Get the free Voting System Security Program/plan
Get, Create, Make and Sign voting system security programplan
How to edit voting system security programplan online
Uncompromising security for your PDF editing and eSignature needs
How to fill out voting system security programplan
How to fill out voting system security programplan
Who needs voting system security programplan?
Voting System Security Program Plan Form: A Comprehensive Guide
Understanding the voting system security program
Voting system security is crucial for safeguarding the integrity of democratic processes. As election systems become increasingly digitized, threats from cyber attacks, unauthorized access, and insider fraud have escalated. Protecting the sanctity of votes and voter information must be a top priority for election officials. There are various aspects of cybersecurity that play a role in securing elections, from creating secure voting machines to developing stringent data protection measures.
Planning your voting system security program
The first step in creating a voting system security program is defining your security objectives. These objectives should detail what you aim to achieve, such as minimizing vulnerabilities, ensuring compliance with local regulations, and enhancing voter confidence. Clearly defined goals that can be measured will facilitate the evaluation of the program’s success.
Assembling a security committee is crucial for the effective implementation of your program. This committee should comprise individuals from diverse backgrounds, such as cybersecurity experts, legal advisors, and election officials. Each member should have specified roles, contributing their expertise to form a holistic approach to security. The diversity in skill sets allows for more thorough risk assessments and problem-solving.
Developing a comprehensive security strategy
Once you've planned your program, the next step is to assess your current security measures thoroughly. Conducting a security audit will help identify existing vulnerabilities and potential gaps in your system. This audit should evaluate your technology infrastructure, personnel training, and previous incident responses.
After assessing your current stance, the next task is crafting a tailored security policy. This policy should include essential elements like access control measures, incident reporting procedures, and data encryption standards. Additionally, it’s crucial to adapt your policies according to specific state regulations to ensure compliance and legitimacy.
Implementing security measures
Implementing security measures involves both hardware and software components. Selecting secure voting machines with tamper-evident features is paramount. Moreover, these machines should have updated software with regular patches to safeguard against emerging vulnerabilities. A robust software environment not only improves security but also enhances the user experience.
Another critical component is personnel training and awareness. Developing training programs for poll workers and officials ensures they are familiar with security procedures and potential threats. Additionally, educating voters about security practices and what to look for can help enhance overall security during elections.
Ensuring compliance and regulatory adherence
Understanding the legal landscape is crucial when developing your voting system security program. There are various federal and state regulations that govern election security, including standards set by the National Institute of Standards and Technology (NIST) and the International Organization for Standardization (ISO). Being aware of these compliance standards guarantees that your security program meets necessary legal requirements.
Documenting compliance procedures is an integral part of maintaining transparency. Thorough records of all security measures should be kept, which may include audit results, training programs, and policy updates. Many jurisdictions also require specific reporting to state authorities, so being proactive in documentation will streamline this process.
Incident response and management
Despite the best security measures, breaches may still occur. Therefore, preparing for security incidents is a vital part of your security plan. Developing an incident response plan that outlines immediate action steps is essential. This plan should include communication protocols, roles during a breach, and data recovery strategies.
After an incident occurs, effective communication with stakeholders is key. Maintaining transparency can help preserve public trust during a crisis. It’s vital to inform the electorate about what actions you’ve taken, the status of the breach, and how it will impact the election process.
Engaging stakeholders and the community
Building partnerships with technology companies and security experts can significantly enhance your security program. Collaborating with local law enforcement ensures that your security plans align with emergency response strategies. This collaboration can often lead to better preparedness and response during election events.
Engaging voters is also essential; strategies for informing the public about security measures should be prioritized. Gaining voter trust not only enhances public confidence in the electoral process but also ensures a higher turnout during elections. Strategies can include community meetings, information pamphlets, and social media updates.
Utilizing technology and innovations
Emerging technologies hold tremendous potential for voting security. For instance, blockchain technology can provide tamper-proof records of votes, ensuring transparency and trust. Leveraging machine learning algorithms in threat detection can enhance the ability to identify unusual activities, further safeguarding the voting process.
When implementing secure electronic voting systems, best practices should be a cornerstone of your strategy. This includes regular updates, using encryption for ballots, and vigilant monitoring for suspicious activities. Recognizing what to consider when choosing electronic voting systems will help in fortifying the security of the voting process.
Monitoring and future improvements
Continuous monitoring is essential to maintain the environment for secure voting. Implementing real-time monitoring solutions allows for immediate threat detection and quick reaction capabilities. Tools that provide ongoing threat assessments should be utilized for a proactive approach to security.
Moreover, your security program must remain adaptable. As technology and threats evolve, so should your security measures. Regular reviews, updates to policies, and enhanced training programs help ensure that your voting system security program remains relevant and effective.
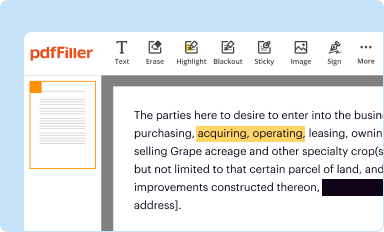
Integrating pdfFiller for document management
pdfFiller is an invaluable tool for managing the various forms and documents crucial to your voting system security program. By using pdfFiller, election officials can create secure, shareable forms that meet compliance standards with ease. This streamlining of form management aids in ensuring accountability and transparency.
The collaboration features of pdfFiller allow teams to work together seamlessly, enhancing the document review processes through cloud-based access. This functionality enables efficient management of document versions and approvals, crucial for maintaining up-to-date policies, training materials, and compliance documentation.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send voting system security programplan to be eSigned by others?
How do I execute voting system security programplan online?
How do I fill out the voting system security programplan form on my smartphone?
What is voting system security programplan?
Who is required to file voting system security programplan?
How to fill out voting system security programplan?
What is the purpose of voting system security programplan?
What information must be reported on voting system security programplan?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.