Last updated on Jan 2, 2016
Get the free IT Risk Assessment Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
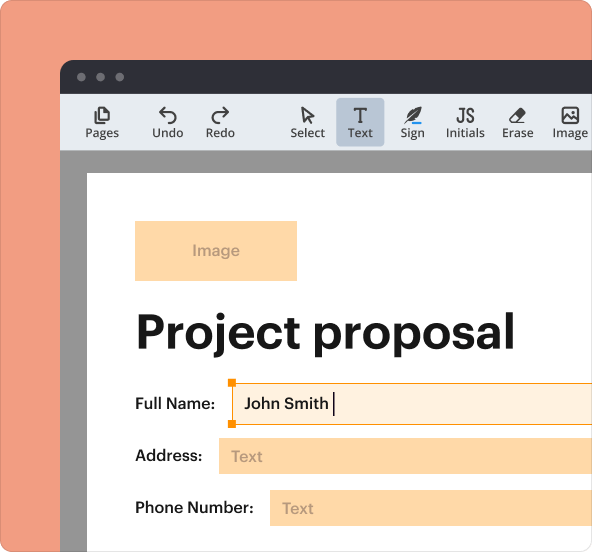
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
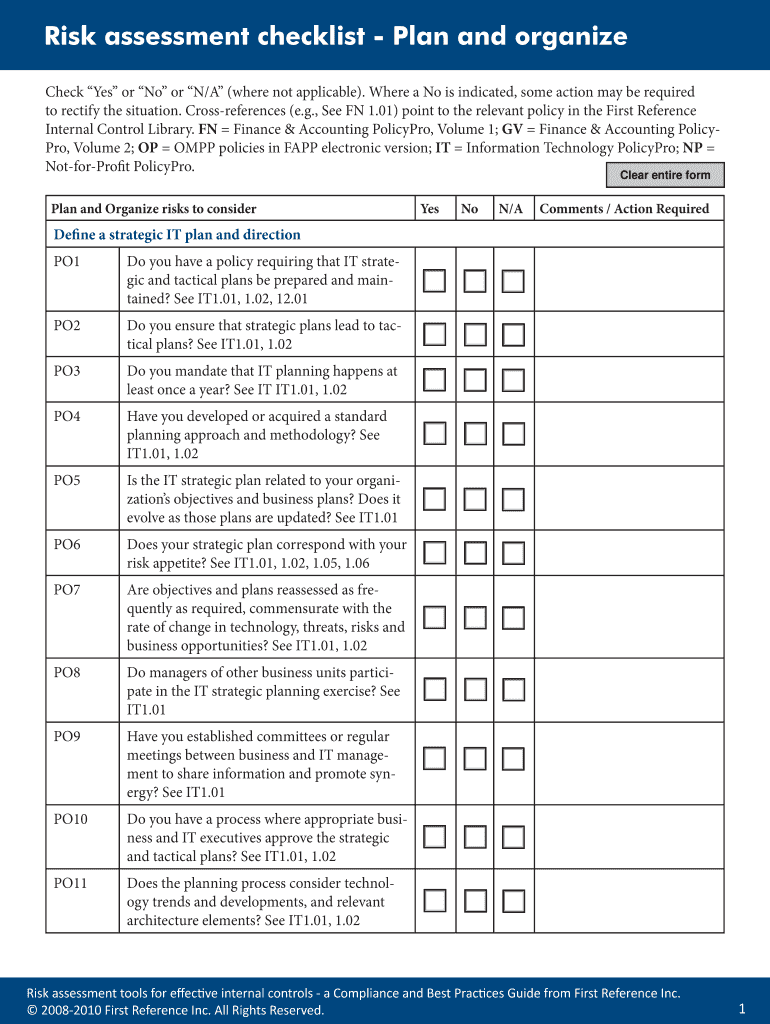
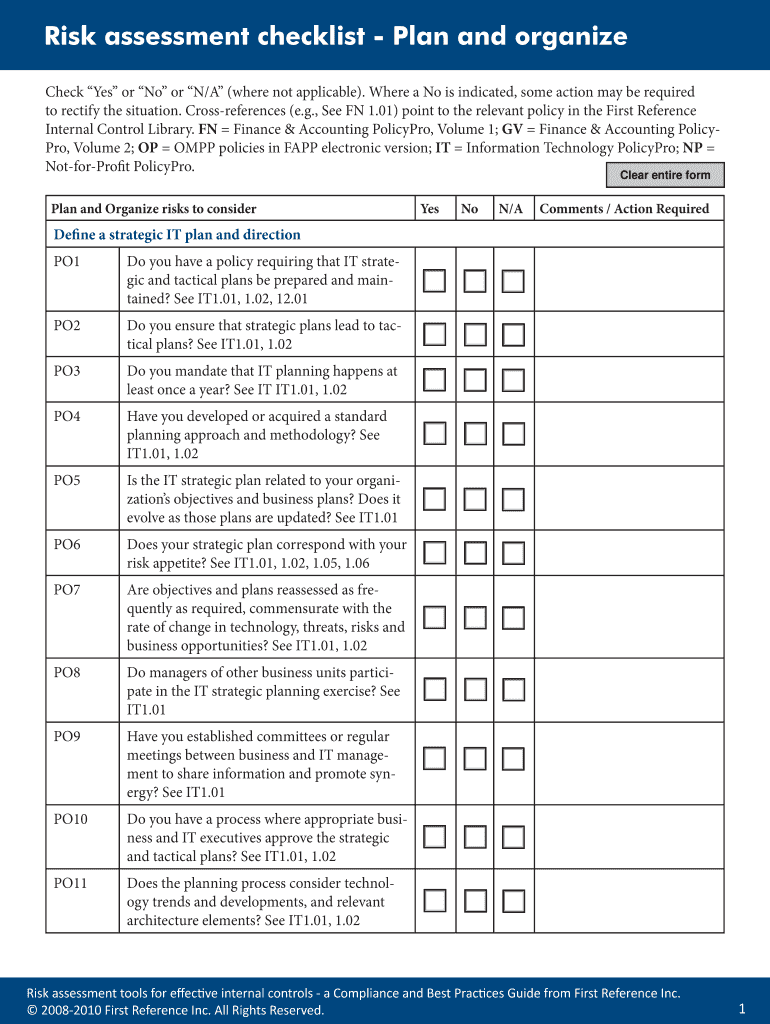
What is IT Risk Checklist
The IT Risk Assessment Checklist is a digital document used by organizations to evaluate and manage IT-related risks effectively.
pdfFiller scores top ratings on review platforms




Who needs IT Risk Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to IT Risk Checklist
What is the IT Risk Assessment Checklist?
The IT Risk Assessment Checklist is a structured tool designed to help organizations evaluate and manage IT-related risks. Its primary objective is to ensure that IT strategies align effectively with overarching business goals. Evaluating and managing IT risks is crucial, as it mitigates potential threats that could compromise operations and data integrity. This checklist serves as a vital resource for organizations aiming to establish robust IT risk management processes.
Benefits of Using the IT Risk Assessment Checklist
Organizations utilize the IT Risk Assessment Checklist for several important reasons. Firstly, it helps identify potential IT risks that could disrupt business continuity. By outlining these risks, it aids in strategic planning and ensures adherence to internal controls. This proactive approach fosters better IT governance and supports organizations in prioritizing their risk management efforts.
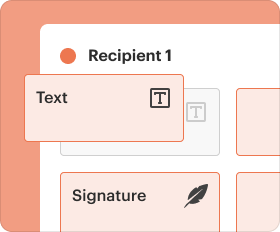
Key Features of the IT Risk Assessment Checklist
The IT Risk Assessment Checklist includes an array of features designed to enhance usability and effectiveness. Key components include a series of targeted questions that assess various IT processes to uncover vulnerabilities. User-friendly elements such as checkboxes and fillable fields make the form easy to navigate. Additionally, it is compatible with digital platforms, further streamlining the assessment process.
Who Needs the IT Risk Assessment Checklist?
This checklist is beneficial for a variety of roles and organizations. IT managers, compliance officers, and risk management professionals will find it especially useful. The checklist is relevant for small businesses and large enterprises alike, as all organizations must prioritize IT risk management. Industries such as finance, healthcare, and manufacturing should particularly consider leveraging this checklist to safeguard their operational integrity.
How to Fill Out the IT Risk Assessment Checklist Online (Step-by-Step)
Completing the IT Risk Assessment Checklist online is a straightforward process. Follow these steps to ensure accurate and effective risk evaluation:
-
Access the checklist and familiarize yourself with its sections.
-
Begin with the general information section, providing necessary details.
-
Navigate through each section, ensuring that you answer all questions thoroughly.
-
Pay special attention to common fields that require detailed responses.
-
Review your answers for clarity and completeness before submission.
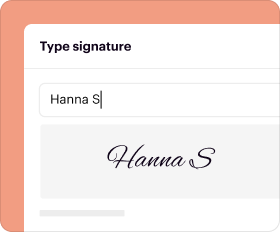
Digital Signature Requirements for the IT Risk Assessment Checklist
Understanding the signature requirements for the IT Risk Assessment Checklist is essential. A digital signature is typically warranted to validate the document; however, alternatives may be acceptable. It's crucial to consider security measures in place when electronically signing documents. Legal aspects concerning digital versus wet signatures must also be acknowledged to ensure compliance.
Security and Compliance Considerations for IT Risk Assessment
Ensuring security and compliance while using the IT Risk Assessment Checklist is vital. pdfFiller provides robust security measures, including 256-bit encryption, to protect sensitive information. Additionally, compliance with important regulations like HIPAA and GDPR is maintained throughout the risk assessment process. Upholding data privacy is paramount as organizations evaluate their IT risks.
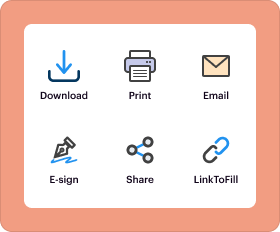
How to Download and Share the IT Risk Assessment Checklist
Once the IT Risk Assessment Checklist is completed, users can easily download and share it. Here are the steps to follow:
-
Click on the download button to save the checklist as a PDF.
-
Choose your preferred method for sharing with stakeholders, such as email or cloud storage.
These steps ensure that your completed checklist is accessible to relevant parties for review and action.
Next Steps After Completing the IT Risk Assessment Checklist
After completing the IT Risk Assessment Checklist, organizations should utilize the results for further risk evaluation in their IT strategy. It's important to outline potential actions or follow-ups based on the checklist findings. Incorporating these findings into ongoing risk management processes will enhance IT governance and support continual improvement.
Make Filling Out Your IT Risk Assessment Checklist Simple with pdfFiller
pdfFiller simplifies the process of filling out your IT Risk Assessment Checklist, making it user-friendly and efficient. Its services include editing, creating, and electronically signing PDF forms to streamline your workflow. Additional features such as format conversion and collaboration tools enhance the overall experience. Start your risk assessment journey with pdfFiller today to ensure a smooth and effective process.
How to fill out the IT Risk Checklist
-
1.To access the IT Risk Assessment Checklist on pdfFiller, visit the website and use the search function to locate the form by its name.
-
2.Once you find the form, click on it to open it in the pdfFiller editor.
-
3.Before you begin filling out the checklist, gather all necessary information about your organization's IT processes, risk management strategies, and compliance requirements.
-
4.Navigate through the form using the editor's toolbar to fill out the fields. Click on each checkbox and text input area to provide your responses.
-
5.As you complete the form, make sure to answer each question thoroughly, reflecting the current state of your IT practices and controls.
-
6.After filling out the checklist, review your answers carefully to ensure that all information is accurate and complete.
-
7.Utilize pdfFiller's preview option to view the completed form before finalizing it.
-
8.Once satisfied with your entries, you can save the document to your account, download it in your preferred format, or submit it directly through pdfFiller's sharing options.
Who is eligible to use the IT Risk Assessment Checklist?
The IT Risk Assessment Checklist is designed for any organization looking to manage IT-related risks, including businesses of all sizes, governmental bodies, and non-profits.
What is the purpose of this checklist?
This checklist serves to help organizations systematically evaluate their IT processes, ensure compliance, and align IT strategies with overall business goals.
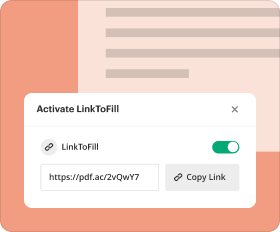
How do I submit the completed checklist?
You can submit the completed checklist by downloading it from pdfFiller and emailing it to the relevant stakeholders or by using pdfFiller's direct sharing features.
What information do I need to complete the checklist?
Before starting, gather information regarding your IT policies, risk management plans, and relevant compliance requirements to provide accurate responses in the checklist.
What are common mistakes to avoid when filling out this form?
Common mistakes include leaving fields blank, providing outdated information, or misunderstanding the specific questions. Review each entry before submission.
How can I ensure the accuracy of my responses?
To ensure accuracy, cross-reference your answers with current IT policies and involve relevant team members in the review process before finalizing the checklist.
Are there any fees associated with using this checklist on pdfFiller?
Using pdfFiller typically involves subscription or pay-per-use fees, but specific costs vary depending on the tools and services you utilize.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.