Get the free The Data Breach
Show details
The Data Breach Nightmare Minimizing the Litigation Exposure Michael Vats Step toe & Johnson, LLP New York, NY uveitis steptoe.com 2125063927Litigation RisksCivil lawsuits Including class actionsAgency
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign form data breach
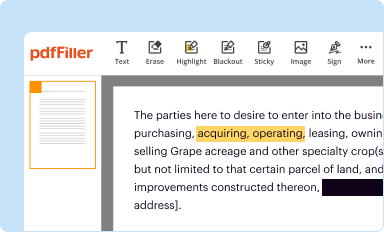
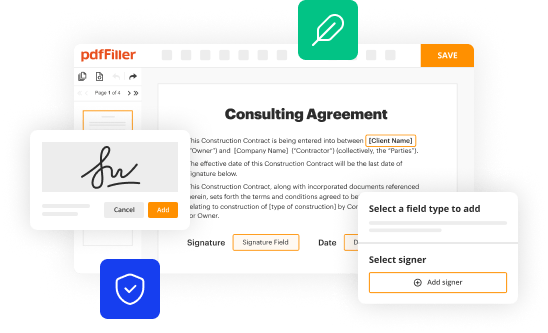
Edit your form data breach form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
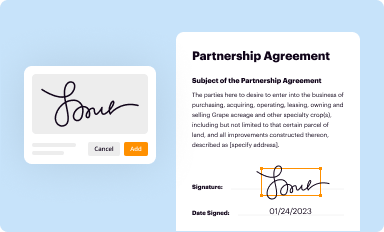
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
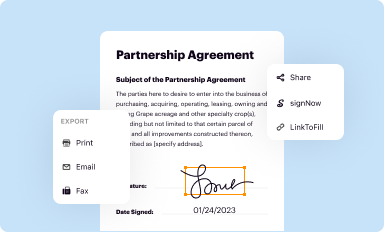
Share your form instantly
Email, fax, or share your form data breach form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing form data breach online
Use the instructions below to start using our professional PDF editor:
1
Log into your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit form data breach. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out form data breach
How to fill out form data breach:
01
Collect all necessary information: Make sure to gather all the required details related to the data breach incident. This includes information such as the date and time of the breach, what data was compromised, how it was accessed, and any other relevant details.
02
Document the incident: Create a written record of the data breach incident. This should include a detailed description of what happened, the potential impact on individuals or entities affected, and any steps taken to mitigate the breach or prevent future incidents.
03
Determine legal obligations: Understand the legal requirements and regulations applicable to data breaches in your jurisdiction. This may include notifying affected individuals or authorities, conducting investigations, or reporting the incident to relevant regulatory bodies.
04
Assess the damage: Evaluate the potential consequences and impact of the data breach. This may involve analyzing the type of data compromised, the sensitivity of the information, and the potential harm it may cause to affected individuals or organizations.
05
Develop a response plan: Create a comprehensive response plan to effectively address the data breach. This should include steps to contain the breach, notify affected parties, implement remedial measures, and prevent future breaches.
06
Communicate with stakeholders: Inform internal and external stakeholders, such as employees, customers, partners, and regulatory bodies, about the data breach incident. Maintain transparent and open communication to build trust and confidence during the recovery process.
07
Review and enhance security measures: Conduct a thorough analysis of your existing data security measures and identify any gaps or weaknesses. Take necessary steps to strengthen your cybersecurity infrastructure and protocols, including implementing encryption, access controls, and regular security audits.
Who needs form data breach?
01
Organizations handling sensitive personal or confidential information: Any entity that collects, stores, or processes sensitive data, such as customer information, financial records, or medical records, needs to be aware of and prepared for data breaches.
02
Data Controllers and Processors: Both data controllers (those who determine the purposes and means of data processing) and data processors (those who process data on behalf of the controller) have a responsibility to safeguard personal data and respond appropriately in the event of a breach.
03
Compliance and Legal Teams: Compliance officers and legal teams within organizations play a crucial role in understanding and complying with data protection laws and regulations. They need to be knowledgeable about data breach notification requirements and ensure proper procedures are followed.
04
IT and Security Professionals: IT and security professionals are responsible for maintaining a secure IT infrastructure and implementing measures to prevent and respond to data breaches. They need to stay updated on the latest cybersecurity threats and best practices to protect sensitive data.
05
Individuals and Data Subjects: Individuals who provide their personal information to organizations should also be aware of data breach risks. They can take proactive steps to protect their own data, such as using strong passwords, enabling two-factor authentication, and being cautious about sharing personal information online.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send form data breach for eSignature?
To distribute your form data breach, simply send it to others and receive the eSigned document back instantly. Post or email a PDF that you've notarized online. Doing so requires never leaving your account.
Can I edit form data breach on an iOS device?
Create, edit, and share form data breach from your iOS smartphone with the pdfFiller mobile app. Installing it from the Apple Store takes only a few seconds. You may take advantage of a free trial and select a subscription that meets your needs.
How do I edit form data breach on an Android device?
You can. With the pdfFiller Android app, you can edit, sign, and distribute form data breach from anywhere with an internet connection. Take use of the app's mobile capabilities.
What is form data breach?
Form data breach is the unauthorized release of sensitive information, usually caused by a cyber attack or security incident.
Who is required to file form data breach?
Organizations and businesses that experience a data breach involving personal information are required to file form data breach.
How to fill out form data breach?
Form data breach is typically filled out by providing details about the breach, including the type of information compromised, the potential impact on affected individuals, and the steps taken to address the breach.
What is the purpose of form data breach?
The purpose of form data breach is to notify the appropriate authorities and affected individuals about the breach, as well as to take necessary steps to mitigate the impact of the breach.
What information must be reported on form data breach?
Information that must be reported on form data breach includes the date and time of the breach, the type of information compromised, the number of affected individuals, and the potential impact of the breach.
Fill out your form data breach online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Form Data Breach is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.