Get the free Operating system security
Show details
Operating system security Thomas Aura CSEC3400 Information security Alto University, autumn 2015Outline Access control models in operating systems: 1. Windows 2. Unix 3. Alternatives Acknowledgements:
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign operating system security
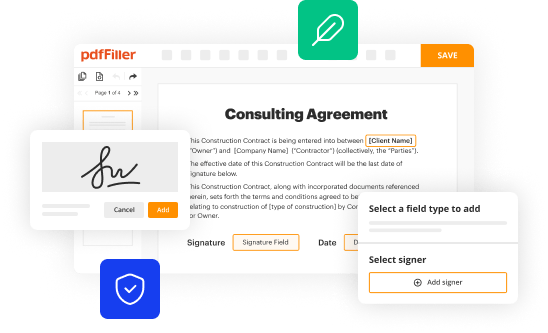
Edit your operating system security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
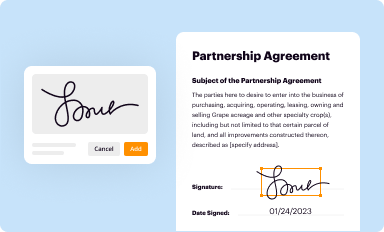
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
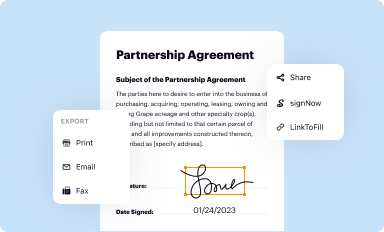
Share your form instantly
Email, fax, or share your operating system security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing operating system security online
Use the instructions below to start using our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit operating system security. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out operating system security
How to fill out operating system security
01
Start by identifying the security requirements of the operating system. This includes understanding the potential threats and vulnerabilities that the system may face.
02
Implement strong authentication mechanisms such as passwords, biometrics, or multi-factor authentication to ensure only authorized users can access the operating system.
03
Regularly update and patch the operating system with the latest security updates to fix any known vulnerabilities.
04
Use firewalls and intrusion detection systems to monitor and analyze network traffic, blocking any suspicious or malicious activity.
05
Encrypt sensitive data to protect it from unauthorized access. This includes using techniques such as disk encryption or secure communication protocols.
06
Enable auditing and logging features to keep track of system activities. This can help in detecting and investigating any security incidents.
07
Train users on secure computing practices and educate them about potential risks and how to avoid them.
08
Regularly perform security assessments and penetration tests to identify and fix any security weaknesses in the operating system.
09
Implement access control policies to restrict user privileges and permissions based on the principle of least privilege.
10
Establish a comprehensive incident response plan to quickly and effectively respond to any security incidents or breaches.
Who needs operating system security?
01
Operating system security is needed by anyone who uses a computer with an operating system. This includes individuals, businesses, organizations, and government agencies.
02
It is especially important for organizations and businesses that store sensitive data, as a security breach can result in financial loss, reputational damage, and legal consequences.
03
Government agencies handle critical and confidential information, making operating system security essential to protect national security and citizen privacy.
04
Individuals also need operating system security to protect their personal information, financial transactions, and online activities from potential threats and cybercriminals.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit operating system security online?
With pdfFiller, it's easy to make changes. Open your operating system security in the editor, which is very easy to use and understand. When you go there, you'll be able to black out and change text, write and erase, add images, draw lines, arrows, and more. You can also add sticky notes and text boxes.
Can I sign the operating system security electronically in Chrome?
Yes. By adding the solution to your Chrome browser, you may use pdfFiller to eSign documents while also enjoying all of the PDF editor's capabilities in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a photo of your handwritten signature using the extension. Whatever option you select, you'll be able to eSign your operating system security in seconds.
Can I create an eSignature for the operating system security in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your operating system security directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
What is operating system security?
Operating system security refers to the measures put in place to protect the operating system from unauthorized access, malware, and other threats.
Who is required to file operating system security?
Anyone using a computer system with an operating system is required to implement operating system security measures.
How to fill out operating system security?
Operating system security can be filled out by implementing firewalls, antivirus software, regular updates, and user access control.
What is the purpose of operating system security?
The purpose of operating system security is to ensure the confidentiality, integrity, and availability of the resources on the system.
What information must be reported on operating system security?
Information on the security measures implemented, any incidents or breaches, and any updates or changes made to the system.
Fill out your operating system security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Operating System Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.