Get the free Configure Basic AP Security via GUI FWL v11 - media fdtc
Show details
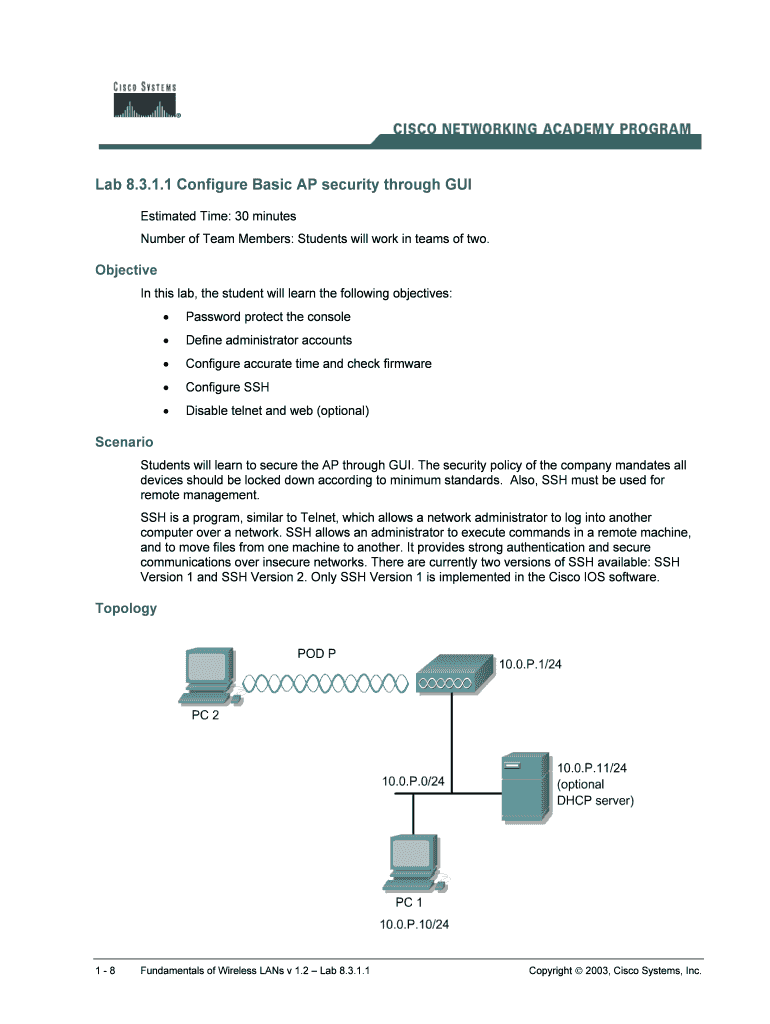
Lab 8.3.1.1 Configure Basic AP security through GUI Estimated Time: 30 minutes Number of Team Members: Students will work in teams of two. Objective In this lab, the student will learn the following
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign configure basic ap security

Edit your configure basic ap security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your configure basic ap security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit configure basic ap security online
Use the instructions below to start using our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit configure basic ap security. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out configure basic ap security

To fill out and configure basic ap security, follow these steps:
01
Start by accessing the administration interface of your access point (AP). This can usually be done by typing the AP's IP address into your web browser.
02
Once logged in, locate the wireless settings or security settings section. The exact location may vary depending on the AP manufacturer and model.
03
Choose the type of security protocol you want to enable. The most common options are WEP, WPA, and WPA2. WPA2 is considered the most secure and is recommended.
04
Set a strong password or passphrase for your wireless network. Avoid using easily guessable information like your name or address. Use a combination of uppercase and lowercase letters, numbers, and special characters for added security.
05
Enable encryption for your AP's security. Options like AES or TKIP are commonly available. AES is the more secure option, so it is advisable to select it if possible.
06
If your AP supports it, enable MAC address filtering. This feature allows you to specify which devices can connect to your network based on their unique MAC addresses. Add the MAC addresses of your trusted devices to the allowed list.
07
Disable SSID broadcast to make your wireless network less visible to outsiders. This will prevent your network from appearing on the list of available networks on other devices. However, note that this will not guarantee complete invisibility.
08
Review and save your settings. Each AP interface will have a different method for confirming and applying the changes. Make sure to save your configurations to apply them successfully.
8.1
Anyone who owns or manages a wireless network should configure basic AP security. Whether you are a homeowner, a small business owner, or in charge of a large enterprise network, securing your AP is crucial. Without proper security measures, your wireless network can be vulnerable to unauthorized access, data theft, and other cyber threats. By configuring basic AP security, you can protect your network and the devices connected to it from potential attacks and maintain the privacy of your data. So, whether it is for personal use or a professional setting, everyone who uses a wireless network needs to configure basic AP security.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit configure basic ap security on an iOS device?
Yes, you can. With the pdfFiller mobile app, you can instantly edit, share, and sign configure basic ap security on your iOS device. Get it at the Apple Store and install it in seconds. The application is free, but you will have to create an account to purchase a subscription or activate a free trial.
How do I complete configure basic ap security on an iOS device?
Get and install the pdfFiller application for iOS. Next, open the app and log in or create an account to get access to all of the solution’s editing features. To open your configure basic ap security, upload it from your device or cloud storage, or enter the document URL. After you complete all of the required fields within the document and eSign it (if that is needed), you can save it or share it with others.
How do I complete configure basic ap security on an Android device?
On an Android device, use the pdfFiller mobile app to finish your configure basic ap security. The program allows you to execute all necessary document management operations, such as adding, editing, and removing text, signing, annotating, and more. You only need a smartphone and an internet connection.
Fill out your configure basic ap security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Configure Basic Ap Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















