Get the free About Information Security Breaches
Show details
January 9, 2023 Mark E. Smith direct dial: 713.646.1385 mesmith@bakerlaw.comVIA EMAIL (IDTHEFT@OAG.STATE.MD.US) Brian E. Frosh Attorney General Office of the Attorney General Attn: Security Breach
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign about information security breaches
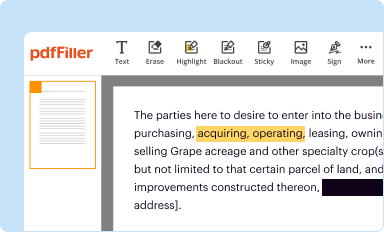
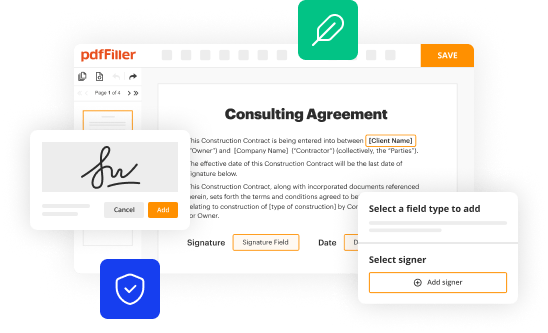
Edit your about information security breaches form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
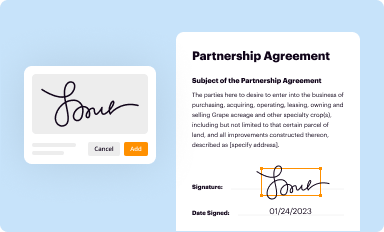
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your about information security breaches form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit about information security breaches online
Follow the steps down below to use a professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit about information security breaches. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
Dealing with documents is simple using pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out about information security breaches
How to fill out about information security breaches
01
Identify the scope of the data breach by determining what type of information was compromised.
02
Gather relevant details including the date of the breach, how it was discovered, and the systems affected.
03
Document the timeline of events from detection to response actions taken.
04
Assess the impact of the breach on affected individuals and organizations.
05
Notify affected parties, including regulators and customers, if necessary.
06
Implement corrective actions to prevent future breaches, including updating security protocols and training staff.
07
Prepare a report summarizing the breach, the response, and any future prevention measures.
Who needs about information security breaches?
01
Organizations that handle sensitive personal or financial information.
02
Businesses subject to data protection regulations like GDPR or HIPAA.
03
IT and security teams responsible for protecting organizational data.
04
Legal teams for compliance and liability issues.
05
Management and stakeholders for strategic decision-making on security measures.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find about information security breaches?
It’s easy with pdfFiller, a comprehensive online solution for professional document management. Access our extensive library of online forms (over 25M fillable forms are available) and locate the about information security breaches in a matter of seconds. Open it right away and start customizing it using advanced editing features.
How do I make edits in about information security breaches without leaving Chrome?
Install the pdfFiller Google Chrome Extension in your web browser to begin editing about information security breaches and other documents right from a Google search page. When you examine your documents in Chrome, you may make changes to them. With pdfFiller, you can create fillable documents and update existing PDFs from any internet-connected device.
Can I create an electronic signature for signing my about information security breaches in Gmail?
When you use pdfFiller's add-on for Gmail, you can add or type a signature. You can also draw a signature. pdfFiller lets you eSign your about information security breaches and other documents right from your email. In order to keep signed documents and your own signatures, you need to sign up for an account.
What is about information security breaches?
Information security breaches refer to incidents where unauthorized individuals gain access to sensitive data, potentially compromising personal, financial, or proprietary information.
Who is required to file about information security breaches?
Organizations that handle personal data or are subject to specific regulations (such as healthcare providers, financial institutions, and businesses handling consumer data) are typically required to file reports about information security breaches.
How to fill out about information security breaches?
Filing about information security breaches usually involves completing a standardized form that includes details about the breach, such as the nature of the incident, the data affected, and the measures taken in response.
What is the purpose of about information security breaches?
The purpose of filing about information security breaches is to ensure transparency, inform affected individuals, help regulatory bodies assess the breach's impact, and implement preventative measures for the future.
What information must be reported on about information security breaches?
The information that must be reported generally includes the date of the breach, the type of data involved, the number of individuals affected, the response taken, and any potential impact on the victims.
Fill out your about information security breaches online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
About Information Security Breaches is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.