Last updated on Jan 28, 2016

Get the free Bomb Threat Response Checklist
We are not affiliated with any brand or entity on this form
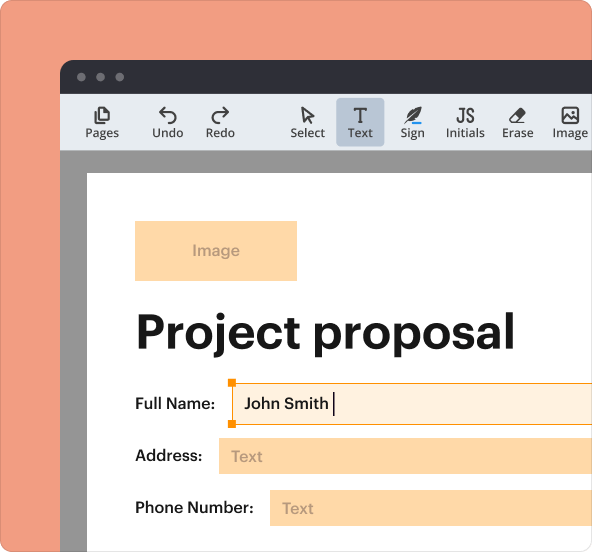
Why pdfFiller is the best tool for your documents and forms
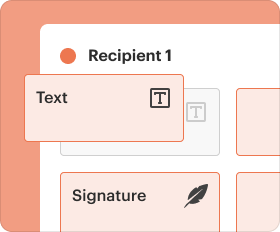
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
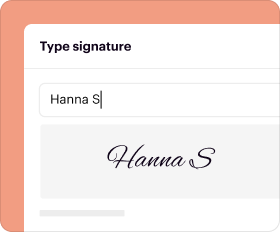
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

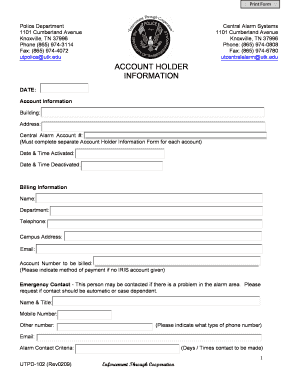
What is Bomb Threat Checklist
The Bomb Threat Response Checklist is an emergency response form used by organizations to systematically handle bomb threats and suspicious packages.
pdfFiller scores top ratings on review platforms




Who needs Bomb Threat Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Bomb Threat Checklist
What is the Bomb Threat Response Checklist?
The Bomb Threat Response Checklist serves as a rapid reference guide aimed at assisting employees and managers in effectively responding to bomb threats. By providing an organized framework, it enhances safety and efficiency within various organizational contexts. The checklist includes essential components, such as fields to record critical details about the threat and step-by-step instructions for appropriate responses during emergencies.
Purpose and Benefits of Using the Bomb Threat Response Checklist
This checklist is vital for maintaining safety and compliance within organizations. It significantly enhances preparedness for potential bomb threats, particularly in commercial facilities and educational institutions. Additionally, it helps in effectively documenting threat details, ensuring that necessary information is available to authorities. The bomb threat guidelines establish a quick and organized response mechanism, crucial in emergency situations.
Key Features of the Bomb Threat Response Checklist
-
Fillable fields designed to capture critical information about the threat.
-
Specific instructions for responding to various threat formats, including phone calls, handwritten notes, and emails.
-
Protocols for identifying suspicious packages to ensure comprehensive safety measures.
Who Should Use the Bomb Threat Response Checklist?
Essential roles that benefit from using the checklist include teachers, security personnel, and administrative staff, ensuring that everyone is prepared to manage bomb threats effectively. This checklist is relevant across diverse sectors, including education, corporate environments, and government agencies. It is imperative for all employees to maintain awareness of security protocols to foster a safer workplace.
How to Fill Out the Bomb Threat Response Checklist Online
-
Access the Bomb Threat Response Checklist on pdfFiller.
-
Carefully fill in the fields, capturing relevant threat information.
-
Follow field-specific instructions to ensure proper documentation.
-
Avoid common errors, such as incomplete information or misclassification of threats.
-
Utilize the validation checklist to review your entries for accuracy.
Security and Compliance Considerations for the Bomb Threat Response Checklist
When handling sensitive documents like the Bomb Threat Response Checklist, implementing robust security measures is crucial. pdfFiller provides various features, such as 256-bit encryption and compliance with standards like HIPAA and GDPR, ensuring confidentiality. Additionally, adhering to best practices for record retention and maintaining privacy is vital for handling such sensitive information.
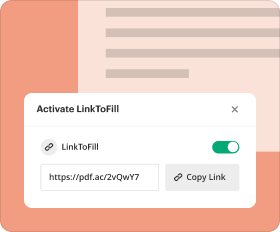
Submission Process for the Bomb Threat Response Checklist
Once the checklist is completed, it can be submitted through various methods, including online platforms, email, or in-person delivery. Adhering to specified timeframes for submission is critical, as delays may lead to adverse consequences. After submission, it is important to follow up with confirmation and tracking procedures to ensure that the checklist has been received and processed appropriately.
What Happens After You Submit the Bomb Threat Response Checklist?
Upon submission, the authorities will evaluate the checklist and initiate the appropriate response process. It's essential to be aware of how to check the status of your submission and to know the next steps should you need further action. Keeping a record of completed checklists is recommended for future reference, ensuring accountability and transparency in the response process.
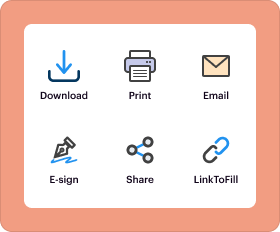
Enhancing Your Document Management with pdfFiller
pdfFiller plays a pivotal role in managing the Bomb Threat Response Checklist efficiently. The platform enables users to fill, edit, and securely store forms, enhancing overall document management. Leveraging this cloud-based solution streamlines emergency documentation and promotes better organization of sensitive records, ensuring that critical information is accessible and actionable.
How to fill out the Bomb Threat Checklist
-
1.Access the Bomb Threat Response Checklist on pdfFiller by visiting their website and searching for the form in their library.
-
2.Once located, click on the form to open it in the pdfFiller interface where you'll see the fillable fields.
-
3.Before filling out the form, gather any necessary information such as details of the threat, caller information, and relevant circumstances surrounding the situation.
-
4.Navigate through the checklist using your mouse to click on each fillable field, entering information as prompted by the form's guidelines.
-
5.For additional instructions, refer to any annotations provided in the checklist to ensure compliance with response procedures.
-
6.Once you have filled in all the required fields, take a moment to review your entries for accuracy.
-
7.Look over the form carefully to confirm that all relevant information has been included and is correctly represented.
-
8.To save your progress, click on the 'Save' option or download the completed form to your device for future use.
-
9.If you need to submit the completed form, follow the submission instructions provided on pdfFiller, which may include emailing or printing the document.
Who is eligible to use the Bomb Threat Response Checklist?
The Bomb Threat Response Checklist can be used by anyone involved in emergency response scenarios, including security personnel, school administrators, and facility managers, to ensure a structured response to bomb threats.
Are there any deadlines associated with filling out this form?
While the Bomb Threat Response Checklist must be completed promptly during an emergency, there are typically no formal deadlines for completing the document after the incident occurs.
How do I submit the completed Bomb Threat Response Checklist?
After filling out the checklist, you can submit it by following the specific submission guidelines provided on pdfFiller, which may include printing, saving, or emailing directly from the platform.
What supporting documents do I need to submit with the checklist?
Generally, there are no additional supporting documents required with the Bomb Threat Response Checklist; however, you might want to keep records of any reports or communications related to the incident.
What are common mistakes to avoid while using the checklist?
Common mistakes include leaving fields blank, providing inaccurate information, or failing to follow the guidelines for recording details about the threat, all of which can undermine the checklist's effectiveness.
How long does it take to process the form once submitted?
Processing times for the Bomb Threat Response Checklist can vary based on organizational protocols and emergency response procedures; however, immediate action is typically taken when a threat is reported.
Can I edit the form after saving it on pdfFiller?
Yes, once saved on pdfFiller, you can return to the Bomb Threat Response Checklist to make any necessary edits or updates, ensuring the information remains accurate.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.