Get the free Running Malicious Powershell Scripts
Show details
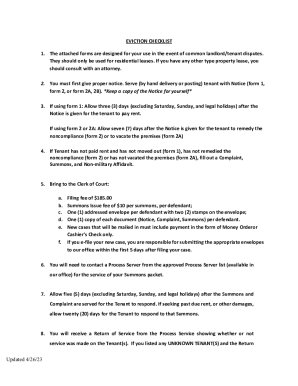
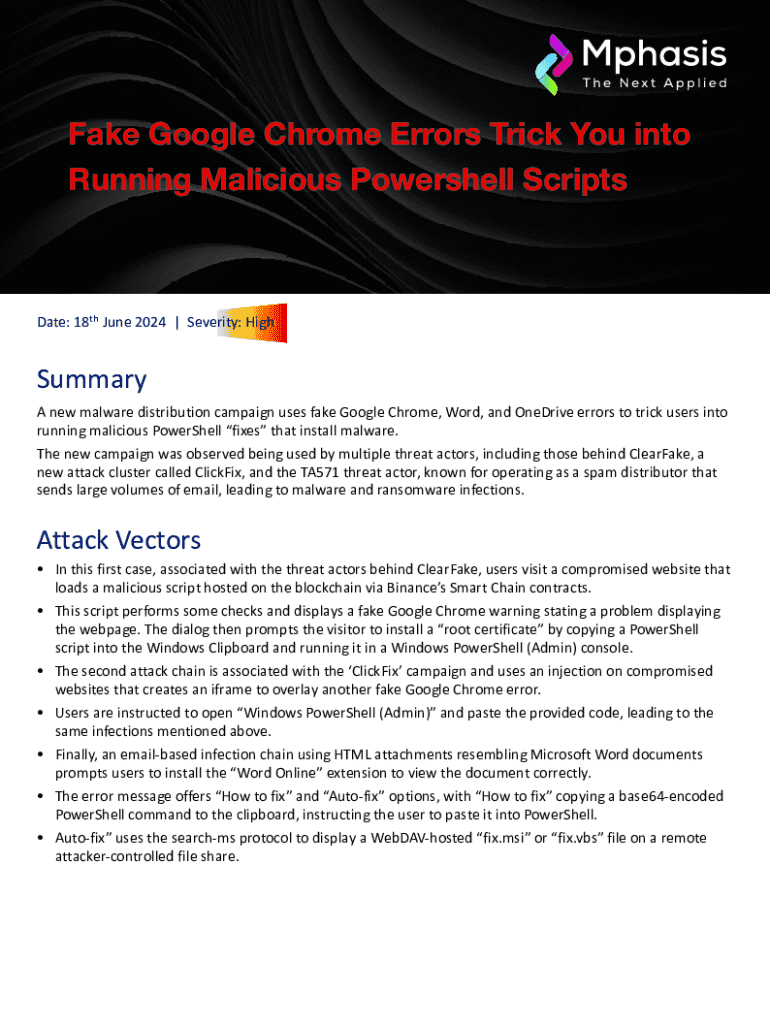
Fake Google Chrome Errors Trick You into Running Malicious Powershell ScriptsDate: 18th June 2024 | Severity: HighSummary A new malware distribution campaign uses fake Google Chrome, Word, and OneDrive
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign running malicious powershell scripts
Edit your running malicious powershell scripts form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your running malicious powershell scripts form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit running malicious powershell scripts online
Follow the steps down below to benefit from a competent PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit running malicious powershell scripts. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out running malicious powershell scripts
How to fill out running malicious powershell scripts
01
Open PowerShell with administrative privileges.
02
Ensure that script execution is set to 'Unrestricted' by running 'Set-ExecutionPolicy Unrestricted'.
03
Download or create the malicious PowerShell script file.
04
Use 'cd' command to navigate to the directory where the script is located.
05
Execute the script by typing './scriptname.ps1' and pressing Enter.
06
Monitor system behavior for changes that indicate malicious activity.
Who needs running malicious powershell scripts?
01
Cybercriminals seeking to exploit vulnerabilities.
02
Hackers aiming to gain unauthorized access to systems.
03
Individuals wanting to perform unethical activities for personal gain.
04
Groups aiming to disrupt or damage systems for ideological reasons.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit running malicious powershell scripts from Google Drive?
Simplify your document workflows and create fillable forms right in Google Drive by integrating pdfFiller with Google Docs. The integration will allow you to create, modify, and eSign documents, including running malicious powershell scripts, without leaving Google Drive. Add pdfFiller’s functionalities to Google Drive and manage your paperwork more efficiently on any internet-connected device.
How do I edit running malicious powershell scripts straight from my smartphone?
The best way to make changes to documents on a mobile device is to use pdfFiller's apps for iOS and Android. You may get them from the Apple Store and Google Play. Learn more about the apps here. To start editing running malicious powershell scripts, you need to install and log in to the app.
How do I edit running malicious powershell scripts on an iOS device?
You can. Using the pdfFiller iOS app, you can edit, distribute, and sign running malicious powershell scripts. Install it in seconds at the Apple Store. The app is free, but you must register to buy a subscription or start a free trial.
What is running malicious powershell scripts?
Running malicious PowerShell scripts refers to the execution of scripts written in the PowerShell programming language that are designed to perform harmful actions on a computer system, such as stealing data, installing malware, or compromising security.
Who is required to file running malicious powershell scripts?
Typically, IT security professionals, network administrators, or cybersecurity incident response teams are required to document instances of running malicious PowerShell scripts as part of their security monitoring and incident reporting processes.
How to fill out running malicious powershell scripts?
To document running malicious PowerShell scripts, one should record the script's source, date and time of execution, affected systems, observable impacts, and any actions taken to mitigate the threat, often using an incident report template or security incident form.
What is the purpose of running malicious powershell scripts?
The purpose of running malicious PowerShell scripts is often to exploit vulnerabilities, gain unauthorized access, spread malware, exfiltrate sensitive information, or disrupt services within a target organization.
What information must be reported on running malicious powershell scripts?
Information that must be reported includes the script's origin, execution time, systems affected, actions taken by the script, indicators of compromise, and any steps taken to remediate the issue.
Fill out your running malicious powershell scripts online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Running Malicious Powershell Scripts is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.