Get the free Techie held for hacking into payment gateway in Hyderabad
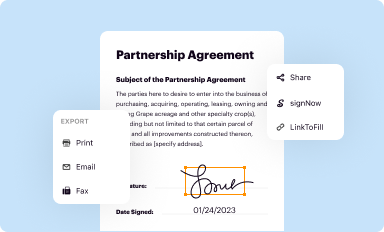
Get, Create, Make and Sign techie held for hacking
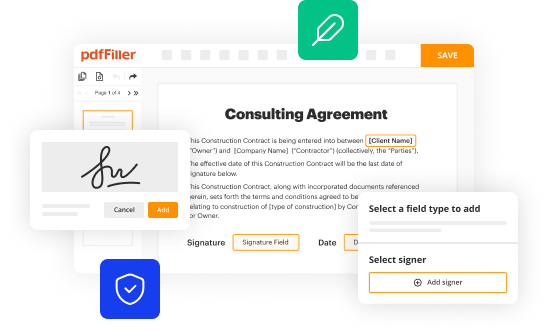
Editing techie held for hacking online
Uncompromising security for your PDF editing and eSignature needs
How to fill out techie held for hacking
How to fill out techie held for hacking
Who needs techie held for hacking?
Techie held for hacking form
Understanding the legal landscape of hacking forms
When an individual is charged with hacking, especially in relation to a hacking form, it's critical to understand the legal framework that governs such actions. Hacking laws can vary significantly between jurisdictions, and each country has its own legislation addressing unauthorized access to computer systems and data theft. For instance, in the United States, the Computer Fraud and Abuse Act (CFAA) serves as a pivotal legislative framework, whereas European countries might look towards the General Data Protection Regulation (GDPR) for aspects of unauthorized access and data breaches.
Being charged with hacking comes with severe implications. The legal consequences can range from hefty fines to imprisonment, depending on the severity of the act and the intent behind it. For tech professionals, such charges can tarnish their reputation, making it difficult to secure future employment. Moreover, one’s personal life could be profoundly affected, with family and social relationships strained due to the stigma associated with being a suspect in a hacking incident.
What is a hacking form?
A hacking form is typically a documentation tool used to report hacking incidents, breaches, or unauthorized access attempts. It serves as a formal record, outlining the nature of the incident and providing a framework for further investigation. The purpose of such forms is critical, as they help organizations comply with legal requirements and assist in formulating defensive strategies against potential cyber threats.
Common scenarios for using hacking forms include employee reports of unauthorized system access, documenting customer asset theft, or compliance with internal security policies following a breach. Their structured design allows investigators to gather all necessary details, facilitating thorough reviews of incidents and subsequent actions.
The role of techie in document creation
For tech professionals, being well-prepared for potential hacking allegations is paramount. Understanding the risks inherent in technology work, including exposure to sensitive data and systems, emphasizes the importance of proper documentation. By utilizing structured forms, techies not only protect themselves legally but also contribute to robust cybersecurity measures within their organizations.
Leveraging tools like pdfFiller can significantly enhance how these professionals create and manage their documentation. This cloud-based solution offers various features tailored for ease of use, ensuring that techies can quickly and effectively fill out hacking forms while maintaining an organized approach to their documents, enabling them to address legal challenges proactively.
How to fill out a hacking form effectively
Filling out a hacking form accurately is essential for ensuring a clear communication of incidents. Begin by gathering all necessary information, including details about the breach, potential suspects, and the nature of the incident involving laptops or customer assets. Understanding each section of the form is vital; this will guide you in providing precise and relevant information.
While completing the form, adhere to best practices such as clarity and conciseness. Avoid jargon unless necessary, and ensure the language is straightforward for investigators. Once completed, review and edit the form meticulously—accurate data reduces the potential for errors that could derail investigations or compromise your position.
Ensuring security and compliance
Maintaining security and compliance during document submissions is non-negotiable. To protect your documents, ensure that you use secure sharing options, encrypt sensitive files, and adhere to organizational policies when submitting hacking forms to authorities or within your company. Implementing these best practices minimizes risks associated with data leakage and assists in protecting your legal standing.
Understanding compliance requirements also plays a critical role in navigating hacking allegations. Engaging with resources provided by pdfFiller allows tech professionals to remain informed about necessary legal standards, ensuring every document submitted aligns with compliance protocols. This proactive stance can bolster one’s defence in the outcome of an investigation.
Case studies
Real-life applications of hacking forms shed light on their importance in legal defense. For example, in recent cases where techies effectively documented incidents using structured forms, they successfully navigated their defenses against hacking charges. By detailing their actions clearly and providing evidence of non-malicious intent, these individuals managed to restore their reputations and find new opportunities in their field.
Conversely, there are numerous cases where improper handling or incomplete forms led to severe repercussions. Tech professionals faced exacerbated legal consequences due to vague statements, underscoring the importance of diligence and thoroughness in this process. Through interviews with legal professionals, insights reveal the pivotal role that well-crafted documentation plays in shaping outcomes of hacking allegations.
Future trends in document management for tech professionals
Future trends in legal requirements indicate a growing scrutiny in documentation processes related to cybersecurity. As laws evolve alongside technology, tech professionals must brace themselves for new regulations surrounding documentation accuracy and accountability. This evolution may demand not only adaptability but also a proactive approach in how incidents are recorded and reported using tools such as pdfFiller.
Additionally, innovations like AI and machine learning are reshaping document management. These technologies can improve the efficiency of creating, filling, and analyzing documents, ultimately facilitating better compliance and security measures. As pdfFiller introduces enhancements driven by these innovations, techies will benefit from streamlined processes designed for evolving legal landscapes.
Frequently asked questions (FAQs)
Common concerns about hacking forms often revolve around misconceptions regarding their purpose and legal implications. Many individuals mistakenly believe that submitting a form absolves them from liability, whereas, in reality, accurate and honest reporting is critical for defense. Clarifying legal jargon is essential to empower techies to take the necessary steps in their defense efforts.
pdfFiller provides resources tailored for tech professionals, including intuitive features that enhance the ease of use in filling out forms. Testimonial highlights from users reflect how the platform has supported them in navigating legal matters effectively. By leveraging tools designed for collaboration and accuracy, techies can maximize their potential during legal challenges.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit techie held for hacking in Chrome?
Can I create an electronic signature for the techie held for hacking in Chrome?
How do I complete techie held for hacking on an iOS device?
What is techie held for hacking?
Who is required to file techie held for hacking?
How to fill out techie held for hacking?
What is the purpose of techie held for hacking?
What information must be reported on techie held for hacking?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.