Get the free Access control & security systems. updated 11202015 - csuohio
Show details
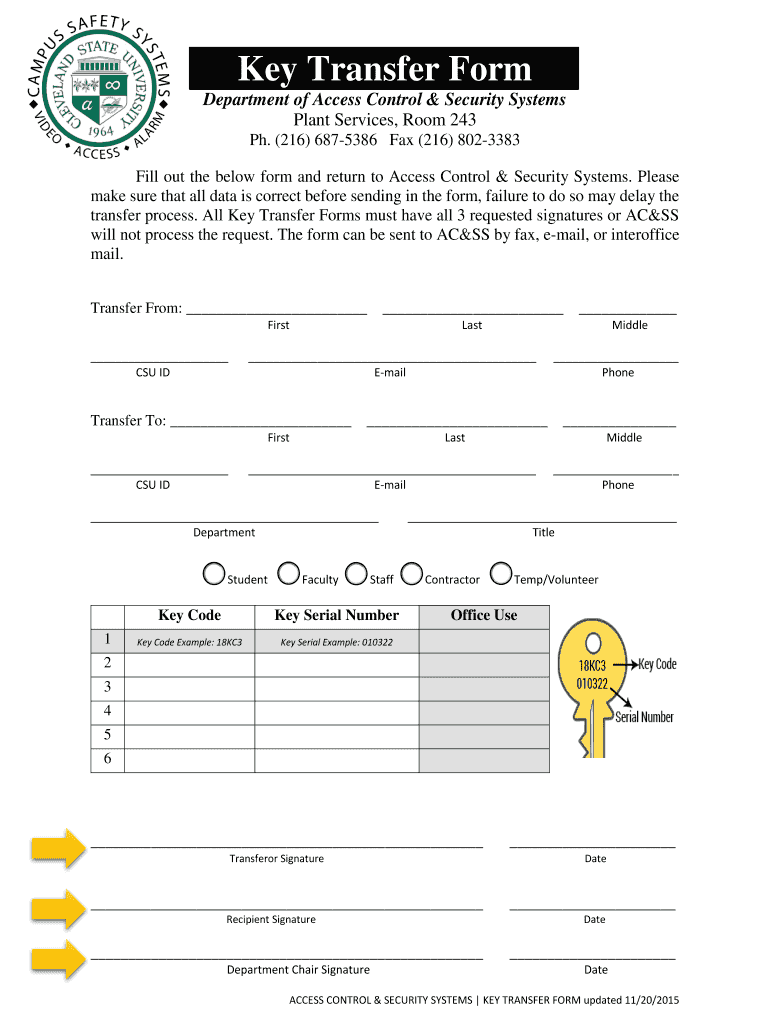
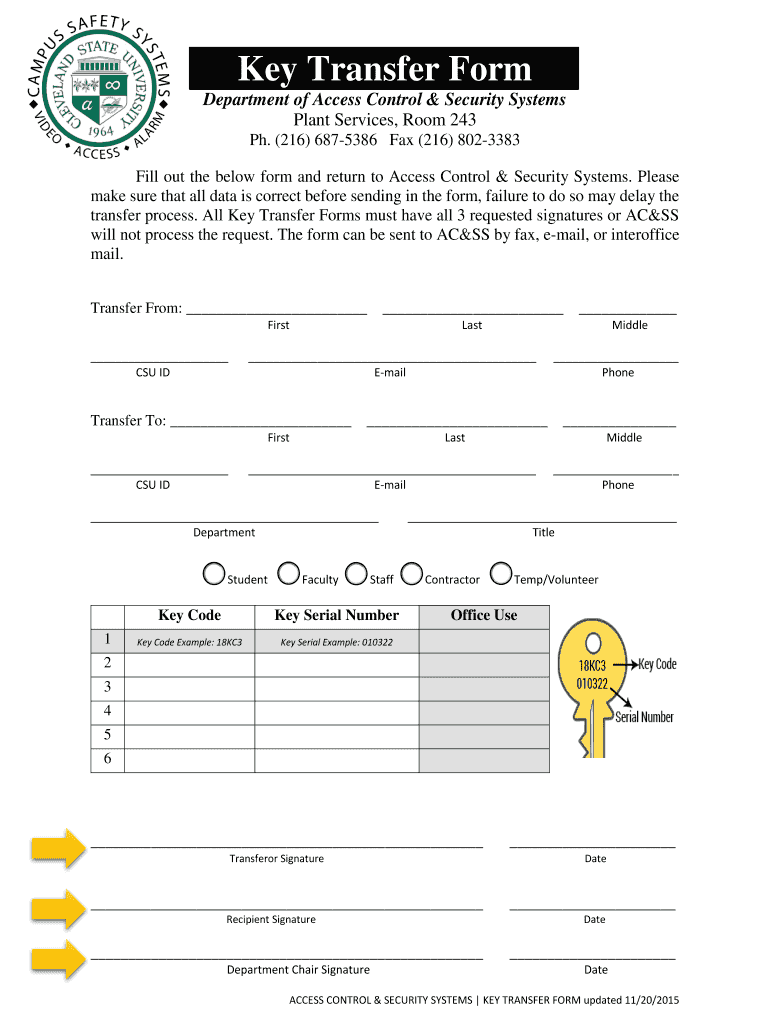
Key Transfer Form. Department of Access Control & Security Systems. Plant Services, Room 243. PH. (216) 6875386 Fax (216) 8023383. ACCESS CONTROL...
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign access control amp security
Edit your access control amp security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your access control amp security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit access control amp security online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit access control amp security. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out access control amp security
How to fill out access control & security:
01
Identify the areas or resources that require access control. This could include physical spaces such as doors, gates, or rooms, as well as digital resources like computer networks, files, or databases.
02
Determine the different levels of access required for each area or resource. This could involve creating different access groups or roles with specific permissions. For example, some users may require full access, while others may only need read-only access.
03
Implement access control measures such as passwords, authentication systems, or keycard entry systems to restrict access to authorized individuals only. This could involve setting up strong passwords, regularly changing them, or using multi-factor authentication for added security.
04
Regularly review and update access control policies and procedures. As new employees join or leave the organization, it is important to revoke or grant access accordingly. Similarly, access privileges should be regularly reviewed to ensure they are up to date and aligned with organizational needs.
05
Monitor and audit access control systems to detect any unauthorized access or security breaches. This could involve implementing logging systems, conducting periodic security audits, or using security cameras to keep track of access activity.
Who needs access control & security:
01
Businesses and organizations of all sizes, ranging from small startups to large corporations, require access control and security measures. Access control ensures that only authorized individuals can access sensitive information or resources, protecting them from unauthorized access or potential breaches.
02
Industrial facilities, research labs, or manufacturing plants need access control & security to protect valuable assets, trade secrets, or confidential data. Restricting access to certain areas or equipment ensures that only trained and authorized personnel can operate or access them.
03
Educational institutions such as schools, colleges, or universities also require access control to secure their campuses and protect students, staff, and sensitive information. Restricting access to certain areas or facilities can help prevent unauthorized entry or potential threats.
04
Government organizations or agencies need access control & security to safeguard classified information, secure sensitive locations, or protect critical infrastructure from potential threats. Access control measures ensure that only authorized personnel can access restricted areas or resources.
05
Healthcare facilities such as hospitals, clinics, or research laboratories require access control & security to protect patient records, sensitive medical equipment, or pharmaceutical supplies. Restricting access to certain areas ensures that only authorized healthcare professionals can access critical resources.
In summary, access control & security is necessary for a wide range of organizations and institutions to protect valuable assets, ensure the safety of individuals, and safeguard sensitive information from unauthorized access or potential breaches.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit access control amp security from Google Drive?
By integrating pdfFiller with Google Docs, you can streamline your document workflows and produce fillable forms that can be stored directly in Google Drive. Using the connection, you will be able to create, change, and eSign documents, including access control amp security, all without having to leave Google Drive. Add pdfFiller's features to Google Drive and you'll be able to handle your documents more effectively from any device with an internet connection.
How do I edit access control amp security on an iOS device?
Create, edit, and share access control amp security from your iOS smartphone with the pdfFiller mobile app. Installing it from the Apple Store takes only a few seconds. You may take advantage of a free trial and select a subscription that meets your needs.
How do I fill out access control amp security on an Android device?
Complete your access control amp security and other papers on your Android device by using the pdfFiller mobile app. The program includes all of the necessary document management tools, such as editing content, eSigning, annotating, sharing files, and so on. You will be able to view your papers at any time as long as you have an internet connection.
What is access control amp security?
Access control amp security is a system that manages who has access to certain resources or areas, and ensures that only authorized individuals are allowed entry.
Who is required to file access control amp security?
Access control amp security must be filed by any entity or organization that needs to restrict access to certain information, data, or physical locations.
How to fill out access control amp security?
Access control amp security is typically filled out by using specialized software or hardware that allows administrators to set permissions and restrictions for users.
What is the purpose of access control amp security?
The purpose of access control amp security is to protect sensitive information, assets, and resources from unauthorized access.
What information must be reported on access control amp security?
Access control amp security reports typically include details about user access levels, permission settings, and any security incidents or breaches.
Fill out your access control amp security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Access Control Amp Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















