Get the free ISMS Implementation Guide and Examplesdoc - atsec
Show details
ATSEM information security corporation 9130 Jollyville Road, Suite 260 Austin, TX 78759 Tel: 5126157300 Fax: 5126157301 www.atsec.com a t sec in f or m ATI on sec your I thank you ISMS Implementation
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign isms implementation guide and
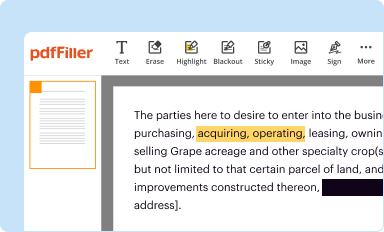
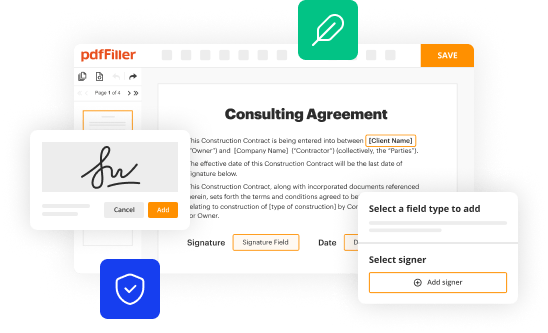
Edit your isms implementation guide and form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your isms implementation guide and form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing isms implementation guide and online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit isms implementation guide and. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out isms implementation guide and
How to fill out ISMS implementation guide and:
01
Begin by familiarizing yourself with the purpose and scope of the ISMS implementation guide. Understand the key objectives and desired outcomes of the guide.
02
Review the template or format provided for the ISMS implementation guide. Take note of the sections or categories that need to be filled out, such as risk assessment, security policies, incident response plans, and controls.
03
Gather the necessary information and documentation for each section of the guide. This may include company policies, risk assessments, legal requirements, and any existing security measures already in place.
04
Start with the risk assessment section. Identify the potential threats and vulnerabilities that your organization may face. Assess the likelihood and impact of each threat, and determine the necessary controls to mitigate these risks.
05
Move on to the security policies section. Define and document your organization's security policies, such as access control, information classification, and data protection. Ensure that these policies align with industry best practices and standards.
06
Proceed to the incident response plans section. Outline the steps to be taken in the event of a security incident or breach. Clearly define roles and responsibilities, communication channels, and escalation procedures.
07
Lastly, address the controls section. Document the specific security controls that your organization has implemented to protect against identified risks. Include details on technical and procedural controls, as well as any monitoring or auditing mechanisms in place.
Who needs ISMS implementation guide and:
01
Organizations that are planning to implement an Information Security Management System (ISMS) can benefit from using an ISMS implementation guide. It provides a structured framework and guidance to ensure the successful implementation of security measures.
02
Businesses that handle sensitive or confidential information, such as personal data, financial records, or intellectual property, should consider using an ISMS implementation guide. It helps in identifying and managing risks associated with the protection of this information.
03
Companies seeking to comply with industry standards and regulations, such as ISO 27001, may find an ISMS implementation guide invaluable. It helps in meeting the requirements and demonstrating the effectiveness of the implemented security controls.
Overall, any organization that values the security and protection of their information assets can benefit from using an ISMS implementation guide. It provides a comprehensive approach to managing information security risks and ensuring the confidentiality, integrity, and availability of critical information.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send isms implementation guide and to be eSigned by others?
When you're ready to share your isms implementation guide and, you can send it to other people and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail. You can also notarize your PDF on the web. You don't have to leave your account to do this.
How do I make edits in isms implementation guide and without leaving Chrome?
Install the pdfFiller Chrome Extension to modify, fill out, and eSign your isms implementation guide and, which you can access right from a Google search page. Fillable documents without leaving Chrome on any internet-connected device.
Can I sign the isms implementation guide and electronically in Chrome?
Yes. You can use pdfFiller to sign documents and use all of the features of the PDF editor in one place if you add this solution to Chrome. In order to use the extension, you can draw or write an electronic signature. You can also upload a picture of your handwritten signature. There is no need to worry about how long it takes to sign your isms implementation guide and.
What is isms implementation guide and?
ISMS implementation guide is a document detailing the steps and processes involved in implementing an Information Security Management System (ISMS) within an organization.
Who is required to file isms implementation guide and?
Any organization that wants to implement an ISMS and achieve certification such as ISO 27001 is required to file an ISMS implementation guide.
How to fill out isms implementation guide and?
ISMS implementation guide can be filled out by documenting the organization's security policies, procedures, risk assessments, and control measures in line with ISO 27001 standards.
What is the purpose of isms implementation guide and?
The purpose of ISMS implementation guide is to provide a roadmap for organizations to follow in order to effectively implement an ISMS and enhance their information security management practices.
What information must be reported on isms implementation guide and?
An ISMS implementation guide must include details on the organization's risk assessment, security controls, policies and procedures, roles and responsibilities, and monitoring and review processes.
Fill out your isms implementation guide and online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Isms Implementation Guide And is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.