Get the free Cyberkey Rules and Regulations
Show details
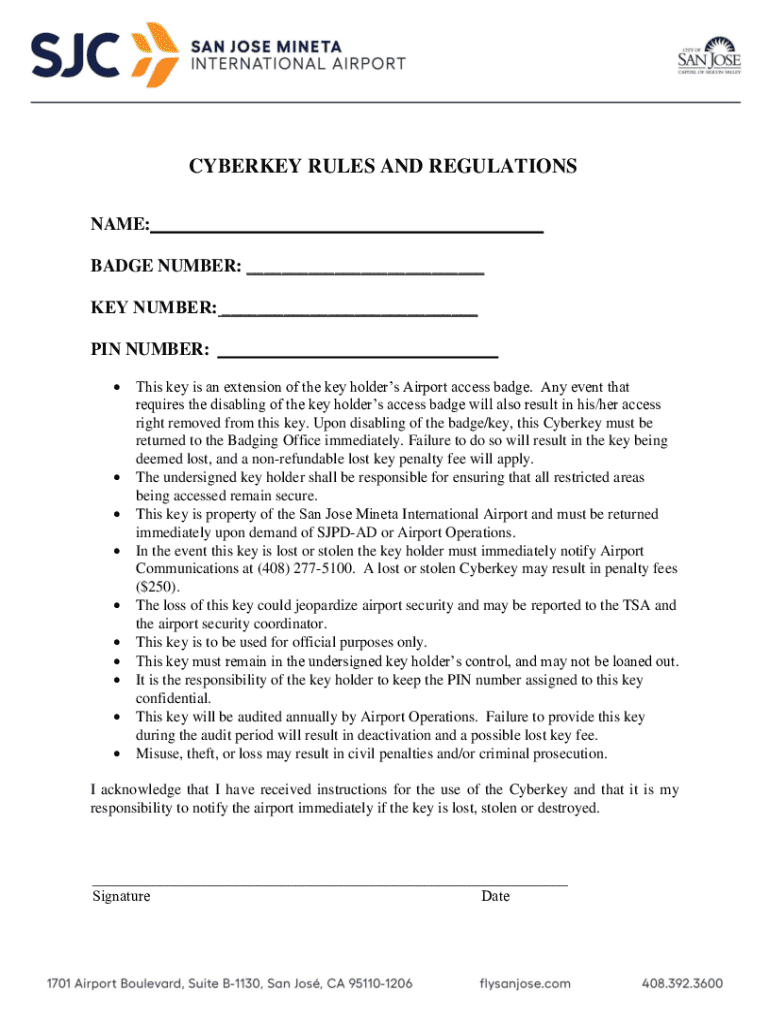
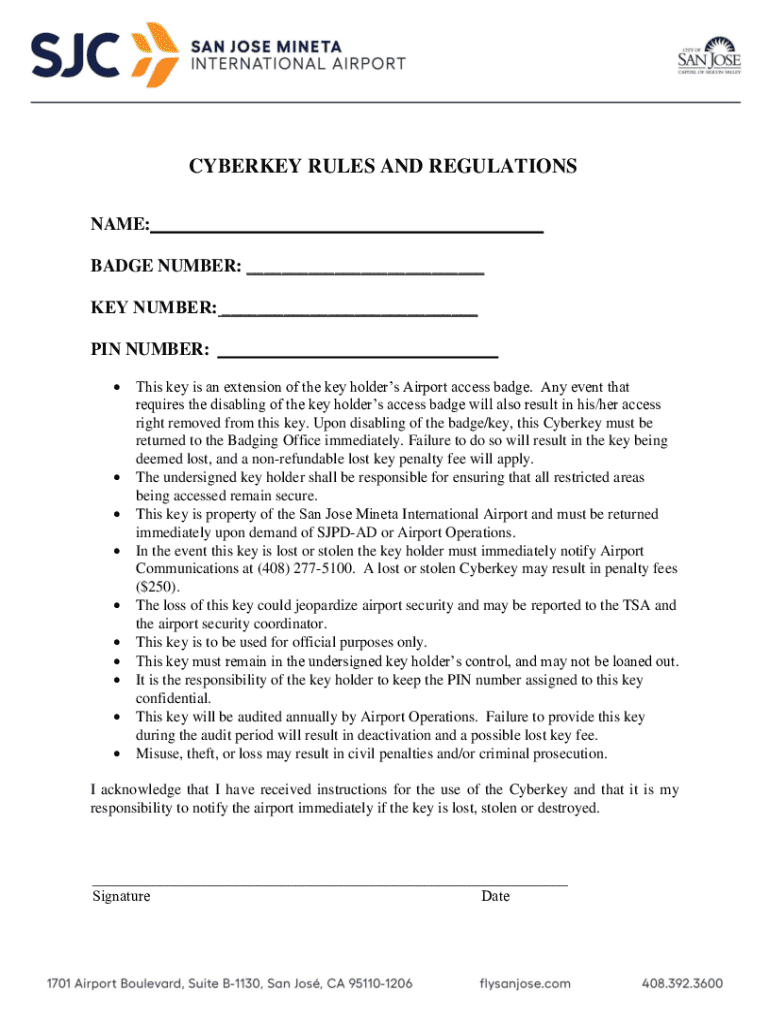
This document outlines the rules and regulations associated with the usage of the Cyberkey at the San Jose Mineta International Airport. It details the responsibilities of the key holder, the consequences of losing the key, and the protocol for reporting lost or stolen keys.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyberkey rules and regulations

Edit your cyberkey rules and regulations form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyberkey rules and regulations form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing cyberkey rules and regulations online
To use our professional PDF editor, follow these steps:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit cyberkey rules and regulations. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyberkey rules and regulations

How to fill out cyberkey rules and regulations
01
Begin by reviewing the general guidelines provided with the CyberKey.
02
Identify the specific rules and regulations that apply to your organization or situation.
03
Fill out the required fields with accurate information, ensuring compliance with all listed mandates.
04
Include any necessary signatures or approvals from designated authorities.
05
Double-check for completeness and correctness before submission.
Who needs cyberkey rules and regulations?
01
Individuals and organizations that handle sensitive information or require secure access control.
02
Staff members who manage or oversee compliance with security protocols and regulations.
03
IT departments responsible for deploying and maintaining cybersecurity measures.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make edits in cyberkey rules and regulations without leaving Chrome?
Download and install the pdfFiller Google Chrome Extension to your browser to edit, fill out, and eSign your cyberkey rules and regulations, which you can open in the editor with a single click from a Google search page. Fillable documents may be executed from any internet-connected device without leaving Chrome.
How do I fill out the cyberkey rules and regulations form on my smartphone?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign cyberkey rules and regulations and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
Can I edit cyberkey rules and regulations on an Android device?
The pdfFiller app for Android allows you to edit PDF files like cyberkey rules and regulations. Mobile document editing, signing, and sending. Install the app to ease document management anywhere.
What is cyberkey rules and regulations?
Cyberkey rules and regulations are guidelines established to ensure compliance with cybersecurity standards, protecting sensitive information and maintaining the integrity of digital communications.
Who is required to file cyberkey rules and regulations?
Entities that manage sensitive electronic data or engage in activities related to cybersecurity must file cyberkey rules and regulations to demonstrate compliance with established standards.
How to fill out cyberkey rules and regulations?
To fill out cyberkey rules and regulations, organizations must gather necessary data, complete the required forms accurately, and submit them through the prescribed channels by the deadline.
What is the purpose of cyberkey rules and regulations?
The purpose of cyberkey rules and regulations is to create a standardized framework for cybersecurity practices, safeguarding information systems against threats and ensuring legal compliance.
What information must be reported on cyberkey rules and regulations?
Reported information typically includes details about data protection measures, incident response protocols, employee training, and compliance with cybersecurity best practices.
Fill out your cyberkey rules and regulations online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyberkey Rules And Regulations is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.