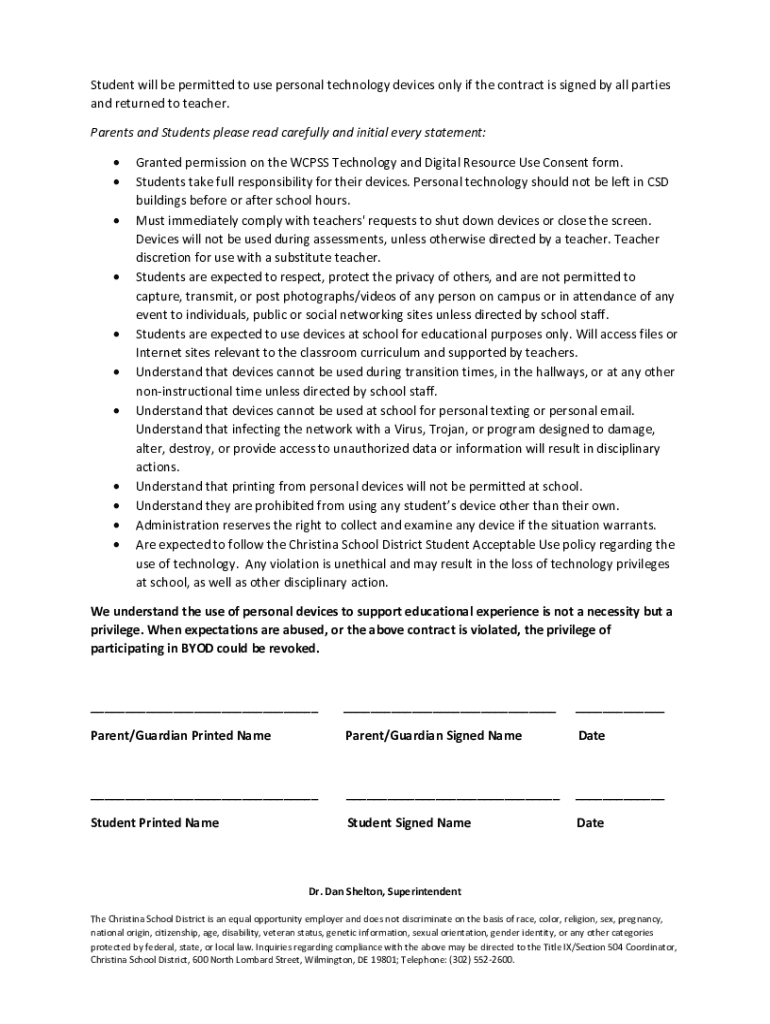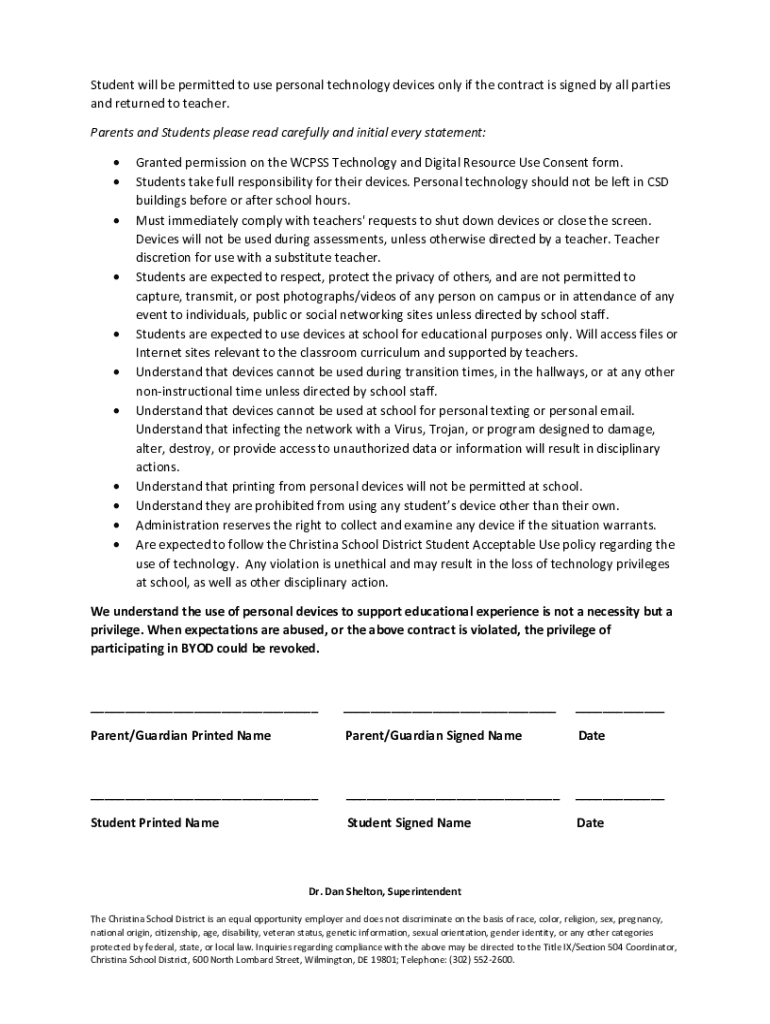
Get the free Byod Explanation and Terms of Agreement
Get, Create, Make and Sign byod explanation and terms
How to edit byod explanation and terms online
Uncompromising security for your PDF editing and eSignature needs
How to fill out byod explanation and terms
How to fill out byod explanation and terms
Who needs byod explanation and terms?
BYOD Explained: Policies and Terms Form for Modern Workplaces
Understanding BYOD: An overview
BYOD, or Bring Your Own Device, refers to a policy that allows employees to use their personal devices—such as smartphones, tablets, and laptops—to access company resources and systems. This trend has emerged in response to the growing reliance on technology for work, and it has significantly evolved from a simple convenience to a strategic approach in modern workplaces. The catalyst for this transformation includes increasing employee demand for flexibility, advancements in mobile technology, and a shift toward remote and hybrid work settings.
Key terms related to BYOD include Mobile Device Management (MDM), which refers to software solutions that help organizations manage and secure employee devices. Other essential phrases include ‘acceptable use policies’, which outline how personal devices should be used in a work environment, and ‘data security’, highlighting the importance of protecting sensitive information accessed via personal devices.
The importance of BYOD policies
Organizations implement BYOD policies for several compelling reasons. Firstly, it enhances employee satisfaction and productivity by providing the flexibility to work from preferred devices. Studies show that employees often perform better on devices they are familiar with, leading to increased efficiency and engagement. Additionally, BYOD can generate significant cost savings for organizations, as it reduces the burden of providing hardware and maintenance support.
However, while the benefits are notable, BYOD comes with inherent risks. Data security vulnerabilities are a primary concern, particularly when personal devices access sensitive company data. Moreover, compliance issues and legal considerations may arise, especially in regulated industries where data protection is paramount. Thus, it is critical for organizations to have comprehensive BYOD policies in place to mitigate these risks.
Essential components of a BYOD policy
A well-defined BYOD policy should include several essential components to address potential challenges effectively. First, it should provide clear definitions of device eligibility to ensure that employees know which devices can be used for work. Additionally, the policy must distinguish between personal and corporate data, ensuring employees understand what information can be accessed and stored on personal devices.
Security protocols are also critical, incorporating the following guidelines:
Lastly, the policy must outline the responsibilities of both employees and the IT department to ensure secure and responsible BYOD usage.
Creating a BYOD agreement
Developing a BYOD agreement is crucial for establishing a clear framework of expectations between the organization and its employees. The agreement should include key elements like the purpose of BYOD and its scope, acceptable use policies that outline how devices should be utilized for work, and delineation of user responsibilities and liabilities in case of a data breach or device theft.
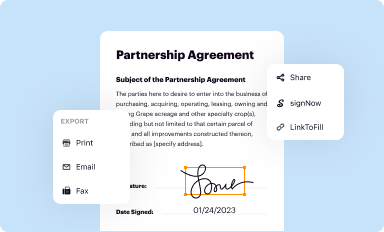
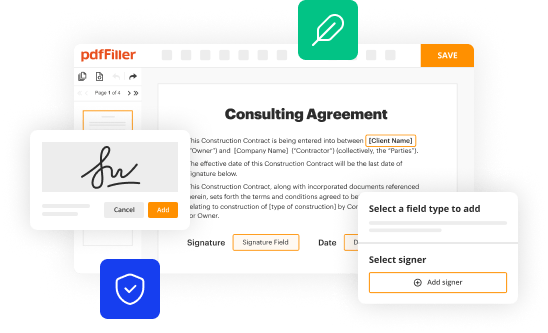
When drafting a comprehensive BYOD agreement, organizations should consider leveraging interactive tools like pdfFiller. These tools can provide templates that streamline the creation process, ensuring all necessary components are included and tailored to specific organizational needs.
Best practices for implementing BYOD
For successful BYOD implementation, organizations should follow a series of best practices. First, assessing organizational readiness will help identify potential challenges and ensure that the necessary infrastructure and support are in place.
Engaging stakeholders during policy creation is equally important. Involving employees in discussions around the policy can lead to greater acceptance and adherence.
Training employees on BYOD usage and security best practices is essential to create a culture of awareness and responsibility regarding data protection. Additionally, regular review and updates of BYOD policies will help organizations adapt to changing technology and emerging threats.
Tools and resources for BYOD management
Several tools can aid in managing BYOD environments effectively. Mobile Device Management (MDM) software provides organizations with a centralized platform to manage employee devices, enforce security protocols, and administer updates. Features may include tracking device compliance, pushing necessary applications, and securing data.
In addition, utilizing pdfFiller for document management and policy dissemination is beneficial. This platform enables teams to collect, edit, and manage BYOD agreements efficiently. Interactive forms can be used for tracking device compliance and maintaining employee agreements to enhance organization-wide BYOD management.
Frequently asked questions about BYOD
Common misconceptions about BYOD often revolve around perceived risks versus actual benefits. Many believe that allowing personal devices increases security vulnerabilities. However, with robust policies and security measures in place, organizations can leverage BYOD safely.
Privacy concerns are also frequently raised. Employees want assurances that their personal information is not monitored. It is critical for organizations to communicate the boundaries of monitoring and data access clearly.
Lastly, it is important to clarify the differences between BYOD policies and corporate-owned device strategies. Each approach comes with unique implications regarding security, ownership of data, and user responsibilities.
Further exploration of BYOD related topics
As BYOD continues to evolve, several related topics deserve exploration. Mobile App Security Guidelines are crucial for ensuring that employee applications accessing company data comply with security standards. Organizations should also stay informed about emerging trends in BYOD practices, such as the integration of biometric authentication and the increasing relevance of wearable technology.
Furthermore, conversations around personal computers in BYOD policies are gaining traction, as more employees seek to connect laptops for workplace productivity. Addressing these topics will ensure that organizations remain proactive in adapting to the changing technological landscape.
Key takeaways for a successful BYOD implementation
Implementing BYOD policies effectively requires understanding key components and fostering a secure environment. Organizations must prioritize regular updates and training to ensure employees are equipped to handle potential risks associated with personal device use.
Engaging employees in the BYOD process is vital for building a culture of responsibility and security. With strong policies in place and ongoing dialogue about best practices, organizations can harness the advantages of BYOD while minimizing risks.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I execute byod explanation and terms online?
Can I create an eSignature for the byod explanation and terms in Gmail?
How do I fill out byod explanation and terms using my mobile device?
What is BYOD explanation and terms?
Who is required to file BYOD explanation and terms?
How to fill out BYOD explanation and terms?
What is the purpose of BYOD explanation and terms?
What information must be reported on BYOD explanation and terms?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.