Get the free M.s. in Cybersecurity Program Planning Guide
Get, Create, Make and Sign ms in cybersecurity program



Editing ms in cybersecurity program online
Uncompromising security for your PDF editing and eSignature needs
How to fill out ms in cybersecurity program

How to fill out ms in cybersecurity program
Who needs ms in cybersecurity program?
Master of Science in Cybersecurity Program Form: Your Comprehensive Guide
Overview of the Master of Science in Cybersecurity Program
The Master of Science in Cybersecurity program is tailored for individuals aspiring to gain advanced knowledge and skills in a field that is critically important in today's technologically driven environment. With cyber threats evolving rapidly, obtaining an MS in Cybersecurity equips students with essential strategies to protect sensitive information and maintain the integrity of systems. The program focuses on developing expertise in identifying vulnerabilities, implementing security measures, and responding to cyber incidents.
Core program objectives include preparing students to effectively manage cybersecurity challenges, understand the legal and ethical implications of cybersecurity practices, and foster a proactive approach to security management. Given the increasing sophistication of cyber attacks, this education is more than just beneficial; it has become essential for businesses, governments, and organizations worldwide to secure their digital assets.
Key features of the MS in Cybersecurity Program
One of the distinguishing features of the MS in Cybersecurity program is its STEM designation. This classification is significant as it highlights the program's focus on science, technology, engineering, and mathematics, providing additional benefits for graduates.
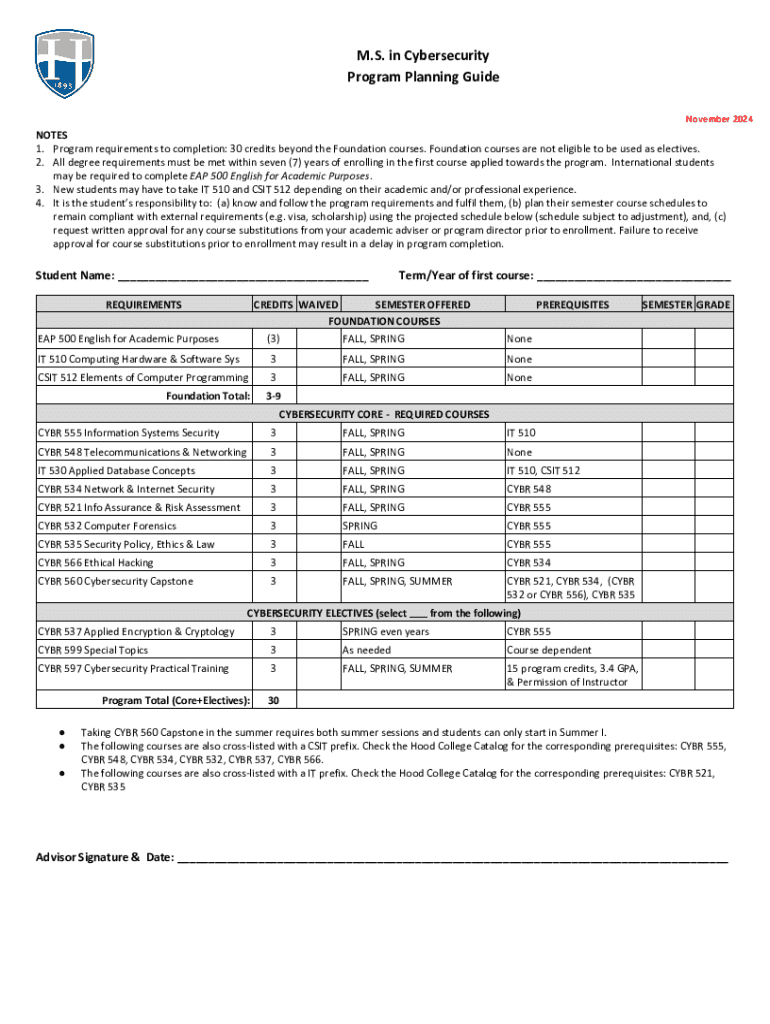
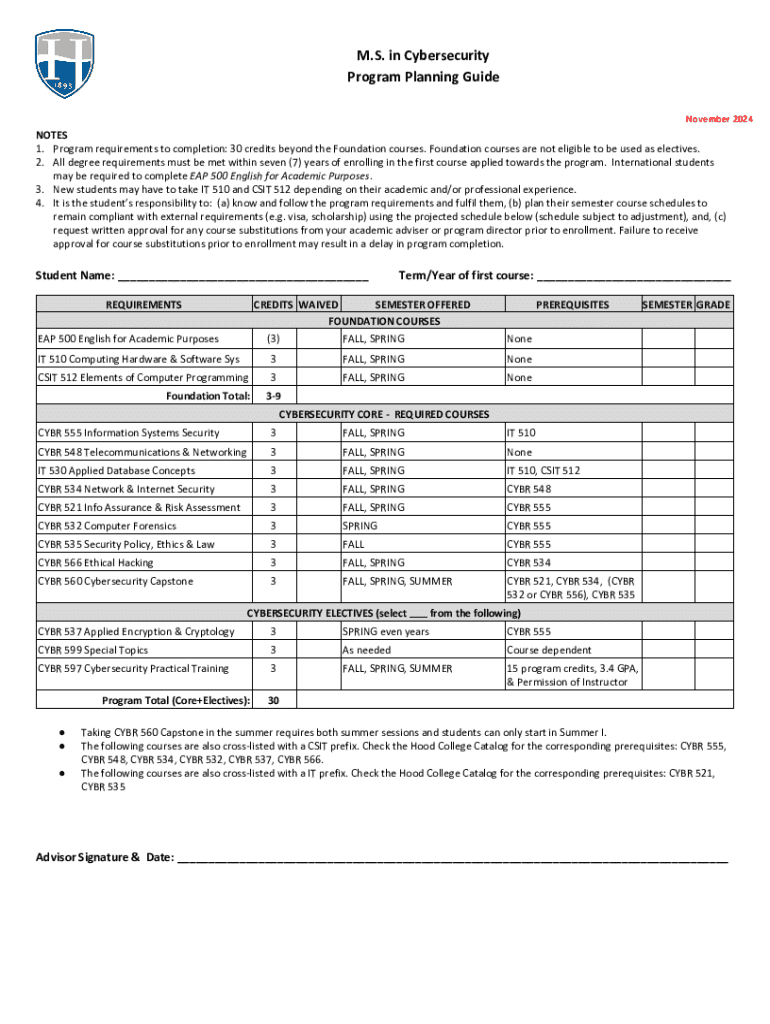
Program structure and curriculum requirements
The MS in Cybersecurity program typically spans 1-2 years, depending on whether students choose a full-time or part-time track. Students are usually required to complete around 30-36 credit hours to earn their degree. Core courses often cover critical areas such as network security, risk management, cryptography, and ethical hacking.
Additionally, students have the option to select electives that align with their career interests. Specializations may delve into innovative sections such as cloud security, application security, and data protection laws, ensuring that graduates are well-versed in current trends and technological advancements in cybersecurity.
Admissions process for the MS in Cybersecurity
To apply for the MS in Cybersecurity, candidates must first meet specific eligibility criteria, including having a bachelor's degree in a relevant field such as computer science, information technology, or a related discipline. Prospective students are expected to possess a foundational understanding of programming, networking, and security principles, as these will be critical in advanced studies.
Financial considerations for prospective students
Understanding the financial commitments associated with the MS in Cybersecurity is essential for prospective students. Tuition fees vary widely by institution but generally range from $20,000 to $60,000 for the entire program. Additional costs may include expenses related to books, materials, and technology fees.
Career opportunities after graduation
The demand for cybersecurity professionals is surging, with the Bureau of Labor Statistics projecting a growth rate of 31% from 2019 to 2029. Graduates of the MS in Cybersecurity can expect to find numerous career opportunities in various sectors, including finance, healthcare, government, and technology.
Graduate outcomes and success stories
Alumni of the MS in Cybersecurity program often embark on successful career paths, with many attaining influential positions in the field. Notable alumni have contributed significantly to advancements in cybersecurity practices, formulated strategies at Fortune 500 companies, and established their startups focused on innovative security solutions.
Interactive tools and resources for application
Applying for the MS in Cybersecurity program can be streamlined through the use of document management solutions like pdfFiller. This platform simplifies the process of filling out the MS in Cybersecurity program form, allowing applicants to edit, sign, and manage their documents with ease.
Using pdfFiller, students can create and share application materials efficiently, alleviating some of the stress involved in documentation. The advantages of having a centralized location for form management cannot be overstated, enhancing the applicant experience.
Preparing your application with pdfFiller
Navigating the application process becomes simpler when utilizing pdfFiller. To effectively prepare and submit your application materials, start by creating an account on the platform. Next, access the MS in Cybersecurity program form, fill in the required fields, and utilize the editing tools available for a polished finish.
Engagement and community building
Getting involved in the cybersecurity community within the institution can enrich the educational experience. Prospective students often have opportunities to connect with faculty members and current students through informational sessions, webinars, and networking events.
Frequently asked questions
Potential applicants often have several questions regarding the MS in Cybersecurity program. Common inquiries include concerns about specific admission criteria, the structure of the curriculum, and what resources are available for student support.
Insights from cybersecurity experts
The cybersecurity field is ever-evolving, and insights from faculty and industry leaders can provide valuable perspectives. Guest articles and interviews often highlight emerging trends, technological advancements, and tips for navigating the job market effectively.
Next steps for potential applicants
For individuals considering an application to the MS in Cybersecurity, it is critical to develop a clear plan. Preparation may include gathering application materials, reaching out for letters of recommendation, and finalizing personal statements.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit ms in cybersecurity program from Google Drive?
How do I make edits in ms in cybersecurity program without leaving Chrome?
How do I fill out ms in cybersecurity program using my mobile device?
What is ms in cybersecurity program?
Who is required to file ms in cybersecurity program?
How to fill out ms in cybersecurity program?
What is the purpose of ms in cybersecurity program?
What information must be reported on ms in cybersecurity program?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.