Get the free Security Vulnerability Assessment Program - bnab-bbabbcomb
Show details
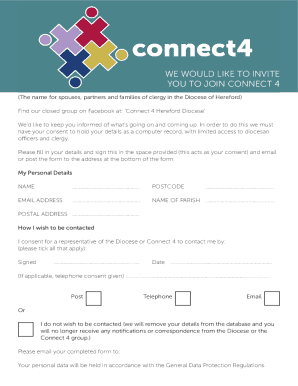
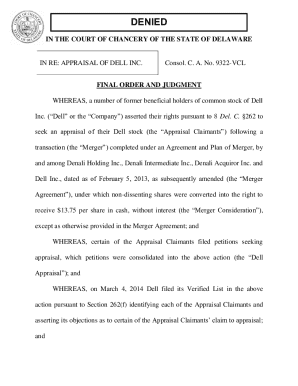
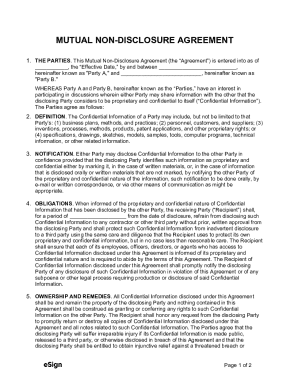
Security Vulnerability Assessment Program Registration Form (Please Print or Type) Business Name: Site Reference: (ex. Satellite or Plant) USPS Shipping Address: (No PO Boxes) City State Zip Contact
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security vulnerability assessment program

Edit your security vulnerability assessment program form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your security vulnerability assessment program form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing security vulnerability assessment program online
To use the professional PDF editor, follow these steps below:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit security vulnerability assessment program. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security vulnerability assessment program

How to fill out a security vulnerability assessment program:
01
Begin by conducting a thorough inventory of all your organization's assets, including hardware, software, networks, and data.
02
Identify and document potential threats and vulnerabilities that may affect the security of these assets. This can include known security flaws, outdated software versions, weak passwords, or inadequate physical security measures.
03
Prioritize the identified risks based on their potential impact and likelihood of occurrence. This will help you allocate resources and prioritize mitigation efforts effectively.
04
Develop a comprehensive plan to address each identified risk. This plan should outline specific actions, responsibilities, and timelines for implementing the necessary security controls or countermeasures.
05
Implement the suggested security controls and monitor their effectiveness regularly. This may involve patching software vulnerabilities, updating hardware firmware, strengthening access controls, or improving physical security measures.
06
Regularly reassess the effectiveness of your security vulnerability assessment program and update it accordingly. This will ensure that you stay abreast of new threats and vulnerabilities that may arise over time.
Who needs a security vulnerability assessment program:
01
Any organization that stores or processes sensitive or valuable information, such as customer data, financial records, or intellectual property, can benefit from a security vulnerability assessment program.
02
Industries with rigorous legal and regulatory compliance requirements, such as healthcare, financial services, or government agencies, often have a heightened need for such programs.
03
Organizations that rely heavily on technology and have a significant online presence, such as e-commerce platforms or cloud service providers, must regularly assess their security vulnerabilities to mitigate the risk of cyberattacks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get security vulnerability assessment program?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific security vulnerability assessment program and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
How do I make edits in security vulnerability assessment program without leaving Chrome?
Install the pdfFiller Google Chrome Extension to edit security vulnerability assessment program and other documents straight from Google search results. When reading documents in Chrome, you may edit them. Create fillable PDFs and update existing PDFs using pdfFiller.
Can I create an eSignature for the security vulnerability assessment program in Gmail?
Create your eSignature using pdfFiller and then eSign your security vulnerability assessment program immediately from your email with pdfFiller's Gmail add-on. To keep your signatures and signed papers, you must create an account.
Fill out your security vulnerability assessment program online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Security Vulnerability Assessment Program is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.