Last updated on Mar 23, 2026
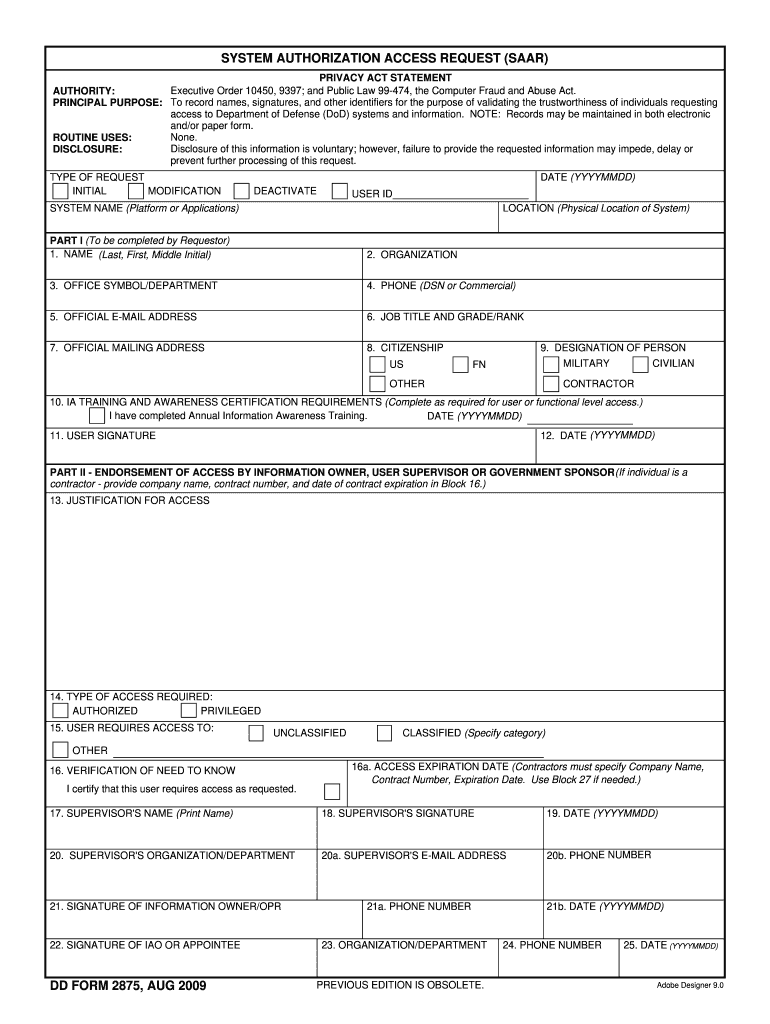
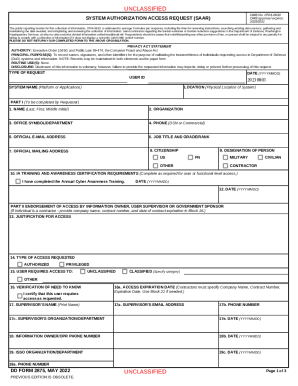
DD 2875 free printable template
pdfFiller is not affiliated with any government organization
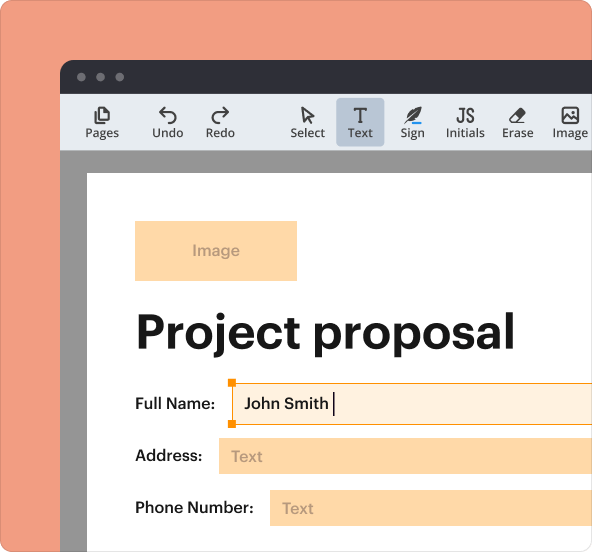
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
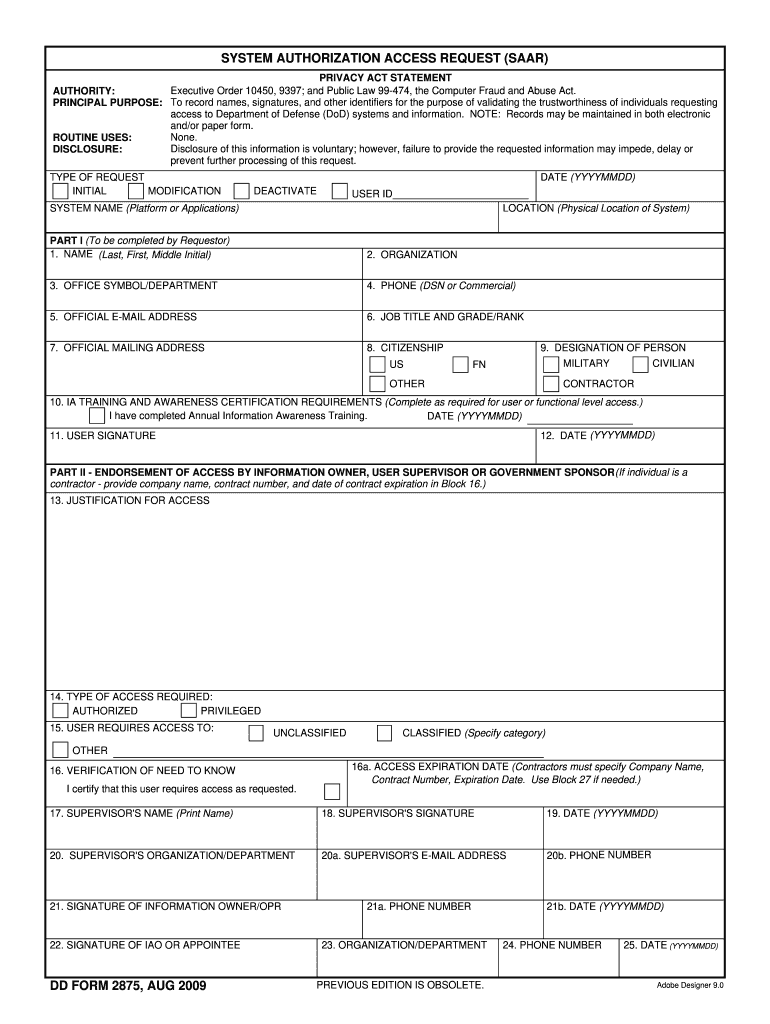
What is DD 2875
The System Authorization Access Request Form is a government document used by the Department of Defense (DoD) to authenticate individuals requesting access to DoD systems and information.
pdfFiller scores top ratings on review platforms




Great features, love the ruler that lets you type straight every line unlike Adobe Acrobat. I really like the compatibility with mobile phones to create your digital signature. Overall I was quite happy and impressed with the software. It would be great if the trial period was longer.
CUSTOMER SERVICE IS HORRIBLE. SOFTWARE KEEPS LOOSING CONNECTION, BUT WHEN WORKING IS GREAT!
Who needs DD 2875?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to DD 2875
What is the DD Form 2875?
The DD Form 2875 is a System Authorization Access Request (SAAR) form used by the Department of Defense (DoD) to validate the trustworthiness of individuals requesting access to DoD systems and information. This form serves an essential role in ensuring that only authorized personnel can manage sensitive data within DoD frameworks. By understanding what the DD Form 2875 entails, users can navigate the access request process more effectively.
Purpose and Benefits of the DD Form 2875
The primary purpose of the DD Form 2875 is to facilitate secure and reliable access to DoD systems. By employing this form, organizations enhance their information handling procedures, ensuring that access is granted in a controlled manner. Benefits of the form include:
-
Securing sensitive information against unauthorized access.
-
Establishing a standardized process for access management.
-
Building trust among stakeholders in handling government operations.
Who Needs to Fill Out the DD Form 2875?
-
Requestor: Initiates the request for access.
-
Supervisor: Reviews and approves the request.
-
Information Owner/OPR: Determines the necessity of access.
-
IAO or Appointee: Authorizes the request for system access.
-
Security Manager: Ensures compliance with security protocols.
Each of these roles is critical in maintaining the integrity and security of DoD information systems.
Key Features and Components of the DD Form 2875
The DD Form 2875 contains vital sections and fields that users need to complete accurately. Notable components include:
-
Personal details of the requestor, including name and contact information.
-
Justification for access, detailing why access is necessary.
-
Required signatures from relevant personnel to validate the request.
This fillable form is designed for ease of use, allowing users to navigate through the required fields efficiently.
How to Fill Out the DD Form 2875 Online: Step-by-Step Guide
To complete the DD Form 2875 online, follow these steps:
-
Gather all necessary personal and organizational information.
-
Access the form on a PDF platform like pdfFiller.
-
Fill out each field accurately, including justification for access.
-
Review the form for completeness and accuracy.
-
Submit the completed form for processing.
Ensure that you pay attention to details, as inaccuracies can delay the process. A downloadable link for the form is available on the official platform.
Common Errors When Completing the DD Form 2875 and How to Avoid Them
When filling out the DD Form 2875, users often encounter common pitfalls. To avoid mistakes, be mindful of the following:
-
Incomplete fields, which can lead to requests being returned.
-
Incorrect signatures, as each role must sign to validate the request.
-
Submission timing, ensuring forms are submitted within deadlines.
Use a validation checklist to review the form before submission, ensuring all required details are present and correct.
Submission Methods for the DD Form 2875
The completed DD Form 2875 can be submitted in multiple ways, enhancing flexibility for users:
-
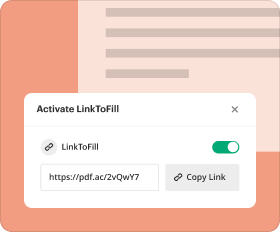
Online submission through the designated DoD portal.
-
Physical submission to the appropriate DoD office.
Be aware of submission timelines, as processing times may vary based on the method chosen. Additionally, confirm if there are any associated fees.
What Happens After You Submit the DD Form 2875?
After submitting the DD Form 2875, users can track the status of their application. Key points to remember include:
-
Regularly checking your application status via the designated tracking system.
-
Understanding common reasons for rejection, including incomplete information or lack of required signatures.
-
Preparing for follow-up actions, such as renewals if access is granted.
Staying informed on the submission process can help manage expectations effectively.
Security and Compliance Considerations for the DD Form 2875
Security is paramount when handling the DD Form 2875. Key considerations include:
-
Utilizing platforms like pdfFiller that offer 256-bit encryption for data protection.
-
Ensuring compliance with regulations such as HIPAA and GDPR during the submission process.
-
Handling sensitive information with care to mitigate risks associated with data breaches.
Prioritizing security ensures that access requests are managed in compliance with government standards.
Enhancing Your Experience with pdfFiller
For a smooth and effective experience while managing the DD Form 2875, consider using pdfFiller. Key features to take advantage of include:
-
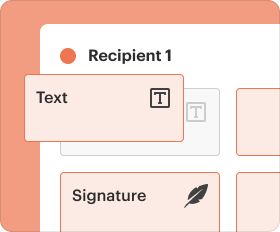
Edit and annotate the form directly within your browser.
-
Create fillable forms to streamline data entry.
-
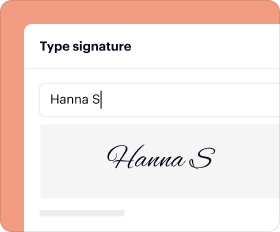
eSign documents securely and share them with necessary stakeholders.
pdfFiller helps simplify the document management process while ensuring a user-friendly interface and robust support for compliance.
How to fill out the DD 2875
-
1.Access pdfFiller and search for the System Authorization Access Request Form.
-
2.Open the form by clicking on it in your pdfFiller dashboard.
-
3.Read through the form instructions provided on the first page to understand the requirements.
-
4.Begin entering your personal information, including your full name, organizational details, and contact information, in the designated fields.
-
5.Provide justification for access within the relevant section of the form.
-
6.Make sure to complete all required fields, indicated by asterisks, to prevent submission errors.
-
7.Gather the necessary information from your supervisor, Information Owner, IAO, and Security Manager for their signatures.
-
8.Utilize pdfFiller's features to electronically sign or add signatures for required signatories.
-
9.Once all sections are completed and signed, review the form thoroughly for accuracy.
-
10.Check that all justifications and signatures are present and valid.
-
11.Finalize the form by clicking the ‘Save’ button to store your progress.
-
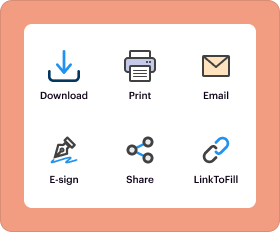
12.To download a copy, select the 'Download' option and choose your preferred format.
-
13.Submit the completed form via email or through your organization's designated submission method.
Who is eligible to submit the System Authorization Access Request Form?
Any individual who requires access to DoD systems, including DoD personnel, contractors, and service members, can submit this form, provided they have the necessary approvals from their supervisor and relevant authorities.
What signatures are required on the form?
The form requires signatures from the requestor, supervisor, Information Owner, Information Assurance Officer (IAO), and Security Manager to validate the access request.
How do I submit the completed form?
The completed form can typically be submitted electronically to your organization's security office or relevant authority via email. Ensure you follow any submission guidelines provided by your organization.
Are there specific deadlines for submitting the form?
Deadlines may vary based on organizational policy or project needs. It's advisable to check with your supervisor for any pertinent timelines regarding access requests.
What supporting documents may be required?
Supporting documents may include identification, proof of employment, and any documentation that justifies the need for access. Check with your organization's guidelines for specific requirements.
What common mistakes should I avoid when filling out the form?
Ensure that all required fields are completed, provide clear justifications for access, and obtain all necessary signatures. Double-check for any misspellings or incomplete sections before submission.
How long will it take to process my request?
Processing times can vary widely based on organizational workload and the nature of the access request. Generally, it may take anywhere from a few days to several weeks, so it's best to plan accordingly.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.