Form Application - Ike Online Gratuito
Drop document here to upload
Up to 100 MB for PDF and up to 25 MB for DOC, DOCX, RTF, PPT, PPTX, JPEG, PNG, JFIF, XLS, XLSX or TXT
Note: Integration described on this webpage may temporarily not be available.
0
Forms filled
0
Forms signed
0
Forms sent
Discover the simplicity of processing PDFs online
Upload your document in seconds
Fill out, edit, or eSign your PDF hassle-free

Download, export, or share your edited file instantly
Top-rated PDF software recognized for its ease of use, powerful features, and impeccable support






Every PDF tool you need to get documents done paper-free
Create & edit PDFs
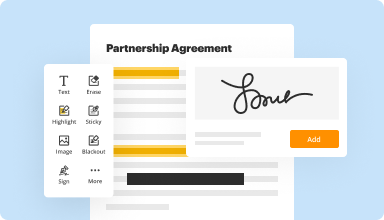
Generate new PDFs from scratch or transform existing documents into reusable templates. Type anywhere on a PDF, rewrite original PDF content, insert images or graphics, redact sensitive details, and highlight important information using an intuitive online editor.
Fill out & sign PDF forms
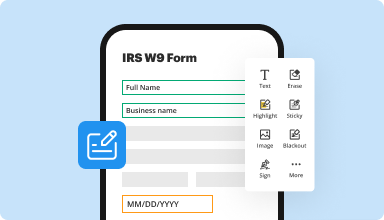
Say goodbye to error-prone manual hassles. Complete any PDF document electronically – even while on the go. Pre-fill multiple PDFs simultaneously or extract responses from completed forms with ease.
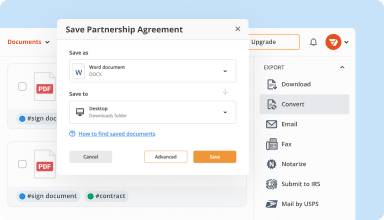
Organize & convert PDFs
Add, remove, or rearrange pages inside your PDFs in seconds. Create new documents by merging or splitting PDFs. Instantly convert edited files to various formats when you download or export them.
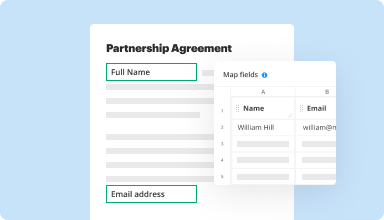
Collect data and approvals
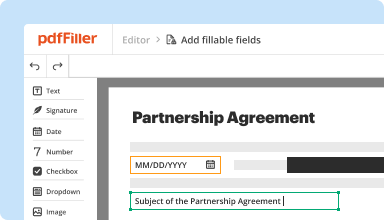
Transform static documents into interactive fillable forms by dragging and dropping various types of fillable fields on your PDFs. Publish these forms on websites or share them via a direct link to capture data, collect signatures, and request payments.
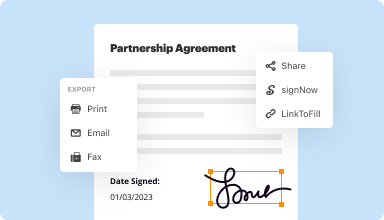
Export documents with ease
Share, email, print, fax, or download edited documents in just a few clicks. Quickly export and import documents from popular cloud storage services like Google Drive, Box, and Dropbox.
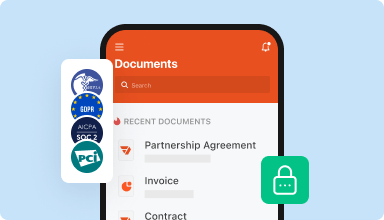
Store documents safely
Store an unlimited number of documents and templates securely in the cloud and access them from any location or device. Add an extra level of protection to documents by locking them with a password, placing them in encrypted folders, or requesting user authentication.
Customer trust by the numbers
64M+
users worldwide
4.6/5
average user rating
4M
PDFs edited per month
9 min
average to create and edit a PDF
Join 64+ million people using paperless workflows to drive productivity and cut costs
Why choose our PDF solution?
Cloud-native PDF editor
Access powerful PDF tools, as well as your documents and templates, from anywhere. No installation needed.
Top-rated for ease of use
Create, edit, and fill out PDF documents faster with an intuitive UI that only takes minutes to master.
Industry-leading customer service
Enjoy peace of mind with an award-winning customer support team always within reach.
What our customers say about pdfFiller
See for yourself by reading reviews on the most popular resources:
This is the greatest help to any business....I am amazed how user friendly and professional this makes for any business large or small. WOW ! Hats off to PDFfiller.
2015-02-12
So far it has met my needs and wants. While there has been a struggle with removing the Electronic disclosure page, their technicians and chat support are quick to respond.
2018-05-29
Great editor, Could have some more funcationality but does 90% of what I want to do. Previously purchased another program (Soda PDF) and couldn't get my head around it. PDFfiller is soo much easier to use, with heaps of online help on how to do anything you want to do.
2018-09-28
PDF FIller was an answer to many questions.
Our business is an industrial maintenance business. We have had to use PDF filler several times with applications and insurance documents. PDF filler made it easier.
We liked how they explained everything we needed to know to fill in applications and other papers online without having to scan and download everything separately. I always thought it was my computer that was the problem, but with PDF filler, it doesn't matter what software is already on your laptop, you can work with any documents.
Sometimes I would go duplicate a step in saving the document, but after a couple of documents, it was easy to figure out what I should do.
2019-03-12
Nice to have
It's good to know that you can use something like this to fill out your documents. You can add and fill out any document you want.
It can be confusing when you are using it. We are using ours online and sometimes you have to wait to do what you want. I have a feeling that it can be faster.
2019-02-22
needed a PDF filler software easy to use
easy to fill out lots of PDF forms without hassle
Easy to use. Can save forms for future use. Does not require any extra learning. Intuitive format makes easy for anyone to use.
Cost was a bit much, but decided the year membership was the best savings deal.
Have used it multiple times already in the first few months so I am glad I did not do a month to month membership.
2017-11-14
First review
It works better than most others I've tried.It is sometimes a bit difficult to navigate as I dont use it too often. I dii have an issue with support, but they did finally undertand my query and they fixed it up, with a very good explanation.
2023-07-16
I have noticed that this is
I have noticed that, although this subreddit has 1,000,020 readers, I am not receiving 1,000,020 upvotes on my posts. I'm not sure if this is being done intentionally or if these "friends" are forgetting to click 'upvote'. Either way, I've had enough. I have compiled a spreadsheet of individuals who have "forgotten" to upvote my most recent posts. After 2 consecutive strikes, your name is automatically highlighted (shown in red) and I am immediately notified. 3 consecutive strikes and you can expect an in-person "consultation". Think about your actions.
2022-09-03
What do you like best?
Easy tools to edit and send email/fax is a breeze
What do you dislike?
Download forms from third party is not useful with provider business names.
Recommendations to others considering the product:
Good for business especially with email and fax service is free.
What problems are you solving with the product? What benefits have you realized?
Leases, company business editing.
2020-11-05
Form Application - Ike Feature
The Form Application - Ike feature streamlines your data collection process, making it easier to create and manage forms. This tool allows users to build custom forms tailored to their specific needs.
Key Features
User-friendly form builder
Customizable templates
Real-time data collection
Integration with popular tools
Mobile-responsive design
Potential Use Cases and Benefits
Collect customer feedback efficiently
Manage event registrations seamlessly
Conduct surveys to gain insights
Facilitate job applications easily
Organize registrations for workshops or classes
By using the Form Application - Ike feature, you can solve common problems related to data collection. Instead of dealing with paper forms or disorganized spreadsheets, you can gather all your responses in one accessible location. This organization helps you save time, reduce errors, and make informed decisions based on accurate information.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What if I have more questions?
Contact Support
What is Ike used for?
The Internet Key Exchange (IKE) is an IPsec (Internet Protocol Security) standard protocol used to ensure security for virtual private network (VPN) negotiation and remote host or network access.
How does IKE protocol work?
Internet Key Exchange (IKE) Internet Key Exchange (IKE) is the protocol used to set up a secure, authenticated communications channel between two parties. IKE typically uses X. 509 PKI certificates for authentication and the DiffieHellman key exchange protocol to set up a shared session secret.
What is the main function of Ike?
The Internet Key Exchange (IKE) is an IPsec (Internet Protocol Security) standard protocol used to ensure security for virtual private network (VPN) negotiation and remote host or network access. The IKE protocol ensures security for SA communication without the reconfiguration that would otherwise be required.
What does Ike need?
IKE has many benefits. It eliminates the need to manually specify all the IPsec security parameters at both peers. It allows the user to specify a particular lifetime for the IPsec security association. Furthermore, encryption can be changed during IPsec sessions. Moreover, it permits certification authority.
What is the difference between IKE Phase 1 and 2?
IKE phase 2 has one mode, called quick mode. Quick mode occurs after IKE has established the secure tunnel in phase 1. It negotiates a shared IPsec policy, derives shared secret keying material used for the IPsec security algorithms, and establishes IPsec SAS. Quick mode exchanges nonce that provide replay protection.
How does IPsec Ike work?
The basic purpose of IKE phase 1 is to authenticate the IPsec peers and to set up a secure channel between the peers to enable IKE exchanges. Performs an authenticated Diffie-Hellman exchange with the end result of having matching shared secret keys. Sets up a secure tunnel to negotiate IKE phase 2 parameters.
What is Ike policy?
Internet Key Exchange (IKE) is a key management protocol that is used to authenticate IPsec peers, negotiate and distribute IPsec encryption keys, and to automatically establish IPsec security associations (SAS). This policy states which security parameters will be used to protect subsequent IKE negotiations.
What is Ike Cisco?
IKE is a key management protocol standard that is used in conjunction with the IPsec standard. IPsec is an IP security feature that provides robust authentication and encryption of IP packets. (ISAM, Oakley, and SKEMA are security protocols implemented by IKE.)
#1 usability according to G2
Try the PDF solution that respects your time.






