Get the free Top 10 Malware Which Targeted Crypto Users
Show details
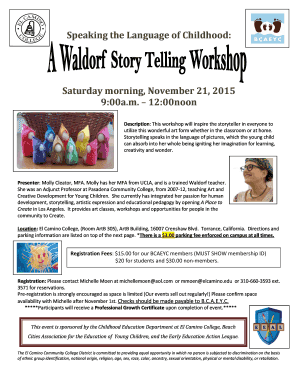
Cryptolocker can cause serious damage to personal and business computers. By always creating a physically separate backup of critical files, regularly running antivirus scans and avoiding unknown
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign top 10 malware which

Edit your top 10 malware which form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your top 10 malware which form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit top 10 malware which online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit top 10 malware which. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
It's easier to work with documents with pdfFiller than you can have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out top 10 malware which

How to fill out top 10 malware which
01
Start by identifying the top 10 malware threats based on current reports and research.
02
Gather information on each malware threat, including the symptoms, characteristics, and potential impact.
03
Create a spreadsheet or document to organize the information for easy reference.
04
For each malware threat, list the name, type, distribution method, and recommended protection measures.
05
Include any additional details such as known vulnerabilities, affected systems, and common targets.
06
Regularly update the top 10 malware list to reflect new threats and changes in the threat landscape.
07
Share the top 10 malware list with relevant stakeholders, such as IT security teams, to ensure awareness and preparedness.
08
Train employees on how to recognize and respond to the top 10 malware threats to prevent infections and minimize damage.
09
Monitor for any signs of the top 10 malware threats within your organization's network and systems.
10
Work with cybersecurity experts and utilize threat intelligence sources to stay informed and protected against evolving malware threats.
Who needs top 10 malware which?
01
IT professionals and cybersecurity experts who are responsible for protecting their organization's network and systems.
02
Organizations of all sizes and industries that want to safeguard their data, systems, and reputation from malicious cyber threats.
03
Individuals who use computers, smartphones, and other devices connected to the internet and want to prevent malware infections and privacy breaches.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I sign the top 10 malware which electronically in Chrome?
You can. With pdfFiller, you get a strong e-signature solution built right into your Chrome browser. Using our addon, you may produce a legally enforceable eSignature by typing, sketching, or photographing it. Choose your preferred method and eSign in minutes.
Can I create an electronic signature for signing my top 10 malware which in Gmail?
Create your eSignature using pdfFiller and then eSign your top 10 malware which immediately from your email with pdfFiller's Gmail add-on. To keep your signatures and signed papers, you must create an account.
How do I edit top 10 malware which on an iOS device?
Use the pdfFiller mobile app to create, edit, and share top 10 malware which from your iOS device. Install it from the Apple Store in seconds. You can benefit from a free trial and choose a subscription that suits your needs.
What is top 10 malware which?
Top 10 malware refers to the most prevalent and dangerous types of malicious software identified by cybersecurity experts, often based on their impact and frequency of attacks.
Who is required to file top 10 malware which?
Individuals or organizations that are responsible for cybersecurity and need to report malware instances for compliance or security improvement purposes are required to file information regarding the top 10 malware.
How to fill out top 10 malware which?
To fill out the report on top 10 malware, one must collect data regarding malware incidents, organize them by prevalence or impact, and provide necessary details such as type, severity, and affected systems.
What is the purpose of top 10 malware which?
The purpose is to identify the most significant threats to cybersecurity, help organizations prioritize their defenses, and provide insights for improving security protocols.
What information must be reported on top 10 malware which?
The report must include the name of the malware, type of attacks it performs, affected systems, mitigation steps taken, and any relevant statistics such as infection rates.
Fill out your top 10 malware which online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Top 10 Malware Which is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.