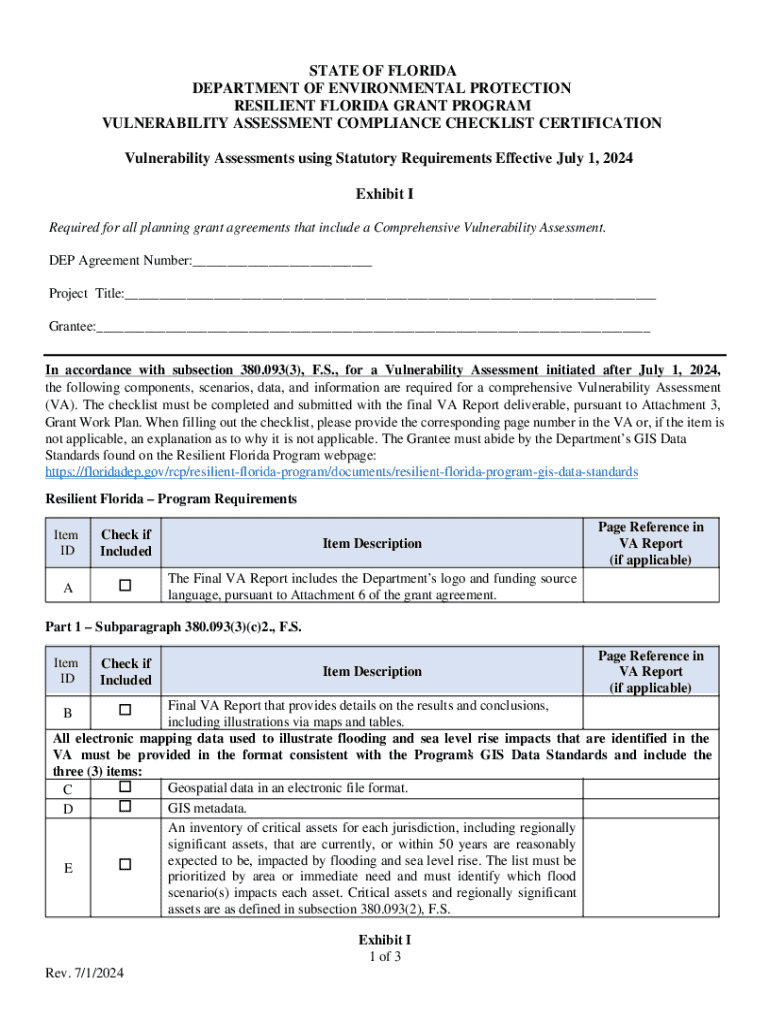
Get the free Vulnerability Assessment Compliance Checklist Certification
Show details
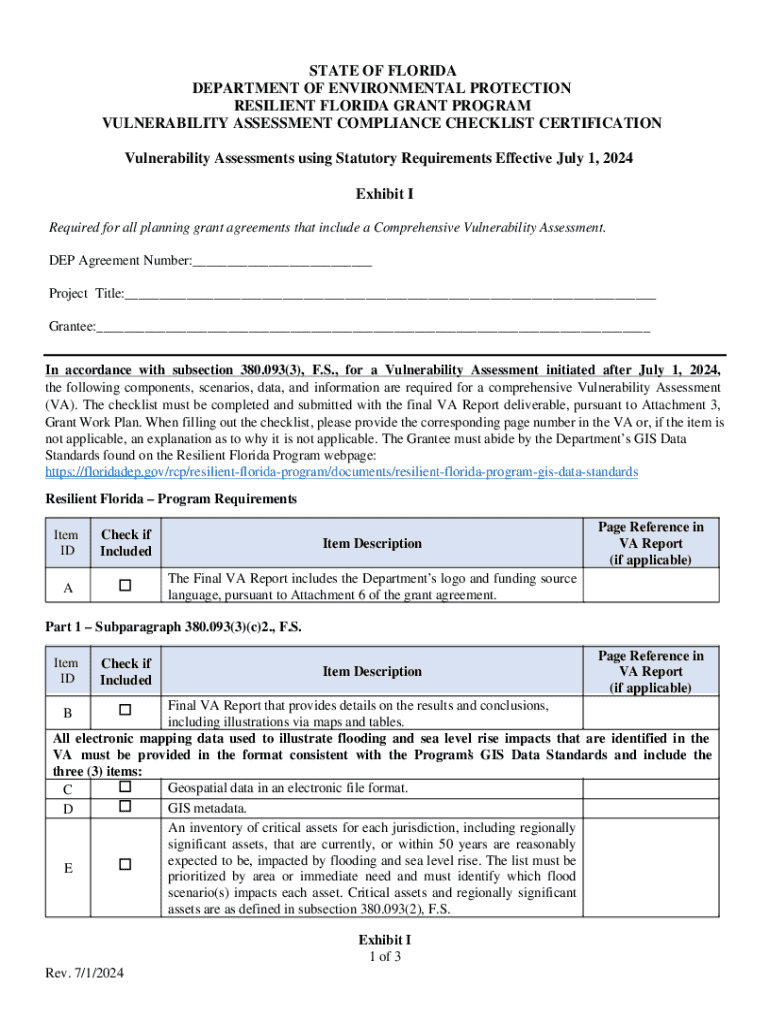
This checklist certifies compliance for comprehensive vulnerability assessments in Florida\'s Resilient Grant Program, effective July 1, 2024, ensuring thorough evaluations of flood and sea level rise impacts.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign vulnerability assessment compliance checklist

Edit your vulnerability assessment compliance checklist form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your vulnerability assessment compliance checklist form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit vulnerability assessment compliance checklist online
To use the professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit vulnerability assessment compliance checklist. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out vulnerability assessment compliance checklist

How to fill out vulnerability assessment compliance checklist
01
Start by identifying all the assets and resources within your organization that need to be assessed for vulnerabilities.
02
Determine the frequency of the vulnerability assessments based on the risk level of your organization and industry regulations.
03
Use a vulnerability assessment tool or hire a third-party provider to conduct the assessments.
04
Evaluate the scan results and prioritize the vulnerabilities based on their severity and potential impact.
05
Develop a plan to remediate the identified vulnerabilities and track the progress of the mitigation efforts.
06
Document all the findings and remediation efforts for audit purposes.
07
Repeat the vulnerability assessment process periodically to ensure ongoing compliance and security of your organization.
Who needs vulnerability assessment compliance checklist?
01
Any organization that wants to ensure the security of its assets and information systems.
02
Companies in regulated industries that are required to comply with specific security standards or regulations.
03
Organizations that handle sensitive data and want to protect it from potential cyber threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my vulnerability assessment compliance checklist in Gmail?
You can use pdfFiller’s add-on for Gmail in order to modify, fill out, and eSign your vulnerability assessment compliance checklist along with other documents right in your inbox. Find pdfFiller for Gmail in Google Workspace Marketplace. Use time you spend on handling your documents and eSignatures for more important things.
How can I modify vulnerability assessment compliance checklist without leaving Google Drive?
People who need to keep track of documents and fill out forms quickly can connect PDF Filler to their Google Docs account. This means that they can make, edit, and sign documents right from their Google Drive. Make your vulnerability assessment compliance checklist into a fillable form that you can manage and sign from any internet-connected device with this add-on.
Where do I find vulnerability assessment compliance checklist?
The pdfFiller premium subscription gives you access to a large library of fillable forms (over 25 million fillable templates) that you can download, fill out, print, and sign. In the library, you'll have no problem discovering state-specific vulnerability assessment compliance checklist and other forms. Find the template you want and tweak it with powerful editing tools.
What is vulnerability assessment compliance checklist?
A vulnerability assessment compliance checklist is a tool used to identify, assess, and report on vulnerabilities within an organization's systems, networks, and applications to ensure compliance with relevant regulations and standards.
Who is required to file vulnerability assessment compliance checklist?
Organizations that handle sensitive data or are subject to regulatory requirements, such as financial institutions, healthcare entities, and businesses that must comply with standards like PCI-DSS, are typically required to file a vulnerability assessment compliance checklist.
How to fill out vulnerability assessment compliance checklist?
To fill out a vulnerability assessment compliance checklist, organizations should first conduct a thorough vulnerability assessment, document the findings, categorize vulnerabilities based on severity, and provide corrective actions or recommended practices. This information is then organized according to the format of the checklist.
What is the purpose of vulnerability assessment compliance checklist?
The purpose of a vulnerability assessment compliance checklist is to provide a structured approach to identifying and mitigating security vulnerabilities, ensuring compliance with applicable regulations, and enhancing the overall security posture of an organization.
What information must be reported on vulnerability assessment compliance checklist?
The information that must be reported on a vulnerability assessment compliance checklist typically includes the identification of vulnerabilities, their severity ratings, remediation actions taken, timelines for addressing the vulnerabilities, and overall risk assessment outcomes.
Fill out your vulnerability assessment compliance checklist online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Vulnerability Assessment Compliance Checklist is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.