Last updated on Dec 17, 2015

Get the free Security Vulnerability Self-Assessment Guide
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Water System Security Guide
The Security Vulnerability Self-Assessment Guide is a legal document used by small drinking water systems to identify and address potential security vulnerabilities.
pdfFiller scores top ratings on review platforms




Who needs Water System Security Guide?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Water System Security Guide
What is the Security Vulnerability Self-Assessment Guide?
The Security Vulnerability Self-Assessment Guide serves as a vital resource for small drinking water systems, specifically tailored for those managing populations between 3,300 and 10,000 residents. This guide aims to identify and address potential security vulnerabilities across various components of the water system, ensuring public safety and compliance with federal regulations.
Key components covered in this document include an assessment of water sources, treatment plants, distribution systems, and personnel management. By leveraging this comprehensive guide, water system personnel can systematically evaluate their security protocols and infrastructure.
Purpose and Benefits of the Security Vulnerability Self-Assessment Guide
This guide is essential for water system personnel to enhance public safety and fulfill legal obligations under the Public Health Security and Bioterrorism Preparedness and Response Act of 2002. By utilizing the vulnerability assessment form, personnel can proactively address security risks and ensure a well-prepared water infrastructure.
The benefits of conducting a thorough vulnerability assessment include improved emergency readiness and enhanced trust from the communities these small drinking water systems serve. Compliance not only safeguards public health but also fortifies the water system's operational integrity.
Who Needs the Security Vulnerability Self-Assessment Guide?
The primary audience for the Security Vulnerability Self-Assessment Guide is water system personnel in Illinois. These individuals are responsible for managing small drinking water systems that cater to communities of varying sizes within the population range mentioned above.
These systems serve critical populations and must adopt comprehensive measures to ensure their infrastructure is secure. The guide enables personnel to identify vulnerabilities specific to their operational environment and enhance preventive strategies.
Key Features of the Security Vulnerability Self-Assessment Guide
This guide encompasses several key features designed to assist in assessing vulnerabilities effectively:
-
Threat identification sections to pinpoint potential security risks.
-
Security measures to be implemented based on the identified threats.
-
Yes/no questions that streamline the assessment process.
-
Action identification sections to document needed security actions.
These features promote a thorough evaluation of current security practices while supporting personnel in making informed recommendations for improvements.
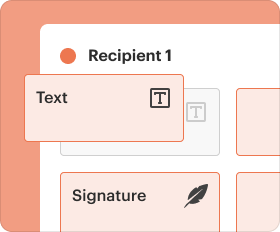
How to Fill Out the Security Vulnerability Self-Assessment Guide Online
Filling out the Security Vulnerability Self-Assessment Guide can be simplified using pdfFiller. Follow these steps to complete the form:
-
Access the Security Vulnerability Self-Assessment Guide on pdfFiller.
-
Fill in required fields, ensuring accuracy for each section.
-
Review your entries for completeness before saving.
This step-by-step process provides clear instructions to guide users in effectively completing the security self-assessment template.
Review and Validation Checklist for the Security Vulnerability Self-Assessment Guide
To ensure accuracy and completeness, it is crucial to use a review and validation checklist when finalizing the Security Vulnerability Self-Assessment Guide. Consider the following:
-
Verify all sections are filled in appropriately.
-
Look for common errors, such as incomplete responses or illegible handwriting.
By adhering to this checklist, water system personnel can avoid common pitfalls that may undermine the document's effectiveness.
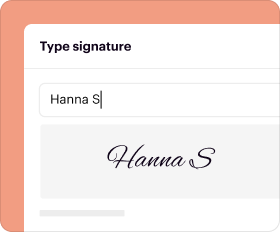
How to Sign and Submit the Security Vulnerability Self-Assessment Guide
Signing the Security Vulnerability Self-Assessment Guide can be done digitally or with a wet signature, depending on submission requirements. Here are the submission methods:
-
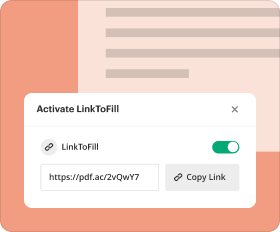
Submit electronically via pdfFiller for quick processing.
-
Mail the completed guide to the designated state agency for further processing.
Understanding these methods ensures compliance with submission guidelines and enhances the efficiency of the assessment process.
What Happens After You Submit the Security Vulnerability Self-Assessment Guide?
Once the Security Vulnerability Self-Assessment Guide is submitted, personnel should track their submission status. This step is essential for understanding the review process and addressing any potential issues proactively.
If amendments or corrections are necessary, water system personnel should be prepared to address feedback from regulatory bodies promptly. Following these protocols helps maintain the integrity of the submission process.
Privacy and Security Measures with the Security Vulnerability Self-Assessment Guide
When handling the Security Vulnerability Self-Assessment Guide, it is vital to implement strong privacy and security measures. This includes utilizing secure platforms such as pdfFiller, which ensures data protection and compliance with regulatory standards.
Water system personnel can rest assured that sensitive information is managed according to applicable data protection regulations, thereby safeguarding both the system and the communities they serve.
Use pdfFiller to Simplify the Security Vulnerability Self-Assessment Process
Utilizing pdfFiller to fill out, sign, and manage the Security Vulnerability Self-Assessment Guide streamlines the entire process. Key features of the platform include:
-
User-friendly interface for easy navigation.
-
Robust security measures for handling sensitive documents.
These capabilities support water system personnel in efficiently managing their assessment tasks while ensuring compliance with security protocols.
How to fill out the Water System Security Guide
-
1.Access pdfFiller and search for 'Security Vulnerability Self-Assessment Guide' in the template library.
-
2.Select the document to open it in the pdfFiller interface, ready for editing.
-
3.Review the sections of the guide and gather necessary information, including details about water sources, treatment plants, and distribution systems.
-
4.Begin filling in the yes/no questions in each section, ensuring accuracy for each component of the water system.
-
5.Use the spaces provided to identify necessary actions and document what actions have already been taken to enhance security.
-
6.Complete the emergency contact list section by entering relevant names, titles, and phone numbers for key personnel.
-
7.After all sections are filled out, review the entire form for any missing information or discrepancies.
-
8.Utilize pdfFiller’s preview feature to see the completed form before finalizing.
-
9.Once satisfied with the form's content, proceed to save your document within pdfFiller.
-
10.You can download your completed form for personal records or submit it directly through pdfFiller if required.
Who is eligible to use the Security Vulnerability Self-Assessment Guide?
The guide is intended for small drinking water systems serving populations between 3,300 and 10,000, specifically for personnel responsible for security assessments.
What is the deadline for completing the vulnerability assessment?
While there is no specific deadline mentioned in the metadata, it's crucial to complete the assessment as part of your emergency preparedness strategy and keep it updated regularly.
How do I submit the completed Self-Assessment Guide?
The completed form can be downloaded for personal records or submitted by designated personnel, as mandated by your local regulatory authority.
What supporting documents do I need to provide?
No additional documents are specifically required with the Security Vulnerability Self-Assessment Guide. However, relevant operational information about your water system may be beneficial to complete the assessment accurately.
What are common mistakes to avoid when filling out the guide?
Avoid leaving yes/no questions unanswered, as this may hinder your vulnerability assessment’s effectiveness. Also, ensure that contact information is accurate and up to date.
How long does it take to process the Security Vulnerability Self-Assessment Guide?
Processing times can vary based on the review requirements set by regulatory agencies. It is advisable to complete the guide promptly to ensure compliance.
What if I need assistance while filling out the form?
If you encounter issues, pdfFiller offers customer support. Additionally, consider consulting local public health or regulatory agency representatives for guidance on completing the assessment correctly.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.