Get the free Tag: Provision of Security ServicesMinistry of Transport
Get, Create, Make and Sign tag provision of security
Editing tag provision of security online
Uncompromising security for your PDF editing and eSignature needs
How to fill out tag provision of security
How to fill out tag provision of security
Who needs tag provision of security?
Tag Provision of Security Form: A Comprehensive Guide
Understanding tag provision in security forms
Tag provision in the context of security forms refers to the inclusion of specific security identifiers or tags within a document to ensure its integrity and authenticity. These tags can help authenticate the document's origins, track changes, and provide users with a sense of security regarding the information contained within. Without effective tag provision, documents are susceptible to tampering or mishandling, leading to potential data breaches.
Security tags imbue forms with critical attributes that enhance their reliability, ensuring that stakeholders trust the information presented. They prevent unauthorized alterations and safeguard sensitive data, which is essential in sectors like finance, healthcare, and legal affairs. Various types of security tags are employed, such as QR codes, watermarks, and digital signatures, each serving distinct security functions.
Key features of security provisioning in forms
The key features of security provisioning in forms emphasize several critical aspects that collectively fortify a document's security. These elements include user authentication mechanisms, data encryption techniques, and robust document tracking capabilities. Each of these components plays a vital role in safeguarding information and ensuring compliance with data protection regulations.
User authentication mechanisms
User authentication is paramount for maintaining document security. Multi-factor authentication methods are commonly adopted, requiring users to provide additional verification beyond just a password. This might include biometrics or one-time codes sent to devices. Furthermore, user role management systems play a crucial role in controlled access, allowing organizations to define who can view or edit sensitive data.
Data encryption techniques
Encryption is critical in protecting data stored in documents. Techniques like Advanced Encryption Standard (AES) or RSA encryption are widely used to secure data both at rest and in transit. AES, in particular, is known for its speed and security, making it a preferred choice. Ensuring that data is encrypted, whether it's being sent over a network or stored on a server, is essential in protecting against unauthorized access.
Document tracking and audit trails
Document tracking functionality allows organizations to monitor and verify the history of changes made to a form. This capability is vital for compliance with data protection laws and for maintaining document integrity. Audit trails provide a chronological record of who accessed or modified the document, enhancing accountability and helping organizations respond promptly to suspicious activities.
Step-by-step guide to implementing tag provision in security forms
Implementing tag provision in security forms is an organized process that begins with assessing your specific document security needs. Organizations must identify sensitive data within their forms and conduct a risk assessment to evaluate potential vulnerabilities. Understanding these aspects empowers better decision-making when deploying security measures.
Choosing the right software for tag provision
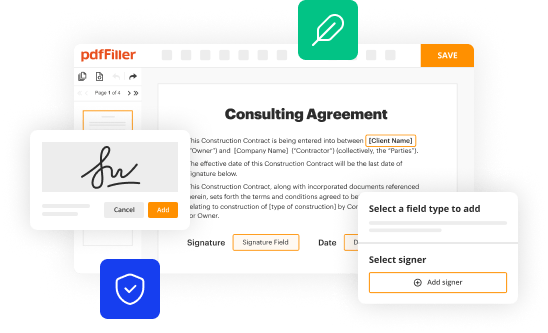
Selecting appropriate software is pivotal. When evaluating document management tools, key features to consider include ease of use, integration capabilities, comprehensive security features, and support for real-time collaboration. Notably, pdfFiller stands out as a top choice due to its robust functionality and seamless integration options.
Setting up security tags in your forms using pdfFiller
Setting up security tags in pdfFiller is straightforward. After creating your document, navigate to the security settings within the tool. Here, you can integrate tags that suit your needs, customize visibility options, and define user permissions. Adopting best practices when configuring these settings ensures your forms are both functional and secure.
Best practices for managing security tags in forms
Implementing best practices in managing security tags is critical for maintaining document integrity. Regularly updating security protocols ensures that your systems are in line with current security standards, protecting against emerging threats. Scheduling periodic reviews of your tagging systems can preempt potential issues that may arise from outdated practices.
Educating users on security practices
Organization-wide education remains fundamental. Effectively training staff on recognizing potential threats, such as phishing attempts or unauthorized access, enhances overall security. Furthermore, sharing best practices for maintaining form security promotes a proactive culture that values data protection.
Troubleshooting common issues with security tags
While implementing tag provisions, users may encounter common issues. Frequent configuration errors can lead to inconsistent tagging or inaccessible documents. Identifying these errors often requires a systematic review of tagging settings to ensure everything aligns correctly. Solutions typically involve revisiting the user permissions and adjusting settings according to established protocols.
FAQs about security forms and tags
Users frequently have questions about security tags. Common inquiries include the effectiveness of digital signatures in preventing forgery and how to ensure that encrypted data remains secure. Addressing these questions helps clarify misconceptions and increases user confidence in document security practices.
Advanced features in pdfFiller for enhanced document security
pdfFiller offers advanced tagging options that allow users to customize tags for specific use cases, enhancing the document's security flexibility. Notably, it includes features such as real-time collaboration while maintaining strict security measures, which enables teams to work efficiently without compromising sensitive information. These advanced options cater to the diverse needs of users seeking enhanced security.
Using integrations to enhance security
The ability to integrate pdfFiller with other security tools significantly enhances document management. By leveraging APIs, users can create more robust security frameworks that benefit from the functionalities of multiple applications, thereby streamlining management processes. This multifaceted approach strengthens overall security and ensures comprehensive protection across all documentation.
Case studies: Successful implementations of tag-provisioned security forms
Exploring case studies of successful implementations reveals valuable insights into the effective use of security tags. For instance, a healthcare organization that incorporated security tags in patient records achieved remarkable improvements in data integrity and patient confidentiality. Lessons learned from high-profile security breaches also underscore the importance of adopting robust tagging mechanisms, as they can prevent costly data leaks and enhance trust.
Future trends in security provisions for document management
Looking ahead, technology innovations in security tagging are expected to center around artificial intelligence and machine learning. These advancements promise to automate security assessments, helping organizations better predict and thwart potential threats. As data landscapes evolve, staying informed about these trends is crucial for maintaining effective security practices.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send tag provision of security for eSignature?
Can I edit tag provision of security on an iOS device?
How do I complete tag provision of security on an iOS device?
What is tag provision of security?
Who is required to file tag provision of security?
How to fill out tag provision of security?
What is the purpose of tag provision of security?
What information must be reported on tag provision of security?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.