Get the free Common Exploits
Show details
Common Exploits and How to Prevent Them David SvobodaSoftware Engineering Institute Carnegie Mellon University Pittsburgh, PA 15213 Common Exploits and How to Prevent Them 2016 Carnegie Mellon University
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign common exploits
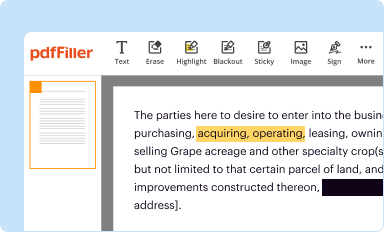
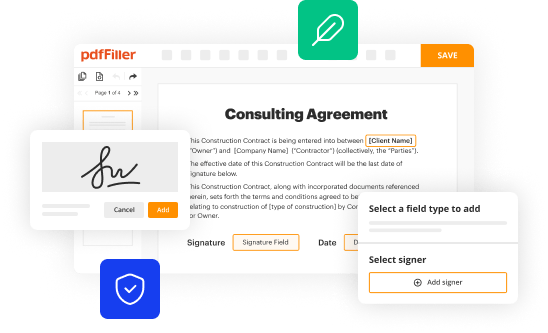
Edit your common exploits form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
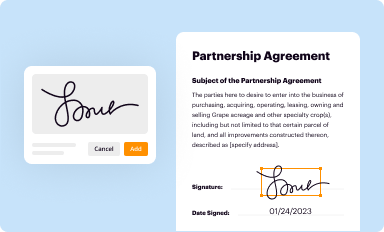
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
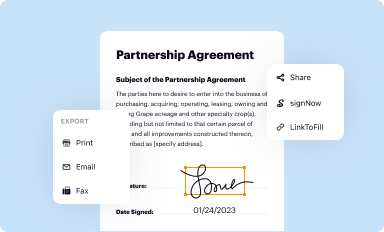
Share your form instantly
Email, fax, or share your common exploits form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing common exploits online
Follow the guidelines below to take advantage of the professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit common exploits. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out common exploits
How to fill out common exploits
01
Identify the target system or application that you want to exploit.
02
Research and gather information about the vulnerabilities commonly found in the target system or application.
03
Select a suitable exploit technique based on the identified vulnerabilities.
04
Obtain or develop the necessary exploit code for the chosen technique.
05
Understand the specifics of the target system or application to ensure the exploit is compatible.
06
Test the exploit in a controlled environment to ensure its effectiveness and functionality.
07
Plan the execution of the exploit, considering factors such as timing and potential consequences.
08
Execute the exploit on the target system or application, following the steps and precautions determined in the previous stages.
09
Monitor the outcome of the exploit, collect any valuable data or control gained.
10
Cover tracks and ensure that no evidence or traces of the exploit are left behind.
11
Document the entire process, including the steps taken, the vulnerabilities exploited, and any lessons learned.
12
Stay updated with the latest exploit techniques and vulnerabilities to enhance your skills and knowledge.
Who needs common exploits?
01
Ethical hackers and penetration testers who are hired to identify and fix security vulnerabilities in systems.
02
System administrators and IT professionals responsible for securing their organization's networks and applications.
03
Security researchers who aim to discover and report vulnerabilities to improve overall system security.
04
Developers who want to understand how exploits work to create more secure software.
05
Law enforcement agencies investigating cybercrime and seeking to understand and prevent exploit usage.
06
Red teamers and security enthusiasts who engage in ethical hacking challenges and competitions.
07
Organizations or individuals who want to test the security posture of their systems and applications.
08
Cybersecurity students and enthusiasts who want to learn about the techniques used in exploiting vulnerabilities.
09
Governments and intelligence agencies for offensive security purposes.
10
Individuals with malicious intent who intend to exploit systems for personal gain or causing harm (unethical use).
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit common exploits straight from my smartphone?
The easiest way to edit documents on a mobile device is using pdfFiller’s mobile-native apps for iOS and Android. You can download those from the Apple Store and Google Play, respectively. You can learn more about the apps here. Install and log in to the application to start editing common exploits.
How do I fill out common exploits using my mobile device?
The pdfFiller mobile app makes it simple to design and fill out legal paperwork. Complete and sign common exploits and other papers using the app. Visit pdfFiller's website to learn more about the PDF editor's features.
How do I edit common exploits on an Android device?
You can make any changes to PDF files, such as common exploits, with the help of the pdfFiller mobile app for Android. Edit, sign, and send documents right from your mobile device. Install the app and streamline your document management wherever you are.
What is common exploits?
Common exploits are known vulnerabilities in software or systems that malicious actors can use to gain unauthorized access or disrupt normal operations.
Who is required to file common exploits?
Any organization or individual that discovers a common exploit is required to file a report with the relevant authorities.
How to fill out common exploits?
Common exploits can be reported through online platforms or by contacting the appropriate cybersecurity agencies.
What is the purpose of common exploits?
The purpose of reporting common exploits is to enable timely patching of vulnerabilities and prevent potential cyber attacks.
What information must be reported on common exploits?
Information such as the type of exploit, affected systems, potential impact, and any mitigating measures taken should be included in the report.
Fill out your common exploits online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Common Exploits is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.