Get the free ISC2 Certified in Cybersecurity: Pre and Post Course ...
Show details
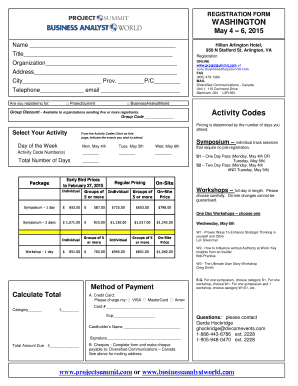
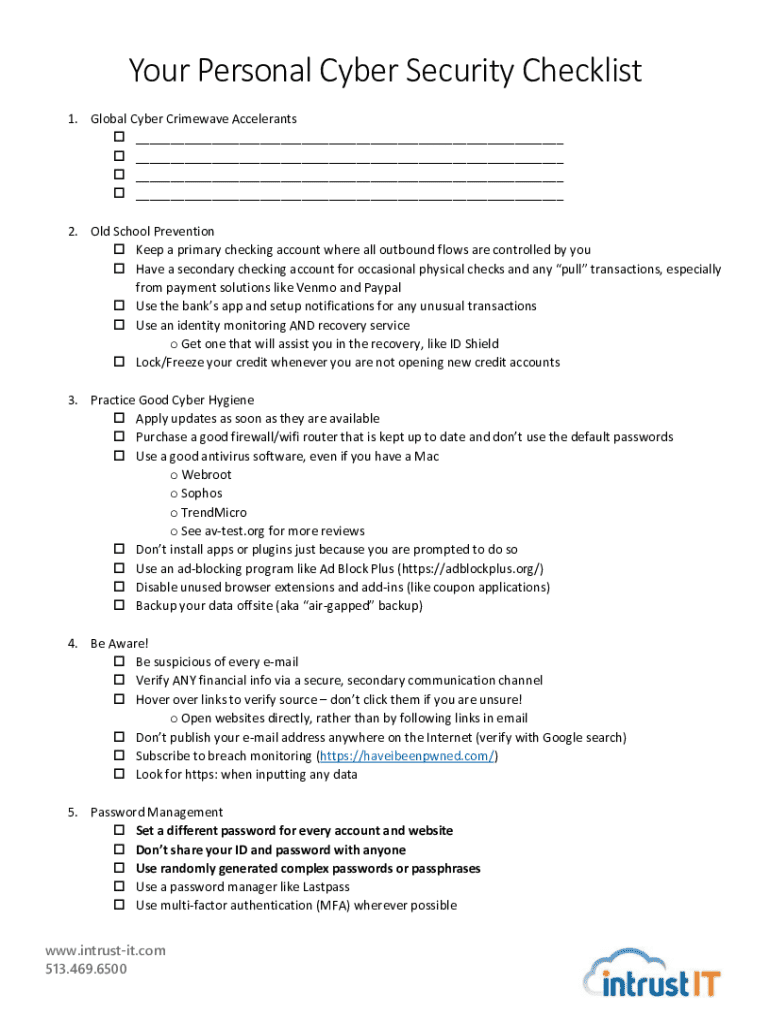
Your Personal Cybersecurity Checklist 1. Global Cyber Crime wave Accelerants ___ ___ ___ ___ 2. Old School Prevention Keep a primary checking account where all outbound flows are controlled by you
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign isc2 certified in cybersecurity

Edit your isc2 certified in cybersecurity form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your isc2 certified in cybersecurity form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit isc2 certified in cybersecurity online
Follow the guidelines below to benefit from a competent PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit isc2 certified in cybersecurity. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
It's easier to work with documents with pdfFiller than you could have believed. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out isc2 certified in cybersecurity

How to fill out isc2 certified in cybersecurity
01
Review the eligibility requirements to ensure you meet the criteria for the certification.
02
Create an account on the isc2 website and submit your application for the exam.
03
Study the exam contents and materials provided by isc2 to prepare for the exam.
04
Schedule a date and time for your exam at a certified testing center.
05
Take the exam and wait for the results to be processed.
06
If you pass the exam, complete any necessary endorsement requirements to officially earn your isc2 certified in cybersecurity.
Who needs isc2 certified in cybersecurity?
01
Cybersecurity professionals looking to further their career and demonstrate their expertise in information security.
02
Employers seeking qualified individuals to fill cybersecurity roles within their organization.
03
Individuals interested in pursuing a career in cybersecurity and looking to improve their job prospects.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I execute isc2 certified in cybersecurity online?
Easy online isc2 certified in cybersecurity completion using pdfFiller. Also, it allows you to legally eSign your form and change original PDF material. Create a free account and manage documents online.
Can I sign the isc2 certified in cybersecurity electronically in Chrome?
Yes. With pdfFiller for Chrome, you can eSign documents and utilize the PDF editor all in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a handwritten signature image. You may eSign your isc2 certified in cybersecurity in seconds.
How do I complete isc2 certified in cybersecurity on an iOS device?
Make sure you get and install the pdfFiller iOS app. Next, open the app and log in or set up an account to use all of the solution's editing tools. If you want to open your isc2 certified in cybersecurity, you can upload it from your device or cloud storage, or you can type the document's URL into the box on the right. After you fill in all of the required fields in the document and eSign it, if that is required, you can save or share it with other people.
What is isc2 certified in cybersecurity?
ISC2 Certified in Cybersecurity is a certification offered by the International Information System Security Certification Consortium (ISC2) that validates an individual's knowledge and skills in cybersecurity practices.
Who is required to file isc2 certified in cybersecurity?
Individuals seeking to demonstrate their expertise in cybersecurity and meet industry standards are typically required to pursue ISC2 certification.
How to fill out isc2 certified in cybersecurity?
To fill out the application for ISC2 certification, individuals must provide personal information, educational background, relevant work experience, and details of any prior certifications.
What is the purpose of isc2 certified in cybersecurity?
The purpose of ISC2 Certified in Cybersecurity is to ensure that professionals are knowledgeable and proficient in cybersecurity principles, enhancing their credibility and career opportunities.
What information must be reported on isc2 certified in cybersecurity?
Applicants must report personal identification details, educational qualifications, work experience, and any pertinent cybersecurity certifications.
Fill out your isc2 certified in cybersecurity online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
isc2 Certified In Cybersecurity is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.