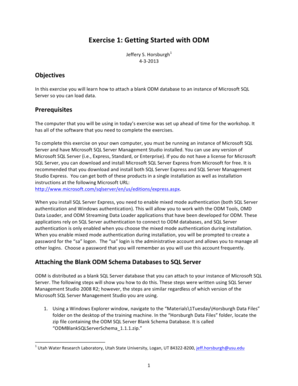
Use the instructions below to start using our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit exploring qualcomms secure execution. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
It's easier to work with documents with pdfFiller than you can have believed. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out exploring qualcomms secure execution

How to fill out exploring qualcomms secure execution
01
To fill out exploring Qualcomm's secure execution, follow these steps:
02
Start by understanding the purpose of exploring Qualcomm's secure execution. This involves understanding the secure execution environment and its benefits.
03
Familiarize yourself with the documentation and resources provided by Qualcomm. This could include whitepapers, technical guides, or SDKs.
04
Begin by exploring the basics of secure execution, such as understanding the underlying hardware, software architecture, and security measures implemented by Qualcomm.
05
Understand the security requirements and constraints specific to your use case or application. This will help you tailor the exploration process accordingly.
06
Dive deeper into the various components and features of Qualcomm's secure execution. This may include understanding secure boot, trusted execution environments (TEEs), or secure enclaves.
07
Experiment with sample code or use cases provided by Qualcomm to gain hands-on experience with secure execution. This could involve writing and executing code within the secure execution environment.
08
Test and validate the security measures implemented by Qualcomm by performing vulnerability assessments, penetration tests, or code reviews.
09
Stay updated with the latest developments and advancements in exploring Qualcomm's secure execution. This may involve joining relevant communities, attending conferences, or reviewing Qualcomm's security updates.
10
Share your findings, experiences, and insights with the Qualcomm community to contribute to the overall understanding and improvement of secure execution.
11
Seek assistance or guidance from Qualcomm's support channels or forums if you encounter any difficulties or have specific questions related to exploring secure execution.
12
Remember to approach exploring Qualcomm's secure execution with caution, respect the privacy and security of the system, and adhere to any applicable terms and conditions.
Who needs exploring qualcomms secure execution?
01
Exploring Qualcomm's secure execution can benefit various stakeholders including:
02
- Developers and software engineers who want to leverage the security features provided by Qualcomm's hardware
03
- Cryptographers and security researchers who specialize in analyzing and improving secure execution environments
04
- System architects and designers who need to understand the capabilities and limitations of Qualcomm's secure execution for designing secure systems
05
- Companies or organizations developing trusted applications that require a secure execution environment
06
- Mobile device manufacturers who want to ensure the security of their devices by utilizing Qualcomm's secure execution
07
- Individuals or entities interested in assessing and auditing the security of Qualcomm's secure execution for compliance or regulatory purposes
08
Ultimately, anyone involved in the development, analysis, or utilization of secure execution can benefit from exploring Qualcomm's secure execution.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send exploring qualcomms secure execution to be eSigned by others?
Once you are ready to share your exploring qualcomms secure execution, you can easily send it to others and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail, or notarize it online. You can do all of this without ever leaving your account.
Can I create an eSignature for the exploring qualcomms secure execution in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your exploring qualcomms secure execution directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
How do I fill out the exploring qualcomms secure execution form on my smartphone?
You can quickly make and fill out legal forms with the help of the pdfFiller app on your phone. Complete and sign exploring qualcomms secure execution and other documents on your mobile device using the application. If you want to learn more about how the PDF editor works, go to pdfFiller.com.
What is exploring Qualcomm's secure execution?
Exploring Qualcomm's secure execution refers to the investigation and understanding of Qualcomm's technologies and methods that ensure the security and integrity of data execution within devices.
Who is required to file exploring Qualcomm's secure execution?
Entities utilizing Qualcomm's secure execution technology in their products or services are typically required to file exploring Qualcomm's secure execution.
How to fill out exploring Qualcomm's secure execution?
Filling out exploring Qualcomm's secure execution involves completing specific documentation that outlines the use of Qualcomm's secure execution technologies and detailing compliance with relevant security protocols.
What is the purpose of exploring Qualcomm's secure execution?
The purpose is to ensure that manufacturers and developers understand the security frameworks in place to protect sensitive data and prevent unauthorized access within their devices.
What information must be reported on exploring Qualcomm's secure execution?
Information that must be reported includes the implementation details of secure execution technology, any identified vulnerabilities, compliance with security standards, and usage statistics.
Fill out your exploring qualcomms secure execution online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Exploring Qualcomms Secure Execution is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.