Last updated on Mar 26, 2026
Pentest Agreement Template free printable template
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
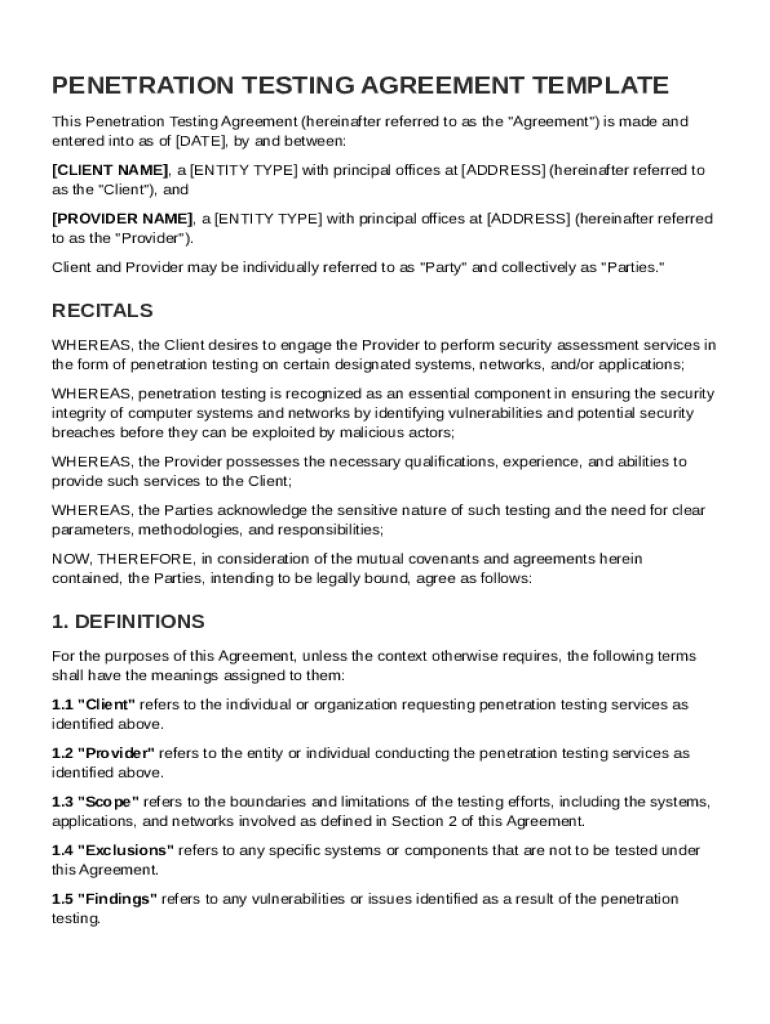
What is Pentest Agreement Template
The Penetration Testing Agreement Template is a legal document used by clients and providers to outline the terms of security assessment services, specifically focusing on penetration testing.
pdfFiller scores top ratings on review platforms




So far everything seems to be alright.. I like it
For a non-tech-savvy person, this is terrific!
Some colleges that I sent my transcripts using PDF filler could not open them
Easy to use but provides to assistance to follow IRS instructions or form guidance.
easy to use, saves a lot of time. clean and clear type fonts.
PDFfiller has helped tremendously in our homeschooling.
Who needs Pentest Agreement Template?
Explore how professionals across industries use pdfFiller.
Comprehensive Pentest Agreement Template on pdfFiller
A Pentest Agreement Template form is essential for establishing clear terms between the client and penetration testing service provider. This document outlines the scope, responsibilities, and legal considerations necessary for effective cybersecurity engagements.
What is penetration testing and why is it important?
Penetration testing, commonly referred to as pen testing, is a simulated cyber attack against your system to check for vulnerabilities that an attacker could exploit. The importance of penetration testing lies in its ability to identify weaknesses before they can be exploited by malicious actors.
-
Penetration testing is an authorized simulated attack conducted on a computer system to evaluate its security.
-
Regular testing helps in identifying vulnerabilities proactively, ensuring compliance with security standards, and protecting sensitive data.
-
By uncovering vulnerabilities, it enables organizations to fortify their defenses, reducing the overall risk of cyber threats.
What are the key components of a penetration testing agreement?
A well-structured penetration testing agreement includes essential components that clarify the engagement. These components are vital for setting expectations and protecting both the client and the service provider.
-
The agreement should clearly identify all parties involved to establish responsibilities and liabilities.
-
Recitals provide context and outline what the penetration test seeks to achieve, ensuring alignment between the client and provider.
-
It’s important to define specific cybersecurity terms to avoid misinterpretation and ensure clarity throughout the document.
How do you craft your pentest agreement?
Crafting a penetration testing agreement involves structured sections to ensure thoroughness and clarity. Each section addresses distinct aspects of the engagement.
-
Clearly list contact and corporate details of both parties to facilitate smooth communication.
-
Detail the exact testing boundaries, including systems and processes that will be assessed.
-
Outline any areas that are off-limits to clarify expectations and prevent misunderstandings.
-
Specify the methodologies that will be used, such as Black Box or White Box testing, and assign responsibilities to both teams.
-
Include clauses that ensure both parties maintain confidentiality and handle data securely.
What are the different types of penetration testing engagements?
Understanding the types of penetration testing can help organizations choose the correct method for their needs. Each type has distinct characteristics that suit various scenarios.
-
The tester has no internal knowledge of the system, simulating an external attacker's approach.
-
The tester has complete knowledge of the infrastructure, which helps in executing thorough testing.
-
The tester has some knowledge of the system configuration, balancing between the Black and White Box strategies.
-
Organizations should assess their security objectives and existing vulnerabilities to select the most suitable testing type.
Why is documenting findings and reporting essential?
Documenting findings from penetration tests is crucial for ensuring that all vulnerabilities are addressed properly. A well-structured report not only communicates issues but also guides remediation efforts.
-
Detailed findings help stakeholders understand vulnerabilities' severity and the potential risks associated with them.
-
Using standard formats helps ensure consistency and clarity in presenting results.
-
Adopt a clear, structured approach when presenting to stakeholders, focusing on actionable insights and prioritizing critical vulnerabilities.
What related contract templates and resources are available?
Various cybersecurity contract templates complement the Pentest Agreement Template. Utilizing these resources can streamline the contracting process.
-
This template provides guidelines on how an organization should conduct penetration tests and manage related policies.
-
Various templates are available for different cybersecurity services, encouraging comprehensive security practices.
-
Leverage these tools to ensure compliance with industry standards while enhancing cybersecurity capabilities.
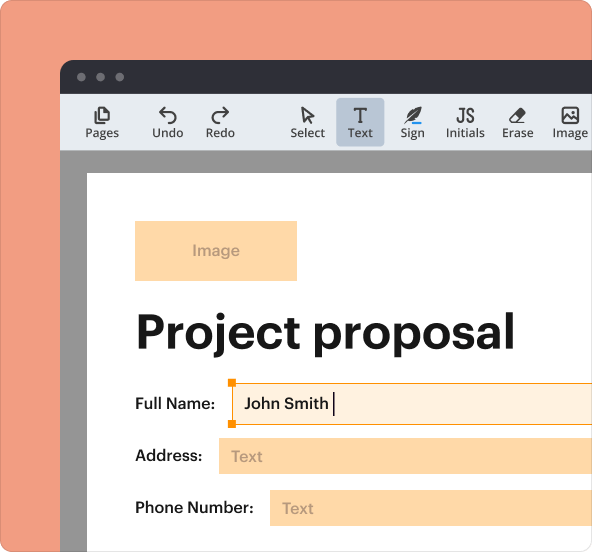
How to utilize pdfFiller for seamless agreement management?
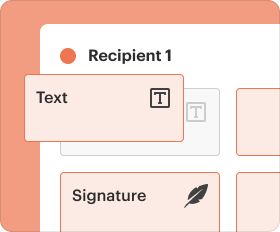
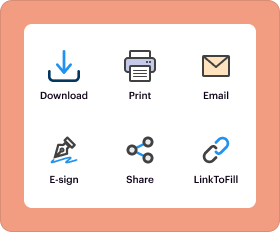
pdfFiller offers a user-friendly platform for managing your Pentest Agreement Template. From editing to e-signing, pdfFiller simplifies the entire document workflow.
-
Easily modify the template using the intuitive drag-and-drop interface, ensuring your agreement meets specific needs.
-
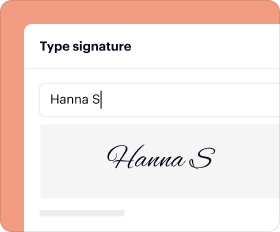
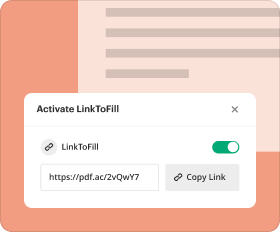
Leverage the platform’s eSignature feature for quick approvals and share the document with stakeholders securely.
-
Manage all your documents in one place, with access from anywhere, ensuring efficiency and collaboration.
What are the legal and compliance considerations in penetration testing?
Legal and compliance considerations are vital in penetration testing contracts to avoid potential legal pitfalls. Understanding regional regulations can significantly impact the testing process.
-
Various regions impose unique regulatory requirements on cybersecurity, which must be included in the agreement.
-
Different industries may have specific regulations that influence how penetration tests are conducted and reported.
-
Follow legal guidelines and consult with legal experts to ensure all aspects of the penetration testing process comply with applicable laws.
How to fill out the Pentest Agreement Template
-
1.Access the Penetration Testing Agreement Template on pdfFiller by searching for it or navigating to the appropriate category in the tool.
-
2.Open the form, and use the editing tools to fill in the provided fields, including your client and provider information.
-
3.Before starting, gather necessary details such as the systems to be tested, any exclusions, and relevant dates for the agreement.
-
4.Navigate through the blank fields and utilize checkboxes to indicate agreements and stipulations as instructed.
-
5.Review the filled-out document for any missing information to ensure completeness.
-
6.Once all fields are accurately completed, finalize the document by checking for accuracy and ensuring all required signatures are indicated.
-
7.Save your work by clicking on the save option in pdfFiller, and you can choose to download the completed agreement or submit it directly through pdfFiller's submission features.
Who is eligible to use this Penetration Testing Agreement Template?
The Penetration Testing Agreement Template is intended for clients needing penetration testing services and providers offering these services. Both parties should have the authority to enter into a binding contract.
What information do I need before filling out this form?
Before filling out the form, gather details such as client and provider names, addresses, system specifics for testing, exclusions, and start and end dates for the agreement.
How do I submit the completed agreement?
After completing the Penetration Testing Agreement, you can submit it directly through pdfFiller's platform, or you can download it for manual submission via email or postal mail.
Are there any common mistakes to avoid when completing this form?
Common mistakes include leaving fields blank, failing to include specific system details, or not having both parties' signatures. Ensure all sections are filled accurately and reviewed.
What is the processing time for this agreement once submitted?
While the Penetration Testing Agreement itself does not have a formal processing time, both parties should review and sign promptly to ensure the timeline for penetration testing can be adhered to.
Is notarization required for this agreement?
No, notarization is not required for the Penetration Testing Agreement Template. However, having it notarized may enhance its legal validity in some cases.
What should I do if I need to make changes after submitting the form?
If changes are needed after submission, communicate with the other party to go over modifications and then amend the form on pdfFiller, ensuring new versions are signed by both parties.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.