
Get the free HIPAA Security Risk Assessment - GHIMA
Show details
HIPAA Security Risk Analysis and Risk Management Methodology with Step-by-Step Instructions Bob Chart, MA, CHP, CHESS, MUSE 1 2010 HITCH Security Advisors LLC All Rights Reserved Table of Contents
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign hipaa security risk assessment
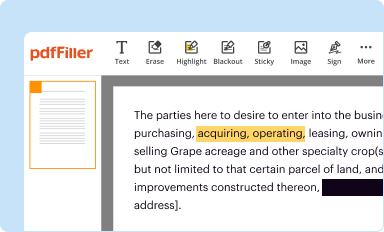
Edit your hipaa security risk assessment form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
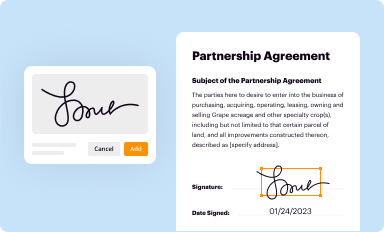
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
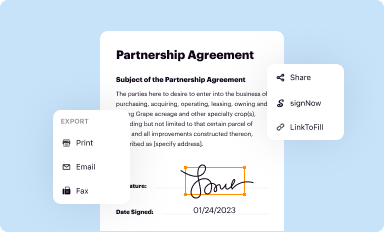
Share your form instantly
Email, fax, or share your hipaa security risk assessment form via URL. You can also download, print, or export forms to your preferred cloud storage service.
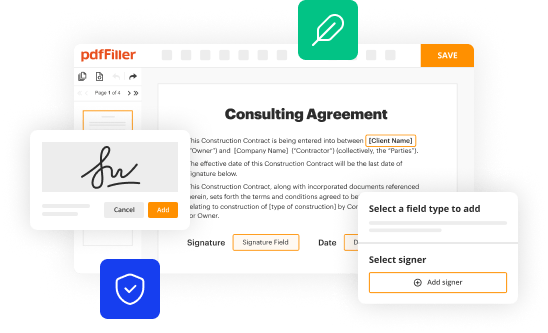
Editing hipaa security risk assessment online
To use the professional PDF editor, follow these steps below:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit hipaa security risk assessment. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out hipaa security risk assessment
How to fill out hipaa security risk assessment:
01
Start by gathering all necessary information and documentation related to your organization's policies, procedures, and systems that handle protected health information (PHI).
02
Review the HIPAA Security Rule, which provides guidelines on how to protect PHI and perform risk assessments. Familiarize yourself with the requirements and recommendations outlined in the rule.
03
Identify all potential risks and vulnerabilities to the confidentiality, integrity, and availability of PHI. This includes physical risks (e.g., theft, natural disasters), technical risks (e.g., outdated software, weak passwords), and administrative risks (e.g., lack of employee training, inadequate access controls).
04
Evaluate and document the likelihood and potential impact of each identified risk. Consider the potential harm that could result from a breach or unauthorized access to PHI, as well as the likelihood of the risk occurring.
05
Determine the current security measures and safeguards that are in place to mitigate these risks. Assess their effectiveness and document any areas where improvements are needed.
06
Identify any gaps or deficiencies in your organization's security measures and safeguards. This could include missing or outdated policies, inadequate training programs, or weak physical security controls.
07
Develop a comprehensive plan to address the identified risks and deficiencies. This plan should detail specific actions, timelines, and responsible parties for implementing necessary changes and improvements.
08
Regularly review and update the risk assessment as needed. This will help ensure that your organization stays up to date with evolving threats and maintains an effective HIPAA compliance program.
Who needs hipaa security risk assessment:
01
Covered Entities: Any healthcare provider that electronically transmits PHI, health plans, and healthcare clearinghouses are required by law to conduct a HIPAA security risk assessment. This includes hospitals, clinics, pharmacies, insurance companies, and billing companies.
02
Business Associates: Any individual or organization that performs services on behalf of a covered entity and handles PHI is also required to conduct a HIPAA security risk assessment. This includes IT companies, consulting firms, medical transcriptionists, and third-party billing companies.
03
Also, any organization that stores, processes, or transmits PHI, even if it is not directly involved in healthcare, should perform a security risk assessment to ensure compliance with HIPAA regulations and protect sensitive patient information.
Remember, it is essential to consult with legal and compliance experts to ensure that your risk assessment and HIPAA compliance efforts align with the specific requirements and regulations applicable to your organization.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is hipaa security risk assessment?
HIPAA security risk assessment is a process that helps identify potential risks to protected health information (PHI) and assess the security measures in place to protect that information.
Who is required to file hipaa security risk assessment?
Covered entities and business associates under HIPAA are required to conduct and document a security risk assessment.
How to fill out hipaa security risk assessment?
HIPAA security risk assessment can be filled out by following the guidelines provided by the Office for Civil Rights (OCR) and using tools and templates available online.
What is the purpose of hipaa security risk assessment?
The purpose of HIPAA security risk assessment is to identify vulnerabilities in the security measures protecting PHI and to implement safeguards to mitigate those risks.
What information must be reported on hipaa security risk assessment?
HIPAA security risk assessment must include an inventory of all systems containing PHI, a risk analysis of potential threats, and a risk management plan to address those risks.
How can I send hipaa security risk assessment to be eSigned by others?
To distribute your hipaa security risk assessment, simply send it to others and receive the eSigned document back instantly. Post or email a PDF that you've notarized online. Doing so requires never leaving your account.
How can I fill out hipaa security risk assessment on an iOS device?
Make sure you get and install the pdfFiller iOS app. Next, open the app and log in or set up an account to use all of the solution's editing tools. If you want to open your hipaa security risk assessment, you can upload it from your device or cloud storage, or you can type the document's URL into the box on the right. After you fill in all of the required fields in the document and eSign it, if that is required, you can save or share it with other people.
How do I fill out hipaa security risk assessment on an Android device?
Complete hipaa security risk assessment and other documents on your Android device with the pdfFiller app. The software allows you to modify information, eSign, annotate, and share files. You may view your papers from anywhere with an internet connection.
Fill out your hipaa security risk assessment online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Hipaa Security Risk Assessment is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















