Get the free Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Confi...
Show details
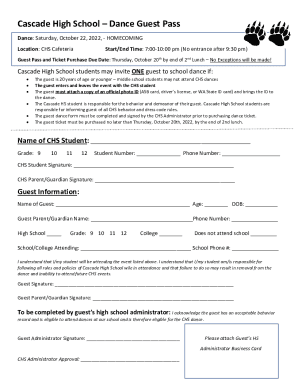
This thesis investigates the application of CUDA-enabled GPUs to accelerate cryptographic algorithms, specifically AES, SHA-2, and Keccak, evaluating their performance in typical system configurations.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cryptographic algorithm acceleration using

Edit your cryptographic algorithm acceleration using form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cryptographic algorithm acceleration using form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing cryptographic algorithm acceleration using online
To use the professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit cryptographic algorithm acceleration using. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cryptographic algorithm acceleration using

How to fill out Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations
01
Ensure that your system has a CUDA-enabled GPU installed.
02
Install the CUDA Toolkit and drivers suitable for your GPU.
03
Download the cryptographic algorithm libraries compatible with CUDA.
04
Integrate the cryptographic libraries into your development environment.
05
Create a project that references the CUDA libraries for cryptographic computations.
06
Write or adapt your cryptographic algorithms to leverage parallel processing using CUDA.
07
Compile your project, verifying that there are no errors.
08
Run your application and monitor performance improvements in cryptographic processing.
Who needs Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations?
01
Organizations requiring high-speed cryptographic processing for data security.
02
Developers working on applications involving encryption and decryption tasks.
03
Researchers in the field of cryptography looking for accelerated testing.
04
Enterprises dealing with large volumes of sensitive data that need real-time processing.
05
Government and financial institutions that prioritize data security and compliance.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations?
Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs refers to the leveraging of CUDA (Compute Unified Device Architecture) technology to enhance the performance of cryptographic algorithms by utilizing the parallel processing capabilities of NVIDIA GPUs. This acceleration allows for faster data encryption, decryption, and hashing in systems configured with CUDA-enabled graphics cards.
Who is required to file Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations?
Typically, entities that implement or utilize cryptographic technologies within their systems for security purposes, such as businesses, government agencies, and developers working with sensitive data or applications requiring encryption, are required to consider or report on the use of CUDA-enabled GPUs for cryptographic acceleration.
How to fill out Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations?
Filling out the documentation for Cryptographic Algorithm Acceleration involves detailing the system configuration, specifying the GPU models being used, outlining the cryptographic algorithms that benefit from acceleration, and providing performance metrics showing improvements. It's important to follow any regulatory guidelines applicable to the reporting or documentation.
What is the purpose of Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations?
The purpose is to enhance the efficiency and speed of cryptographic operations, thereby improving the overall security performance of applications. This technology aims to reduce the processing time for encryption and decryption tasks, making systems more capable of handling high volumes of cryptographic operations efficiently.
What information must be reported on Cryptographic Algorithm Acceleration Using CUDA Enabled GPUs in Typical System Configurations?
Information that must be reported includes details on the system hardware and software configurations, the specific CUDA-enabled GPUs utilized, the cryptographic algorithms being accelerated, relevant benchmarking statistics, and any security compliance measures taken alongside GPU acceleration.
Fill out your cryptographic algorithm acceleration using online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Cryptographic Algorithm Acceleration Using is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.